Fighters in the War Against Cybercrime (1.2)
In this section, you will learn about the Security Operations Center (SOC) and how to become a defender in the cybersecurity arena.
The Modern Security Operations Center (1.2.1)
In this topic, you will learn about the people, processes, and technologies in an SOC.
Elements of an SOC (1.2.1.1)
Defending against today’s threats requires a formalized, structured, and disciplined approach, which is executed by professionals at SOCs. SOCs provide a broad range of services, from monitoring and management, to comprehensive threat solutions and hosted security that can be customized to meet customer needs. SOCs can be wholly in-house, owned and operated by a business, or elements of an SOC can be contracted out to security vendors, such as Cisco’s Managed Security Services.
The major elements of an SOC, shown in Figure 1-1, are people, processes, and technology.
Figure 1-1 Elements of a Security Operations Center
People in the SOC (1.2.1.2)
The SANS Institute (https://www.sans.org) classifies the roles people play in a SOC into four job titles:
Tier 1 Alert Analyst: These professionals monitor incoming alerts, verify that a true incident has occurred, and forward tickets to Tier 2, if necessary.
Tier 2 Incident Responder: These professionals are responsible for deep investigation of incidents and advise remediation or action to be taken.
Tier 3 Subject Matter Expert (SME)/Hunter: These professionals have expert-level skill in network, endpoint, threat intelligence, and malware reverse engineering. They are experts at tracing the processes of the malware to determine its impact and how it can be removed. They are also deeply involved in hunting for potential threats and implementing threat detection tools.
SOC Manager: This professional manages all the resources of the SOC and serves as the point of contact for the larger organization or customer.
This course offers preparation for a certification suitable for the position of Tier 1 Alert Analyst, also known as Cybersecurity Analyst.
Figure 1-2 graphically represents how these roles interact with each other.
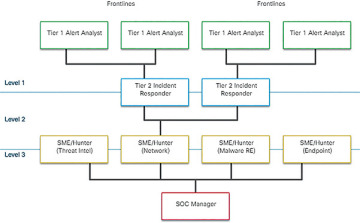
Figure 1-2 Roles of the People in a Security Operations Center
Process in the SOC (1.2.1.3)
The day of a Tier 1 Analyst begins with monitoring security alert queues. A ticketing system is frequently used to allow analysts to select alerts from a queue to investigate. Because the software that generates alerts can trigger false alarms, one job of the Tier 1 Analyst might be to verify that an alert represents a true security incident. When verification is established, the incident can be forwarded to investigators or other security personnel to be acted upon, or resolved as a false alarm.
If a ticket cannot be resolved, the Tier 1 Analyst will forward the ticket to a Tier 2 Analyst for deeper investigation and remediation. If the Tier 2 Analyst cannot resolve the ticket, she will forward it to a Tier 3 Analyst with in-depth knowledge and threat hunting skills.
Figure 1-3 summarizes the roles of Tier 1, Tier 2, and Tier 3 analysts.
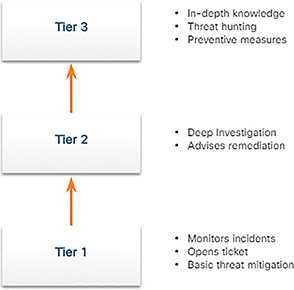
Figure 1-3 Threat Incident Escalation Process
Technologies in the SOC (1.2.1.4)
As shown in Figure 1-4, a SOC needs a security information and event management system (SIEM), or its equivalent. This system combines data from multiple technologies. SIEM systems are used for collecting and filtering data, detecting and classifying threats, analyzing and investigating threats, and managing resources to implement preventive measures and address future threats. SOC technologies include one or more of the following:
Event collection, correlation, and analysis
Security monitoring
Security control
Log management
Vulnerability assessment
Vulnerability tracking
Threat intelligence
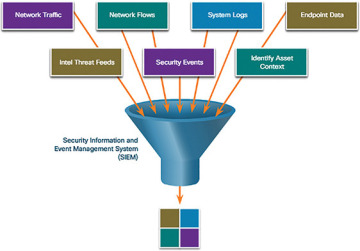
Figure 1-4 SOC Monitoring System
Figure 1-4 is a simplified representation of an SOC monitoring system. Information about network traffic, network flows, system logs, endpoint data, intelligence threat feeds, security events, and identifying asset context are all fed into the SIEM system.
Enterprise and Managed Security (1.2.1.5)
For medium and large networks, the organization will benefit from implementing an enterprise-level SOC. The SOC can be a complete in-house solution. However, many larger organizations will outsource at least part of the SOC operations to a security solutions provider.
