Selecting a WAN Technology (1.2)
In this section, you learn how to select WAN access technologies to satisfy business requirements.
WAN Services (1.2.1)
In this topic, you learn about different WAN services available.
WAN Link Connection Options (1.2.1.1)
ISPs can use are several WAN access connection options to connect the local loop to the enterprise edge. These WAN access options differ in technology, speed, and cost. Each has distinct advantages and disadvantages. Familiarity with these technologies is an important part of network design.
As shown in Figure 1-17 and described in the list that follows, an enterprise can get WAN access in two ways.
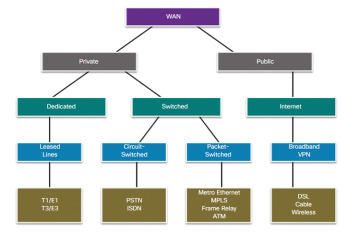
Figure 1-17 WAN Access Options
Private WAN infrastructure: Service providers may offer dedicated point-to-point leased lines, circuit-switched links, such as PSTN or ISDN, and packet-switched links, such as Ethernet WAN, ATM, or Frame Relay.
Public WAN infrastructure: Service providers provide Internet access using broadband services such as DSL, cable, and satellite access. Broadband connections are typically used to connect small offices and telecommuting employees to a corporate site over the Internet. Data traveling between corporate sites over the public WAN infrastructure should be protected using VPNs.
The topology in Figure 1-18 illustrates some of these WAN access technologies.
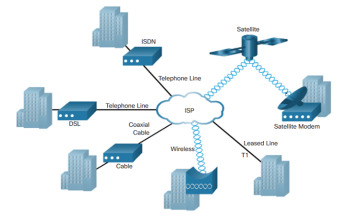
Figure 1-18 WAN Access Technologies
Service Provider Network Infrastructure (1.2.1.2)
When a WAN service provider receives data from a client at a site, it must forward the data to the remote site for final delivery to the recipient. In some cases, the remote site may be connected to the same service provider as the originating site. In other cases, the remote site may be connected to a different ISP, and the originating ISP must pass the data to the connecting ISP.
Long-range communications are usually those connections between ISPs, or between branch offices in very large companies.
Service provider networks are complex. They consist mostly of high-bandwidth fiber-optic media, using either the Synchronous Optical Networking (SONET) or Synchronous Digital Hierarchy (SDH) standard. These standards define how to transfer multiple data, voice, and video traffic over optical fiber using lasers or light-emitting diodes (LEDs) over great distances.
A newer fiber-optic media development for long-range communications is called dense wavelength division multiplexing (DWDM). DWDM multiplies the amount of bandwidth that a single strand of fiber can support, as illustrated in Figure 1-19.
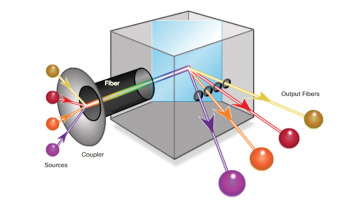
Figure 1-19 DWDM
DWDM enables long-range communication in several ways:
DWDM enables bidirectional (for example, two-way) communications over one strand of fiber.
It can multiplex more than 80 different channels of data (that is, wavelengths) onto a single fiber.
Each channel is capable of carrying a 10 Gb/s multiplexed signal.
It assigns incoming optical signals to specific wavelengths of light (that is, frequencies).
It can amplify these wavelengths to boost the signal strength.
It supports SONET and SDH standards.
DWDM circuits are used in all modern submarine communications cable systems and other long-haul circuits, as illustrated in Figure 1-20.
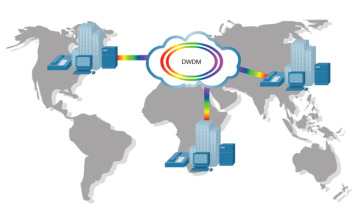
Figure 1-20 Service Provider Networks Use DWDM
Private WAN Infrastructures (1.2.2)
In this topic, you compare private WAN technologies.
Leased Lines (1.2.2.1)
When permanent dedicated connections are required, a point-to-point link is used to provide a pre-established WAN communications path from the customer premises to the provider network. Point-to-point lines are usually leased from a service provider and are called leased lines.
