Connecting to an Ethernet LAN
In addition to understanding the components of an Ethernet LAN and the standards that govern its architecture, you need to understand the connection components of an Ethernet LAN. This section describes the connection components of an Ethernet LAN, including network interface cards (NIC) and cable.
Ethernet Network Interface Cards
A NIC is a printed circuit board that provides network communication capabilities to and from a personal computer on a network. Figure 3-10 shows an example of a NIC.
Figure 3-10.Network Interface Card
Also called a LAN adapter, the NIC plugs into a motherboard and provides a port for connecting to the network. The NIC constitutes the computer interface with the LAN.
The NIC communicates with the network through a serial connection, and with the computer through a parallel connection. When a NIC is installed in a computer, it requires an interrupt request line (IRQ), an input/output (I/O) address, a memory space within the operating system (such as DOS or Windows), and drivers (software) that allow it to perform its function. An IRQ is a signal that informs a central processing unit (CPU) that an event needing its attention has occurred. An IRQ is sent over a hardware line to the microprocessor. An example of an interrupt request being issued is when a key is pressed on a keyboard, and the CPU must move the character from the keyboard to RAM. An I/O address is a location in memory used by an auxiliary device to enter data into or retrieve data from a computer.
The MAC address is burned onto each NIC by the manufacturer, providing a unique, physical network address.
Ethernet Media and Connection Requirements
Distance and time dictate the type of Ethernet connections required. This section describes the cable and connector specifications used to support Ethernet implementations.
The cable and connector specifications used to support Ethernet implementations are derived from the EIA/TIA standards body. The categories of cabling defined for Ethernet are derived from the EIA/TIA-568 (SP-2840) Commercial Building Telecommunications Wiring Standards. EIA/TIA specifies an RJ-45 connector for unshielded twisted-pair (UTP) cable.
The important difference to note is the media used for 10-Mbps Ethernet versus 100-Mbps Fast Ethernet. In networks today, where you see a mix of 10- and 100-Mbps requirements, you must be aware of the need to change over to UTP Category 5 to support Fast Ethernet.
Connection Media
Several types of connection media can be used in an Ethernet LAN implementation. Figure 3-11 shows typical connection types.
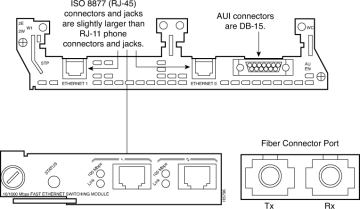
Figure 3-11.Connection Types
The most common type of connection media is the RJ-45 connector and jack illustrated in Figure 3-11. The letters RJ stand for registered jack, and the number “45” refers to a specific physical connector that has eight conductors.
A Gigabit Interface Converter (GBIC), shown in Figure 3-12, is a hot-swappable I/O device that plugs into a Gigabit Ethernet port. A key benefit of using a GBIC is that it is interchangeable, allowing you the flexibility to deploy other 1000BASE-X technology without having to change the physical interface or model on the router or switch. GBICs support UTP (copper) and fiber-optic media for Gigabit Ethernet transmission.
Figure 3-12.1000BASE-T GBIC
Typically, GBICs are used in the LAN for uplinks and are normally used for the backbone. GBICs are also seen in remote networks.
The fiber-optic GBIC, shown in Figure 3-13, is a transceiver that converts serial electric currents to optical signals and converts optical signals to digital electric currents.
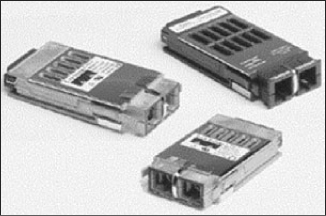
Figure 3-13.Fiber GBIC
Optical GBICs include these types:
- Short wavelength (1000BASE-SX)
- Long wavelength/long haul (1000BASE-LX/LH)
- Extended distance (1000BASE-ZX)
Unshielded Twisted-Pair Cable
Twisted-pair is a copper wire–based cable that can be either shielded or unshielded. UTP cable is frequently used in LANs. Figure 3-14 shows an example of a UTP cable.
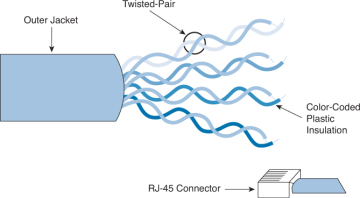
Figure 3-14.UTP Cable
UTP cable is a four-pair wire. Each of the eight individual copper wires in UTP cable is covered by an insulating material. In addition, the wires in each pair are twisted around each other. The advantage of UTP cable is its ability to cancel interference, because the twisted wire pairs limit signal degradation from electromagnetic interference (EMI) and radio frequency interference (RFI). To further reduce crosstalk between the pairs in UTP cable, the number of twists in the wire pairs varies. Both UTP and shielded twisted-pair (STP) cable must follow precise specifications regarding how many twists or braids are permitted per meter.
