VLAN Segmentation (3.1)
One way of breaking a larger network into smaller sections is by implementing VLANs. VLANs allow segmentation, or breaking a large network into smaller ones.
VLAN Definitions (3.1.1.1)
Within a switched internetwork, VLANs provide segmentation and organizational flexibility. VLANs provide a way to group devices within a LAN. A group of devices within a VLAN communicate as if they were attached to the same wire. VLANs are based on logical connections, instead of physical connections.
VLANs allow an administrator to segment networks based on factors such as function, project team, or application, without regard for the physical location of the user or device as shown in Figure 3-1. Devices within a VLAN act as if they are in their own independent network, even if they share a common infrastructure with other VLANs. Any switch port can belong to a VLAN, and unicast, broadcast, and multicast packets are forwarded and flooded only to end stations within the VLAN where the packets are sourced. Each VLAN is considered a separate logical network, and packets destined for stations that do not belong to the VLAN must be forwarded through a device that supports routing.
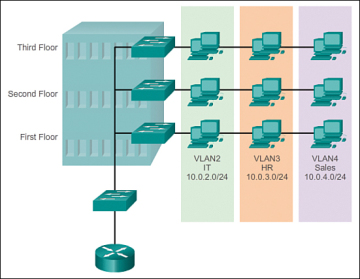
Figure 3-1 VLAN Groups
A VLAN creates a logical broadcast domain that can span multiple physical LAN segments. VLANs improve network performance by separating large broadcast domains into smaller ones. If a device in one VLAN sends a broadcast Ethernet frame, all devices in the VLAN receive the frame, but devices in other VLANs do not.
VLANs enable the implementation of access and security policies according to specific groupings of users. Each switch port can be assigned to only one VLAN (with the exception of a port connected to an IP phone or to another switch).
Benefits of VLANs (3.1.1.2)
User productivity and network adaptability are important for business growth and success. VLANs make it easier to design a network to support the goals of an organization. The primary benefits of using VLANs are as follows:
Security: Groups that have sensitive data are separated from the rest of the network, decreasing the chances of confidential information breaches. As shown in Figure 3-2, faculty computers are on VLAN 10 and completely separated from student and guest data traffic.
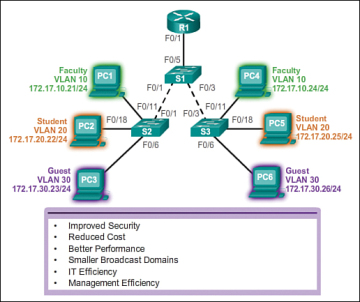
Figure 3-2 Benefits of VLANs
- Cost reduction: Cost savings result from reduced need for expensive network upgrades and more efficient use of existing bandwidth and uplinks.
- Better performance: Dividing flat Layer 2 networks into multiple logical workgroups (broadcast domains) reduces unnecessary traffic on the network and boosts performance.
- Shrink broadcast domains: Dividing a network into VLANs reduces the number of devices in the broadcast domain. As shown in Figure 3-2, there are six computers on this network, but there are three broadcast domains: Faculty, Student, and Guest.
- Improved IT staff efficiency: VLANs make it easier to manage the network because users with similar network requirements share the same VLAN. When a new switch is provisioned, all the policies and procedures already configured for the particular VLAN are implemented when the ports are assigned. It is also easy for the IT staff to identify the function of a VLAN by giving it an appropriate name. In Figure 3-2, for easy identification VLAN 10 has been named “Faculty,” VLAN 20 is named “Student,” and VLAN 30 “Guest.”
- Simpler project and application management: VLANs aggregate users and network devices to support business or geographic requirements. Having separate functions makes managing a project or working with a specialized application easier; an example of such an application is an e-learning development platform for faculty.
Each VLAN in a switched network corresponds to an IP network; therefore, VLAN design must take into consideration the implementation of a hierarchical network addressing scheme. A hierarchical network addressing scheme means that IP network numbers are applied to network segments or VLANs in an orderly fashion that takes the network as a whole into consideration. Blocks of contiguous network addresses are reserved for and configured on devices in a specific area of the network, as shown in Figure 3-2.
Types of VLANs (3.1.1.3)
There are a number of distinct types of VLANs used in modern networks. Some VLAN types are defined by traffic classes. Other types of VLANs are defined by the specific function that they serve.
Data VLAN
A data VLAN is a VLAN that is configured to carry user-generated traffic. A VLAN carrying voice or management traffic would not be part of a data VLAN. It is common practice to separate voice and management traffic from data traffic. A data VLAN, is sometimes referred to as a user VLAN. Data VLANs are used to separate the network into groups of users or devices.