Leased lines have existed since the early 1950s; for this reason, they are referred to by different names such as leased circuits, serial link, serial line, point-to-point link, and T1/E1 or T3/E3 lines.
The term leased line refers to the fact that the organization pays a monthly lease fee to a service provider to use the line. Leased lines are available in different capacities and are generally priced based on the bandwidth required and the distance between the two connected points.
In North America, service providers use the T-carrier system to define the digital transmission capability of a serial copper media link, while Europe uses the E-carrier system, as shown in Figure 1-21. For instance, a T1 link supports 1.544 Mb/s, an E1 supports 2.048 Mb/s, a T3 supports 43.7 Mb/s, and an E3 connection supports 34.368 Mb/s. Optical carrier (OC) transmission rates are used to define the digital transmitting capacity of a fiber-optic network.
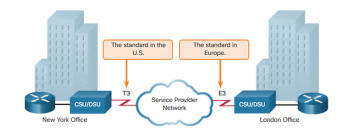
Figure 1-21 Sample Leased-Line Topology
Table 1-1 describes the advantages and disadvantages of using leased lines.
Table 1-1 Advantages/Disadvantages of Leased Lines
| Advantages | Disadvantages |
|---|---|
| Simplicity: Point-to-point communication links require minimal expertise to install and maintain. | Cost: Point-to-point links are generally the most expensive type of WAN access. The cost of leased-line solutions can become significant when they are used to connect many sites over increasing distances. In addition, each endpoint requires an interface on the router, which increases equipment costs. |
| Quality: Point-to-point communication links usually offer high service quality, if they have adequate bandwidth. The dedicated capacity removes latency or jitter between the endpoints. | Limited flexibility: WAN traffic is often variable, and leased lines have a fixed capacity, so the bandwidth of the line seldom matches the need exactly. Any change to the leased line generally requires a site visit by ISP personnel to adjust capacity. |
| Availability: Constant availability is essential for some applications, such as e-commerce. Point-to-point communication links provide permanent, dedicated capacity, which is required for VoIP or Video over IP. |
The Layer 2 protocol is usually HDLC or PPP.
Dialup (1.2.2.2)
Dialup WAN access may be required when no other WAN technology is available. For example, a remote location could use modems and analog dialed telephone lines to provide low capacity and dedicated switched connections, as shown in Figure 1-22. Dialup access is suitable when intermittent, low-volume data transfers are needed.
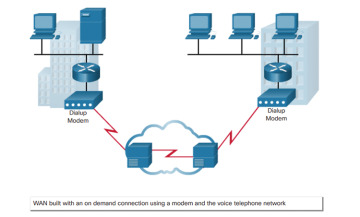
Figure 1-22 Sample Dialup Topology
Traditional telephony uses a copper cable, called the local loop, to connect the telephone handset in the subscriber premises to the CO. The signal on the local loop during a call is a continuously varying electronic signal that is a translation of the subscriber voice into an analog signal.
Traditional local loops can transport binary computer data through the voice telephone network using a dialup modem. The modem modulates the binary data into an analog signal at the source and demodulates the analog signal to binary data at the destination. The physical characteristics of the local loop and its connection to the PSTN limit the rate of the signal to less than 56 kb/s.
For small businesses, these relatively low-speed dialup connections are adequate for the exchange of sales figures, prices, routine reports, and email. Using automatic dialup at night or on weekends for large file transfers and data backup can take advantage of lower off-peak rates. These rates, often referred to as tariffs or toll charges, are based on the distance between the endpoints, time of day, and the duration of the call.
The advantages of modem and analog lines are simplicity, availability, and low implementation cost. The disadvantages are the low data rates and a relatively long connection time. The dedicated circuit has little delay or jitter for point-to-point traffic, but voice or video traffic does not operate adequately at these low bit rates.
ISDN (1.2.2.3)
Integrated Services Digital Network (ISDN) is a circuit-switching technology that enables the local loop of a PSTN to carry digital signals, resulting in higher capacity switched connections.
ISDN changes the internal connections of the PSTN from carrying analog signals to time-division multiplexed (TDM) digital signals. TDM allows two or more signals, or bit streams, to be transferred as subchannels in one communication channel. The signals appear to transfer simultaneously; but physically, the signals are taking turns on the channel.