UTP cable is used in a variety of types of networks. When used as a network medium, UTP cable has four pairs of either 22- or 24-gauge copper wire. UTP used as a network medium has an impedance of 100 ohms, differentiating it from other types of twisted-pair wiring, such as that used for telephone wiring. Because UTP cable has an external diameter of approximately 0.43 cm, or 0.17 inches, its small size can be advantageous during installation. Also, because UTP can be used with most major network architectures, it continues to grow in popularity.
Here are the categories of UTP cable:
- Category 1: Used for telephone communications; not suitable for transmitting data
- Category 2: Capable of transmitting data at speeds of up to 4 Mbps
- Category 3: Used in 10BASE-T networks; can transmit data at speeds up to 10 Mbps
- Category 4: Used in Token Ring networks; can transmit data at speeds up to 16 Mbps
- Category 5: Capable of transmitting data at speeds up to 100 Mbps
- Category 5e: Used in networks running at speeds up to 1000 Mbps (1 Gbps)
- Category 6: Consists of four pairs of 24-gauge copper wires, which can transmit data at speeds of up to 1000 Mbps
- Category 6a: Used in networks running at speeds up to 10 Gbps
The most commonly used categories in LAN environments today are Categories 1 (used primarily for telephony), 5, 5e, and 6.
UTP Implementation
For a UTP implementation in a LAN, you must determine the EIA/TIA type of cable needed and also whether to use a straight-through or crossover cable. This topic describes the characteristics and uses of straight-through and crossover cables, as well as the types of connectors used when UTP is implemented in a LAN. Figure 3-15 shows an RJ-45 connector.
Figure 3-15.RJ-45 Connector
If you look at the RJ-45 transparent-end connector, you can see eight colored wires, twisted into four pairs. Four of the wires (two pairs) carry the positive or true voltage and are considered “tip” (T1 through T4); the other four wires carry the inverse of false voltage grounded and are called “ring” (R1 through R4). Tip and ring are terms that originated in the early days of the telephone. Today, these terms refer to the positive and negative wires in a pair. The wires in the first pair in a cable or a connector are designated as T1 and R1, the second pair as T2 and R2, and so on.
The RJ-45 plug is the male component, crimped at the end of the cable. As you look at the male connector from the front, the pin locations are numbered from 8 on the left to 1 on the right.
The jack is the female component in a network device, wall, cubicle partition outlet, or patch panel.
In addition to identifying the correct EIA/TIA category of cable to use for a connecting device (depending on which standard is being used by the jack on the network device), you need to determine which of the following to use:
- A straight-through cable (either T568A or T568B at each end)
- A crossover cable (T568A at one end; T568B at the other)
In Figure 3-16, the RJ-45 connectors on both ends of the cable show all the wires in the same order. If the two RJ-45 ends of a cable are held side by side in the same orientation, the colored wires (or strips or pins) can be seen at each connector end. If the order of the colored wires is the same at each end, the cable type is straight-through.
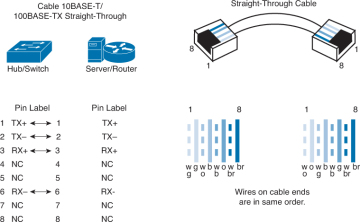
Figure 3-16.Straight-Through Cable
With crossover cables, the RJ-45 connectors on both ends show that some of the wires on one side of the cable are crossed to a different pin on the other side of the cable. Specifically, for Ethernet, pin 1 at one RJ-45 end should be connected to pin 3 at the other end. Pin 2 at one end should be connected to pin 6 at the other end, as shown in the Figure 3-17.
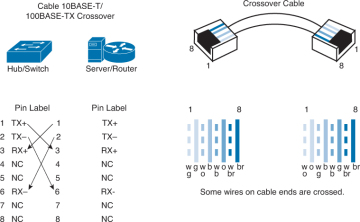
Figure 3-17.Crossover Cable
Figure 3-18 shows the guidelines for choosing which type of cable to use when interconnecting Cisco devices. In addition to verifying the category specification on the cable, you must determine when to use a straight-through or crossover cable.
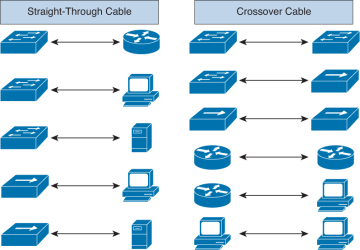
Figure 3-18.When to Use a Straight-Through Cable Versus a Crossover Cable
Use straight-through cables for the following cabling:
- Switch to router
- Switch to PC or server
- Hub to PC or server
Use crossover cables for the following cabling:
- Switch to switch
- Switch to hub
- Hub to hub
- Router to router
- Router Ethernet port to PC NIC
- PC to PC
Auto-MDIX
After reading the previous section, you might be concerned about when you are cabling your network, you might make a critical mistake! Imagine, just one wrong type of cable, and your entire LAN might fail to access key resources. Fortunately, there is great news because of a new technology called Auto-MDIX. Auto-MDIX stands for automatic medium-dependent interface crossover, a feature that lets the interface automatically discover whether the wrong cable is installed. A switch that supports the Auto-MDIX feature detects the wrong cable and causes the switch to swap the pair it uses for transmitting and receiving. This solves the cabling problem, and the switch is able to communicate just fine regardless of the fact that you connected the “wrong” cable. Obviously, this new technology is very desirable and is making its way to more and more Cisco devices all the time.
