Snooping
According to the Merriam-Webster dictionary, snooping is “to look or pry especially in a sneaking or meddlesome manner.” When we use this term referring to multicast, it means the same thing, with the exception of the meddlesome manner. When a device monitors the conversation or messages sent between devices on the network, we can gain a great deal of information which can be used in turn to tune network behavior to be much more efficient. Over the last several years, Cisco has made great improvements in the intelligence of the components that make up a switch. Switches can now perform Layer 3 services, capture analytics, rewrite information, and so on, all at line rate. This increased intelligence has now provided the capability of a Layer 2 switch to look at more than just the destination MAC address; it offers the capability to look deep into the message and make decisions based on Open Systems Interconnect (OSI) Layer 2 to L7 information.
IGMP Snooping
IGMP snooping is one of those features that does exactly what it says. A network component, generally a Layer 2 switch, monitors frames from devices, and, in this case, it listens specifically for IGMP messages. During the snooping process, the switch listens for IGMP messages from both routers and hosts. After discovering a device and determining which GDA that particular device is interested in, the switch creates an entry in the CAM table that maps the GDA to the interface.
Switches learn about routers using several mechanisms:
IGMP query messages
PIMv1 and/or PIMv2 hellos
Examine Figure 2-10 because it will be used to explain IGMP snooping.
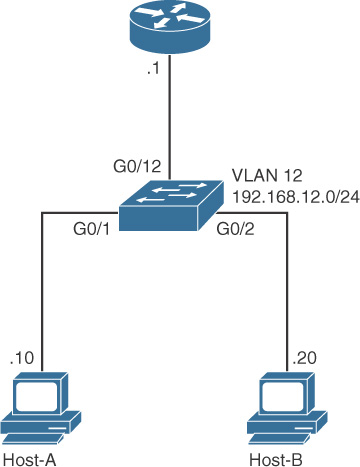
Figure 2-10 IGMP Snooping
Example 2-4 shows a packet capture of an IGMP query report generated from a router.
Example 2-4 IGMP Query Packet Capture
Ethernet Packet: 60 bytes
Dest Addr: 0100.5E00.0001, Source Addr: 0C85.2545.9541
Protocol: 0x0800
IP Version: 0x4, HdrLen: 0x6, TOS: 0xC0 (Prec=Internet Contrl)
Length: 32, ID: 0x1FC5, Flags-Offset: 0x0000
TTL: 1, Protocol: 2 (IGMP), Checksum: 0x57A8 (OK)
Source: 192.168.12.1, Dest: 224.0.0.1
Options: Length = 4
Router Alert Option: 94 0000
IGMP VersionType: 0x11, Max Resp: 0x64, Checksum: 0xEE9B (OK)
Version 2 Membership Query
Group Address: 0.0.0.0
When the switch determines there is a router attached, it places an entry in the IGMP snooping table that specifies the interface, as Example 2-5 demonstrates.
Example 2-5 IGMP Snooping Table
Switch#show ip igmp snooping mrouter
Vlan ports
---- -----
12 Gi0/12(dynamic)
In this case, the switch has learned that a router is attached to interface g0/12. This interface is known as the mrouter port or multicast router port. The mrouter port is essentially a port that the switch has discerned is connected to a multicast enabled router that can process IGMP and PIM messages on behalf of connected hosts. An IGMP-enabled VLAN or segment should always have an mrouter port associated with it. We can also see the effect using the debug ip igmp snooping router command, which gives us greater insight into the process, as Example 2-6 demonstrates.
Example 2-6 debug ip igmp snooping router Output
Switch#debug ip igmp snooping router
router debugging is on
01:49:07: IGMPSN: router: Received non igmp pak on Vlan 12, port Gi0/12
01:49:07: IGMPSN: router: PIMV2 Hello packet received in 12
01:49:07: IGMPSN: router: Is not a router port on Vlan 12, port Gi0/12
01:49:07: IGMPSN: router: Created router port on Vlan 12, port Gi0/12
01:49:07: IGMPSN: router: Learning port: Gi0/12 as rport on Vlan 12
As you see from the output in Example 2-6, the switch received a PIMv2 hello packet from interface Gi0/12 and changed the state of the port to a router port.
When a host connected to the switch wants to join a multicast stream, it sends an IGMP membership report. In Example 2-7, the host connected to port Gi0/2 is interested in receiving data from 224.64.7.7. Using the debug ip igmp snooping group command, we can monitor the activity.
Example 2-7 debug ip igmp snooping group Output
Switch#debug ip igmp snooping group
router debugging is on
01:58:47: IGMPSN: Received IGMPv2 Report for group 224.64.7.7 received on Vlan 12,
port Gi0/2
01:58:47: IGMPSN: group: Adding client ip 192.168.12.20, port_id Gi0/2, on vlan 12
From the output in Example 2-7, we can ascertain that the host connected to Gi0/2 is attempting to connect to the multicast group 224.64.7.7.