Figure 1-23 displays a sample ISDN topology. The ISDN connection may require a terminal adapter (TA), which is a device used to connect ISDN Basic Rate Interface (BRI) connections to a router.
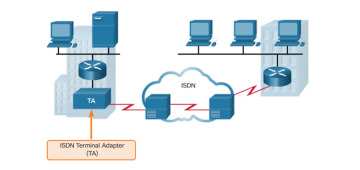
Figure 1-23 Sample ISDN Topology
The two types of ISDN interfaces are as follows:
Basic Rate Interface (BRI): ISDN BRI is intended for the home and small enterprise and provides two 64 kb/s bearer channels (B) for carrying voice and data and a 16 kb/s delta channel (D) for signaling, call setup, and other purposes. The BRI D channel is often underused because it has only two B channels to control (see Figure 1-24).

Figure 1-24 ISDN BRI
Primary Rate Interface (PRI): ISDN is also available for larger installations. In North America, PRI delivers 23 B channels with 64 kb/s and one D channel with 64 kb/s for a total bit rate of up to 1.544 Mb/s. This includes some additional overhead for synchronization. In Europe, Australia, and other parts of the world, ISDN PRI provides 30 B channels and one D channel, for a total bit rate of up to 2.048 Mb/s, including synchronization overhead (see Figure 1-25).
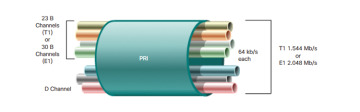
Figure 1-25 ISDN PRI
BRI has a call setup time that is less than a second, and the 64 kb/s B channel provides greater capacity than an analog modem link. In comparison, the call setup time of a dialup modem is approximately 30 or more seconds with a theoretical maximum of 56 kb/s. With ISDN, if greater capacity is required, a second B channel can be activated to provide a total of 128 kb/s. This permits several simultaneous voice conversations, a voice conversation and data transfer, or a video conference using one channel for voice and the other for video.
Another common application of ISDN is to provide additional capacity as needed on a leased-line connection. The leased line is sized to carry average traffic loads while ISDN is added during peak demand periods. ISDN is also used as a backup if the leased line fails. ISDN tariffs are based on a per-B channel basis and are similar to those of analog voice connections.
With PRI ISDN, multiple B channels can be connected between two endpoints. This allows for videoconferencing and high-bandwidth data connections with no latency or jitter. However, multiple connections can be very expensive over long distances.
Frame Relay (1.2.2.4)
Frame Relay is a simple Layer 2 nonbroadcast multi-access (NBMA) WAN technology used to interconnect enterprise LANs. A single router interface can be used to connect to multiple sites using permanent virtual circuits (PVCs). PVCs are used to carry both voice and data traffic between a source and destination, and support data rates up to 4 Mb/s, with some providers offering even higher rates.
An edge router requires only a single interface, even when multiple VCs are used. The leased line to the Frame Relay network edge allows cost-effective connections between widely scattered LANs.
Frame Relay creates PVCs, which are uniquely identified by a data-link connection identifier (DLCI). The PVCs and DLCIs ensure bidirectional communication from one DTE device to another.
For instance, in Figure 1-26, R1 will use DLCI 102 to reach R2 while R2 will use DLCI 201 to reach R1.
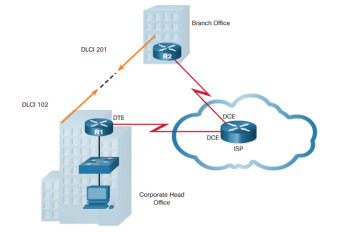
Figure 1-26 Sample Frame Relay Topology
ATM (1.2.2.5)
Asynchronous Transfer Mode (ATM) technology is capable of transferring voice, video, and data through private and public networks. It is built on a cell-based architecture rather than on a frame-based architecture. ATM cells are always a fixed length of 53 bytes. The ATM cell contains a 5-byte ATM header followed by 48 bytes of ATM payload. Small, fixed-length cells are well suited for carrying voice and video traffic because this traffic is intolerant of delay. Video and voice traffic do not have to wait for larger data packets to be transmitted, as shown in Figure 1-27.