Optical Fiber
An optical fiber is a flexible, transparent fiber that is made of very pure glass (silica) and is not much bigger in diameter than a human hair. It acts as a waveguide, or “light pipe,” to transmit light between the two ends of the fiber. Optical fibers are widely used in fiber-optic communications, which permit transmission over longer distances and at higher bandwidths (data rates) than other forms of communication. Fibers are used instead of metal wires because signals travel along them with less loss and with immunity to electromagnetic interference. Figure 3-19 shows an example of optical fiber.
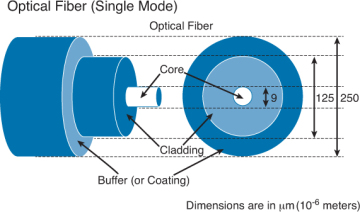
Figure 3-19.Optical Fiber
The two fundamental components that allow a fiber to confine light are the core and the cladding. Most of the light travels from the beginning to the end inside the core. The cladding around the core provides confinement. The diameters of the core and cladding are shown in this illustration, but the core diameter can vary for different fiber types. In this case, the core diameter of 9 µm is very small—the diameter of a human hair is about 50 µm. The outer diameter of the cladding is a standard size of 125 µm. Standardizing the size means that component manufacturers can make connectors for all fiber-optic cables.
The third element in this picture is the buffer (coating), which has nothing to do with the confinement of the light in the fiber. Its purpose is to protect the glass from scratches and moisture. The fiber-optic cable can be easily scratched and broken, like a glass pane. If the fiber is scratched, the scratch could propagate and break the fiber. Another important aspect is the need to keep the fiber dry.
The most significant difference between single-mode fiber (SMF) and multimode fiber (MMF) is in the ability of the fiber to send light for a long distance at high bit rates. In general, MMF is used for shorter distances at a lower bit rate than SMF. For long-distance communications, SMF is preferred. There are many variations of fiber for both MMF and SMF. Figure 3-20 shows the two fiber types.
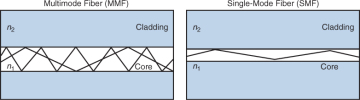
Figure 3-20.Fiber-Optic Types
The most significant physical difference is in the size of the core. The glass in the two fibers is the same, and the index of refraction change is similar. The core diameter can make a major difference. The diameter of the fiber cladding is universal for matching fiber ends.
The effect of having different-size cores in fiber is that the two fiber types will support different ways for the light to get through the fiber. The left image illustrates MMF. MMF supports multiple ways for the light from one source to travel through the fiber (the source of the designation “multimode”). Each path can be thought of as a mode.
For SMF, the possible ways for light to get through the fiber have been reduced to one, a “single mode.” It is not exactly one, but that is a useful approximation. Table 3-1 summarizes the characteristics of MMF and SMF.
Table 3-1. Summarizing MMF and SMF Characteristics
|
MMF Characteristics |
SMF Characteristics |
|
LED transmitter usually used |
Larger transmitter usually used |
|
Lower bandwidth and speed |
Higher bandwidth and speed |
|
Shorter distances |
Longer distances |
|
Less expensive |
More expensive |
An optical fiber connector terminates the end of an optical fiber. A variety of optical fiber connectors are available. The main differences among the types of connectors are dimensions and methods of mechanical coupling. Generally, organizations standardize on one kind of connector, depending on the equipment that they commonly use, or they standardize per type of fiber (one for MMF, one for SMF). Taking into account all the generations of connectors, about 70 connector types are in use today. Figure 3-21 shows some common connector types.
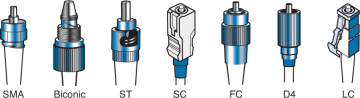
Figure 3-21.Common Fiber-Optic Connector Types
There are three types of connectors:
- Threaded
- Bayonet
- Push-pull
These materials are used for connectors:
- Metal
- Plastic sleeve
Most common connectors are classified as these types:
- ST: Typical for patch panels (for their durability)
- FC: Typical used by service providers for patch panels
- SC: Typical for enterprise equipment
- LC: Typical for enterprise equipment, commonly used on Small Form-Factor Pluggable (SFP) modules
In data communications and telecommunications applications today, small-form-factor connectors (for example, LCs) are replacing the traditional connectors (for example, SCs), mainly to pack more connectors on the faceplate and thus reduce system footprints.