Using the show ip igmp snooping groups command, we can also see the entry in the switch, as demonstrated in Example 2-8.
Example 2-8 show ip igmp snooping groups Output
Switch#show ip igmp snooping groups
Vlan Group Type Version Port List
-----------------------------------------------------------------------
12 224.0.1.40 igmp v2 Gi0/12
12 224.64.7.7 igmp v2 Gi0/2, Gi0/12
The output in Example 2-8 specifies the VLAN, multicast group, IGMP version, and ports associated with each group.
The packet capture in Example 2-9 shows the membership report generated from the host with the MAC address of 0x000F.F7B1.67E0. Notice how the destination MAC and destination IP are those of the multicast group the host is interested in receiving. The IGMP snooped mrouter port entry ensures this IGMP membership report is forwarded to the multicast router for processing, if necessary. See the next section on maintaining group membership.
Example 2-9 IGMP Membership Report Packet Capture
Ethernet Packet: 60 bytes
Dest Addr: 0100.5E40.0707, Source Addr: 000F.F7B1.67E0
Protocol: 0x0800
IP Version: 0x4, HdrLen: 0x5, TOS: 0xC0 (Prec=Internet Contrl)
Length: 28, ID: 0x0000, Flags-Offset: 0x0000
TTL: 1, Protocol: 2 (IGMP), Checksum: 0x051D (OK)
Source: 192.168.12.20, Dest: 224.64.7.7
IGMP VersionType: 0x16, Max Resp: 0x00, Checksum: 0x02B8 (OK)
Version 2 Membership Report
Group Address: 224.64.7.7
The output in Example 2-10 shows several hosts connecting to the multicast group.
Example 2-10 show ip igmp snooping groups Output
Switch#show ip igmp snooping groups
Vlan Group Type Version Port List
-----------------------------------------------------------------------
12 224.0.1.40 igmp v2 Gi0/15
12 224.64.7.7 igmp v2 Gi0/1, Gi0/2,
Gi0/4, Gi0/15
Maintaining Group Membership
As hosts are added to or removed from the multicast group, the switch manages the interaction. The switch does not notify the router of any additions or removals to the group, with the exception of the last host. If there is only one host and it leaves the multicast group, the switch immediately sends a group leave message to the upstream router. One of the interesting aspects of this message is that the switch spoofs the IP address of the last client. Look carefully at the output in Example 2-11.
Example 2-11 IGMP Leave Capture Output
Ethernet Packet: 60 bytes
Dest Addr: 0100.5E00.0002, Source Addr: 0013.19C6.A60F
Protocol: 0x0800
IP Version: 0x4, HdrLen: 0x6, TOS: 0xC0 (Prec=Internet Contrl)
Length: 32, ID: 0x0000, Flags-Offset: 0x0000
TTL: 1, Protocol: 2 (IGMP), Checksum: 0x7745 (OK)
Source: 192.168.12.40, Dest: 224.0.0.2
Options: Length = 4
Router Alert Option: 94 0000
IGMP VersionType: 0x17, Max Resp: 0x00, Checksum: 0x01B8 (OK)
Version 2 Leave Group
Group Address: 224.64.7.7
The benefit of this behavior is that when the last device leaves the multicast group, the router does not have to wait for a timeout. Notice also that the MAC address of the source in the packet in Example 2-11 is the MAC address of the switch as depicted in the show interface Gi0/12 output in Example 2-12. This is the mrouter interface for this segment.
Example 2-12 show interface Output
Switch#show interface Gi0/12
GigabitEthernet0/12 is up, line protocol is up
Hardware is Gigabit Ethernet, address is 0013.19C6.A60F (bia 0013.19C6.A60F)
MTU 1500 bytes, BW 10000 Kbit/sec, DLY 1000 usec,
Configuring IP IGMP Snooping
The configuration could not be easier for newer Catalyst or Nexus product switches. The command is as follows:
C2970(config)#ip igmp snooping
Here is the best part—it is on by default and obviously not necessary to type the previous command. You can confirm that IGMP snooping is functional and verify the specific operating parameters with the show ip igmp snooping command, as demonstrated in Example 2-13.
Example 2-13 Confirming IGMP Snooping Functionality and Parameters
Switch#show ip igmp snooping
Global IGMP Snooping configuration:
-------------------------------------------
IGMP snooping : Enabled
IGMPv3 snooping (minimal) : Enabled
Report suppression : Enabled
TCN solicit query : Disabled
TCN flood query count : 2
Robustness variable : 2
Last member query count : 2
Last member query interval : 1000
The output was truncated for brevity, but the IGMP snooping information will be displayed per VLAN.