The 53-byte ATM cell is less efficient than the bigger frames and packets of Frame Relay. Furthermore, the ATM cell has at least 5 bytes of overhead for each 48-byte payload. When the cell is carrying segmented network layer packets, the overhead is higher because the ATM switch must be able to reassemble the packets at the destination. A typical ATM line needs almost 20 percent greater bandwidth than Frame Relay to carry the same volume of network layer data.
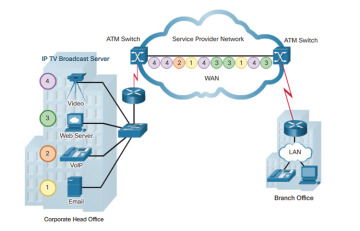
Figure 1-27 Sample ATM Topology
ATM was designed to be extremely scalable and to support link speeds of T1/E1 to OC-12 (622 Mb/s) and faster.
As with other shared technologies, ATM allows multiple VCs on a single leased-line connection to the network edge.
Ethernet WAN (1.2.2.6)
Ethernet was originally developed to be a LAN access technology. Originally, Ethernet was not suitable as a WAN access technology because at that time, the maximum cable length was one kilometer. However, newer Ethernet standards using fiber-optic cables have made Ethernet a reasonable WAN access option. For instance, the IEEE 1000BASE-LX standard supports fiber-optic cable lengths of 5 km, while the IEEE 1000BASE-ZX standard supports cable lengths up to 70 km.
Service providers now offer Ethernet WAN service using fiber-optic cabling. The Ethernet WAN service can go by many names, including Metropolitan Ethernet (MetroE), Ethernet over MPLS (EoMPLS), and Virtual Private LAN Service (VPLS). A sample Ethernet WAN topology is shown in Figure 1-28.

Figure 1-28 Sample Ethernet WAN Topology
An Ethernet WAN offers several benefits:
Reduced expenses and administration: Ethernet WAN provides a switched, high-bandwidth Layer 2 network capable of managing data, voice, and video all on the same infrastructure. This characteristic increases bandwidth and eliminates expensive conversions to other WAN technologies. The technology enables businesses to inexpensively connect numerous sites in a metropolitan area, to each other, and to the Internet.
Easy integration with existing networks: Ethernet WAN connects easily to existing Ethernet LANs, reducing installation costs and time.
Enhanced business productivity: Ethernet WAN enables businesses to take advantage of productivity-enhancing IP applications that are difficult to implement on TDM or Frame Relay networks, such as hosted IP communications, VoIP, and streaming and broadcast video.
MPLS (1.2.2.7)
Multiprotocol Label Switching (MPLS) is a multiprotocol high-performance WAN technology that directs data from one router to the next. MPLS is based on short path labels rather than IP network addresses.
MPLS has several defining characteristics. It is multiprotocol, meaning it has the ability to carry any payload including IPv4, IPv6, Ethernet, ATM, DSL, and Frame Relay traffic. It uses labels that tell a router what to do with a packet. The labels identify paths between distant routers rather than endpoints, and while MPLS actually routes IPv4 and IPv6 packets, everything else is switched.
MPLS is a service provider technology. Leased lines deliver bits between sites, and Frame Relay and Ethernet WAN deliver frames between sites. However, MPLS can deliver any type of packet between sites. MPLS can encapsulate packets of various network protocols. It supports a wide range of WAN technologies including T-carrier/E-carrier links, Carrier Ethernet, ATM, Frame Relay, and DSL.
The sample topology in Figure 1-29 illustrates how MPLS is used. Notice that the different sites can connect to the MPLS cloud using different access technologies.
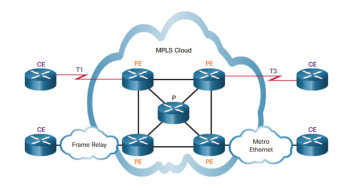
Figure 1-29 Sample MPLS Topology
In the Figure 1-29, CE refers to the customer edge; PE is the provider edge router, which adds and removes labels; and P is an internal provider router, which switches MPLS labeled packets.
VSAT (1.2.2.8)
All private WAN technologies discussed so far used either copper or fiber-optic media. What if an organization needed connectivity in a remote location where no service providers offer WAN service?
Very small aperture terminal (VSAT) is a solution that creates a private WAN using satellite communications. A VSAT is a small satellite dish similar to those used for home Internet and TV. VSATs create a private WAN while providing connectivity to remote locations.