Default VLAN
All switch ports become a part of the default VLAN after the initial boot up of a switch loading the default configuration. Switch ports that participate in the default VLAN are part of the same broadcast domain. This allows any device connected to any switch port to communicate with other devices on other switch ports. The default VLAN for Cisco switches is VLAN 1. In Figure 3-3, the show vlan brief command was issued on a switch running the default configuration. Notice that all ports are assigned to VLAN 1 by default.
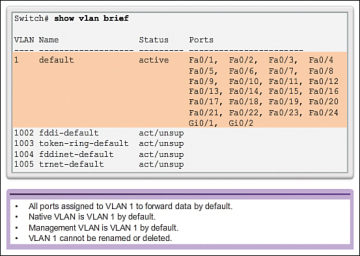
Figure 3-3 Default VLAN 1
VLAN 1 has all the features of any VLAN, except it cannot be renamed or deleted. By default, all Layer 2 control traffic is associated with VLAN 1. In Figure 3-3, all ports are currently assigned to the default VLAN 1.
Native VLAN
A native VLAN is assigned to an 802.1Q trunk port. Trunk ports are the links between switches that support the transmission of traffic associated with more than one VLAN. An 802.1Q trunk port supports traffic coming from many VLANs (tagged traffic), as well as traffic that does not come from a VLAN (untagged traffic). The 802.1Q trunk port places untagged traffic on the native VLAN, which by default is VLAN 1.
Native VLANs are defined in the IEEE 802.1Q specification to maintain backward compatibility with untagged traffic common to legacy LAN scenarios. A native VLAN serves as a common identifier on opposite ends of a trunk link.
It is a best practice to configure the native VLAN as an unused VLAN, distinct from VLAN 1 and other VLANs. In fact, it is not unusual to dedicate a fixed VLAN to serve the role of the native VLAN for all trunk ports in the switched domain. Look at Figure 3-4.
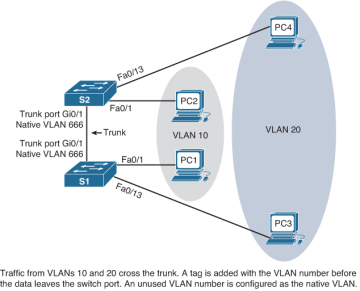
Figure 3-4 Native VLAN
PC1 and PC2 are in VLAN 10. PC3 and PC4 are in VLAN 20. Traffic from both VLANs crosses the trunk link that is configured between the two switches. If PC1 was sending traffic to PC2, as the data leaves the S1 Gi0/1 port, the S1 switch would “tag” the traffic with VLAN 10. When S2 receives the tag, the switch removes it and sends the data on to PC2. The native VLAN should be an unused VLAN, as shown in Figure 3-4. If any devices were configured in the native VLAN, the switches would not tag the traffic before it is placed on the trunk link.
Management VLAN
A management VLAN is any VLAN configured to access the management capabilities of a switch. VLAN 1 is the management VLAN by default. To create the management VLAN, the switch virtual interface (SVI) of that VLAN is assigned an IP address and subnet mask, allowing the switch to be managed via HTTP, Telnet, SSH, or SNMP.
In the past, the management VLAN for a 2960 switch was the only active SVI. On 15.x versions of the Cisco IOS for Catalyst 2960 Series switches, it is possible to have more than one active SVI. With Cisco IOS 15.x, the particular active SVI assigned for remote management must be documented. Although theoretically a switch can have more than one management VLAN, having more than one increases exposure to network attacks.
Voice VLANs (3.1.1.4)
A separate VLAN known as a voice VLAN is needed to support Voice over IP (VoIP). VoIP traffic requires:
- Assured bandwidth to ensure voice quality
- Transmission priority over other types of network traffic
- Capability to be routed around congested areas on the network
- Delay of less than 150 ms across the network
To meet these requirements, the entire network has to be designed to support VoIP. The details of how to configure a network to support VoIP are beyond the scope of this course, but it is useful to summarize how a voice VLAN works between a switch, a Cisco IP phone, and a computer.
In Figure 3-5, VLAN 150 is designed to carry voice traffic. The student computer PC5 is attached to the Cisco IP phone, and the phone is attached to switch S3. PC5 is in VLAN 20, which is used for student data.
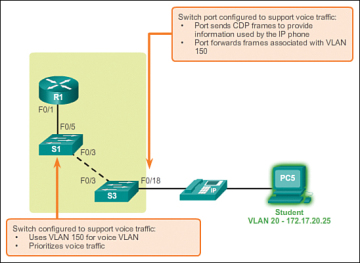
Figure 3-5 Voice VLAN
 Packet Tracer Activity 3.1.1.5: Who Hears the Broadcast?
Packet Tracer Activity 3.1.1.5: Who Hears the Broadcast?