Specifically, a router connects to a satellite dish that is pointed to a service provider’s satellite. This satellite is in geosynchronous orbit in space. The signals must travel approximately 35,786 kilometers (22,236 miles) to the satellite and back.
The example in Figure 1-30 displays a VSAT dish on the roofs of the buildings communicating with a satellite thousands of kilometers away in space.

Figure 1-30 Sample VSAT Topology
Public WAN Infrastructure (1.2.3)
In this topic, you compare public WAN technologies.
DSL (1.2.3.1)
DSL technology is an always-on connection technology that uses existing twisted-pair telephone lines to transport high-bandwidth data, and provides IP services to subscribers. A DSL modem converts an Ethernet signal from the user device to a DSL signal, which is transmitted to the central office.
Multiple DSL subscriber lines are multiplexed into a single, high-capacity link using a DSL access multiplexer (DSLAM) at the provider location referred to as the point of presence (POP). DSLAMs incorporate TDM technology to aggregate many subscriber lines into a single medium, generally a T3 connection. Current DSL technologies use sophisticated coding and modulation techniques to achieve fast data rates.
There is a wide variety of DSL types, standards, and emerging standards. DSL is now a popular choice for enterprise IT departments to support home workers. Generally, a subscriber cannot choose to connect to an enterprise network directly but must first connect to an ISP, and then an IP connection is made through the Internet to the enterprise. Security risks are incurred in this process but can be mediated with security measures.
The topology in Figure 1-31 displays a sample DSL WAN connection.
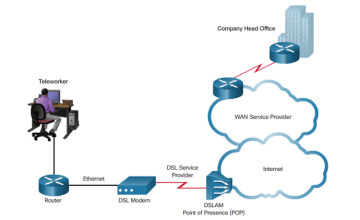
Figure 1-31 Sample DSL Topology
Cable (1.2.3.2)
Coaxial cable is widely used in urban areas to distribute television signals. Network access is available from many cable television providers. This access allows for greater bandwidth than the conventional telephone local loop.
Cable modems (CMs) provide an always-on connection and a simple installation. A subscriber connects a computer or LAN router to the cable modem, which translates the digital signals into the broadband frequencies used for transmitting on a cable television network. The local cable TV office, which is called the cable headend, contains the computer system and databases needed to provide Internet access. The most important component located at the headend is the cable modem termination system (CMTS), which sends and receives digital cable modem signals on a cable network and is necessary for providing Internet services to cable subscribers.
Cable modem subscribers must use the ISP associated with the service provider. All the local subscribers share the same cable bandwidth. As more users join the service, available bandwidth may drop below the expected rate.
The topology in Figure 1-32 displays a sample cable WAN connection.
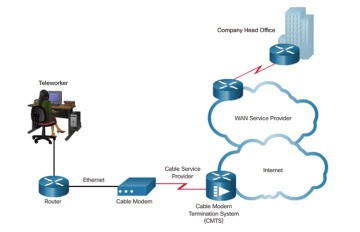
Figure 1-32 Sample Cable Topology
Wireless (1.2.3.3)
Wireless technology uses the unlicensed radio spectrum to send and receive data. The unlicensed spectrum is accessible to anyone who has a wireless router and wireless technology in the device he or she is using.
Until recently, one limitation of wireless access has been the need to be within the local transmission range (typically less than 100 feet) of a wireless router or a wireless modem that has a wired connection to the Internet. The following new developments in broadband wireless technology are changing this situation:
Municipal Wi-Fi: Many cities have begun setting up municipal wireless networks. Some of these networks provide high-speed Internet access for free or for substantially less than the price of other broadband services. Others are for city use only, allowing police and fire departments and other city employees to do certain aspects of their jobs remotely. To connect to a municipal Wi-Fi, a subscriber typically needs a wireless modem, which provides a stronger radio and directional antenna than conventional wireless adapters. Most service providers provide the necessary equipment for free or for a fee, much like they do with DSL or cable modems.
WiMAX: Worldwide Interoperability for Microwave Access (WiMAX) is a new technology that is just beginning to come into use. It is described in the IEEE standard 802.16. WiMAX provides high-speed broadband service with wireless access and provides broad coverage like a cell phone network rather than through small Wi-Fi hotspots. WiMAX operates in a similar way to Wi-Fi, but at higher speeds, over greater distances, and for a greater number of users. It uses a network of WiMAX towers that are similar to cell phone towers. To access a WiMAX network, subscribers must subscribe to an ISP with a WiMAX tower within 30 miles of their location. They also need some type of WiMAX receiver and a special encryption code to get access to the base station.
Satellite Internet: Typically, rural users use this type of technology where cable and DSL are not available. A VSAT provides two-way (upload and download) data communications. The upload speed is about one-tenth of the 500 kb/s download speed. Cable and DSL have higher download speeds, but satellite systems are about 10 times faster than an analog modem. To access satellite Internet services, subscribers need a satellite dish, two modems (uplink and downlink), and coaxial cables between the dish and the modem.
Figure 1-33 displays an example of a WiMAX network.
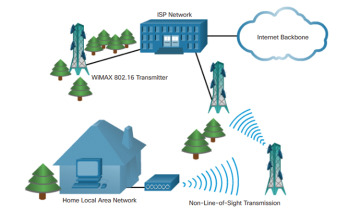
Figure 1-33 Sample Wireless Topology
3G/4G Cellular (1.2.3.4)
Increasingly, cellular service is another wireless WAN technology being used to connect users and remote locations where no other WAN access technology is available, as shown in Figure 1-34. Many users with smartphones and tablets can use cellular data to email, surf the web, download apps, and watch videos.
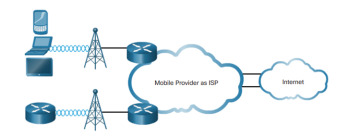
Figure 1-34 Sample Cellular Topology
Phones, tablet computers, laptops, and even some routers can communicate through to the Internet using cellular technology. These devices use radio waves to communicate through a nearby mobile phone tower. The device has a small radio antenna, and the provider has a much larger antenna sitting at the top of a tower somewhere within miles of the phone.
These are two common cellular industry terms:
3G/4G Wireless: Abbreviation for third-generation and fourth-generation cellular access. These technologies support wireless Internet access.
Long-Term Evolution (LTE): Refers to a newer and faster technology and is considered to be part of fourth-generation (4G) technology.
VPN Technology (1.2.3.5)
Security risks are incurred when a teleworker or a remote office worker uses a broadband service to access the corporate WAN over the Internet. To address security concerns, broadband services provide capabilities for using VPN connections to a network device that accepts VPN connections, which are typically located at the corporate site.
A VPN is an encrypted connection between private networks over a public network, such as the Internet. Instead of using a dedicated Layer 2 connection, such as a leased line, a VPN uses virtual connections called VPN tunnels, which are routed through the Internet from the private network of the company to the remote site or employee host.
Using VPN offers several benefits:
Cost savings: VPNs enable organizations to use the global Internet to connect remote offices, and to connect remote users to the main corporate site. This eliminates expensive, dedicated WAN links and modem banks.
Security: VPNs provide the highest level of security by using advanced encryption and authentication protocols that protect data from unauthorized access.
Scalability: Because VPNs use the Internet infrastructure within ISPs and devices, it is easy to add new users. Corporations are able to add large amounts of capacity without adding significant infrastructure.
Compatibility with broadband technology: VPN technology is supported by broadband service providers such as DSL and cable. VPNs allow mobile workers and telecommuters to take advantage of their home high-speed Internet service to access their corporate networks. Business-grade, high-speed broadband connections can also provide a cost-effective solution for connecting remote offices.
There are two types of VPN access:
Site-to-site VPNs: Site-to-site VPNs connect entire networks to each other; for example, they can connect a branch office network to a company headquarters network, as shown in Figure 1-35. Each site is equipped with a VPN gateway, such as a router, firewall, VPN concentrator, or security appliance. In the Figure 1-35, a remote branch office uses a site-to-site-VPN to connect with the corporate head office.
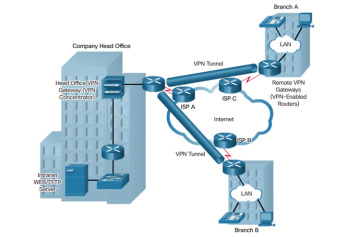
Figure 1-35 Sample Site-to-Site VPN Topology
Remote-access VPNs: Remote-access VPNs enable individual hosts, such as telecommuters, mobile users, and extranet consumers, to access a company network securely over the Internet. Each host (Teleworker 1 and Teleworker 2) typically has VPN client software loaded or uses a web-based client, as shown in Figure 1-36.
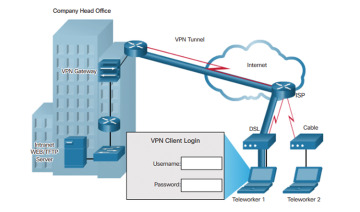
Figure 1-36 Sample Remote-Access VPN Topology
Selecting WAN Services (1.2.4)
In this topic, you learn how to select the appropriate WAN protocol and service for a specific network requirement.
Choosing a WAN Link Connection (1.2.4.1)
There are many important factors to consider when choosing an appropriate WAN connection. For a network administrator to decide which WAN technology best meets the requirements of a specific business, he or she must answer the following questions:
What is the purpose of the WAN?
There are a few issues to consider:
Will the enterprise connect local branches in the same city area, connect remote branches, or connect to a single branch?
Will the WAN be used to connect internal employees, or external business partners and customers, or all three?
Will the enterprise connect to customers, connect to business partners, connect to employees, or some combination of these?
Will the WAN provide authorized users limited or full access to the company intranet?
What is the geographic scope?
There are a few issues to consider:
Is the WAN local, regional, or global?
Is the WAN one-to-one (single branch), one-to-many branches, or many-to-many (distributed)?
What are the traffic requirements?
There are a few issues to consider:
What type of traffic must be supported (data only, VoIP, video, large files, streaming files)? This determines the quality and performance requirements.
What volume of traffic type (voice, video, or data) must be supported for each destination? This determines the bandwidth capacity required for the WAN connection to the ISP.
What Quality of Service is required? This may limit the choices. If the traffic is highly sensitive to latency and jitter, eliminate any WAN connection options that cannot provide the required quality.
What are the security requirements (data integrity, confidentiality, and security)? These are important factors if the traffic is of a highly confidential nature, or if it provides essential services, such as emergency response.
Choosing a WAN Link Connection (Cont.) (1.2.4.2)
In addition to gathering information about the scope of the WAN, the administrator must also determine the following:
Should the WAN use a private or public infrastructure? A private infrastructure offers the best security and confidentiality, whereas the public Internet infrastructure offers the most flexibility and lowest ongoing expense. The choice depends on the purpose of the WAN, the types of traffic it carries, and available operating budget. For example, if the purpose is to provide a nearby branch with high-speed secure services, a private dedicated or switched connection may be best. If the purpose is to connect many remote offices, a public WAN using the Internet may be the best choice. For distributed operations, a combination of options may be the solution.
For a private WAN, should it be dedicated or switched? Real-time, high-volume transactions have special requirements that could favor a dedicated line, such as traffic flowing between the data center and the corporate head office. If the enterprise is connecting to a local single branch, a dedicated leased line could be used. However, that option would become very expensive for a WAN connecting multiple offices. In that case, a switched connection might be better.
For a public WAN, what type of VPN access is required? If the purpose of the WAN is to connect a remote office, a site-to-site VPN may be the best choice. To connect teleworkers or customers, remote-access VPNs are a better option. If the WAN is serving a mixture of remote offices, teleworkers, and authorized customers, such as a global company with distributed operations, a combination of VPN options may be required.
Which connection options are available locally? In some areas, not all WAN connection options are available. In this case, the selection process is simplified, although the resulting WAN may provide less than optimal performance. For example, in a rural or remote area, the only option may be VSAT or cellular access.
What is the cost of the available connection options? Depending on the option chosen, the WAN can be a significant ongoing expense. The cost of a particular option must be weighed against how well it meets the other requirements. For example, a dedicated leased line is the most expensive option, but the expense may be justified if it is critical to ensure secure transmission of high volumes of real-time data. For less demanding applications, a less expensive switched or Internet connection option may be more suitable.
Using the preceding guidelines, as well as those described by the Cisco Enterprise Architecture, a network administrator should be able to choose an appropriate WAN connection to meet the requirements of different business scenarios.