Cisco has a team of experts who help ensure timely and accurate incident resolution. Cisco offers a wide range of incident response, preparedness, and management capabilities:
Cisco Smart Net Total Care Service
Cisco Product Security Incident Response Team (PSIRT)
Cisco Computer Security Incident Response Team (CSIRT)
Cisco Managed Services
Cisco Tactical Operations (TacOps)
Cisco’s Safety and Physical Security Program
Security vs. Availability (1.2.1.6)
Most enterprise networks must be up and running at all times. Security personnel understand that for the organization to accomplish its priorities, network availability must be preserved.
Each business or industry has a limited tolerance for network downtime. That tolerance is usually based upon a comparison of the cost of the downtime in relation to the cost of ensuring against downtime. For example, in a small retail business with only one location, it may be tolerable to have a router as a single point of failure. However, if a large portion of that business’s sales are from online shoppers, then the owner may decide to provide a level of redundancy to ensure that a connection is always available.
Preferred uptime is often measured in the number of down minutes in a year, as shown in Table 1-1. For example, a “five nines” uptime means that the network is up 99.999% of the time or down for no more than 5 minutes a year. “Four nines” would be a downtime of 53 minutes a year.
Table 1-1 Availability and Downtime
Availability % |
Downtime |
99.8% |
17.52 hours |
99.9% (“three nines”) |
8.76 hours |
99.99% (“four nines”) |
52.56 minutes |
99.999% (“five nines”) |
5.256 minutes |
99.9999% (“six nines”) |
31.5 seconds |
99.99999% (“seven nines”) |
3.15 seconds |
However, security cannot be so strong that it interferes with the needs of employees or business functions. It is always a tradeoff between strong security and permitting efficient business functioning.
Becoming a Defender (1.2.2)
In this topic, you will learn about the available certifications, degrees, and opportunities for gaining experience in cybersecurity operations.
Certifications (1.2.2.1)
A variety of cybersecurity certifications that are relevant to careers in SOCs are available from several different organizations.
Cisco CCNA Cyber Ops
The CCNA Cyber Ops certification provides a valuable first step in acquiring the knowledge and skills needed to work with a SOC team. It can be a valuable part of a career in the exciting and growing field of cybersecurity operations.
CompTIA Cybersecurity Analyst Certification
The CompTIA Cybersecurity Analyst (CSA+) certification is a vendor-neutral IT professional certification. It validates knowledge and skills required to configure and use threat detection tools, perform data analysis, and interpret the results to identify vulnerabilities, threats, and risks to an organization. The end goal is the ability to secure and protect applications and systems within an organization.
(ISC)2 Information Security Certifications
(ISC)2 is an international non-profit organization that offers the highly acclaimed CISSP certification. (ISC)2 offers a range of other certifications for various specialties in cybersecurity.
Global Information Assurance Certification (GIAC)
GIAC, which was founded in 1999, is one of the oldest security certification organizations. It offers a wide range of certifications in seven categories.
Other Security-Related Certifications
Search for “cybersecurity certifications” to find information about other vendor and vendor-neutral certifications.
Further Education (1.2.2.2)
Degrees
Anyone considering a career in the cybersecurity field, should seriously consider pursuing a technical degree or bachelor’s degree in computer science, electrical engineering, information technology, or information security. Many educational institutions offer security-related specialized tracks and certifications.
Python Programming
Computer programming is an essential skill for anyone who wishes to pursue a career in cybersecurity. If you have never learned how to program, then Python might be the first language to learn. Python is an open-source, object-oriented language that is routinely used by cybersecurity analysts. It is also a popular programming language for Linux-based systems and software-defined networking (SDN).
Sources of Career Information (1.2.2.3)
A variety of websites and mobile applications advertise information technology jobs. Each site targets a variety of job applicants and provides different tools for candidates to research their ideal job position. Many sites are job site aggregators. Job site aggregators gather listings from other job boards and company career sites and display them in a single location.
Indeed.com
Advertised as the world’s #1 job site, Indeed.com attracts over 180 million unique visitors every month from over 50 different countries. Indeed.com is truly a worldwide job site. It helps companies of all sizes hire the best talent and offers the best opportunity for job seekers.
CareerBuilder.com
CareerBuilder serves many large and prestigious companies. As a result, this site attracts specific candidates that typically have more education and higher credentials. The employers posting on CareerBuilder commonly get more candidates with college degrees, advanced credentials, and industry certifications.
USAJobs.gov
The United States federal government posts any openings on USAJobs:
Salary Information
The website glassdoor.com provides salary information for different job types, companies, and locations. Search for “cyber security analyst” to see salaries and requirements for current job openings.
Getting Experience (1.2.2.4)
There are variety of ways to get experience. The following are a few ideas.
Internships
Internships are an excellent method for gaining entry into the cybersecurity field. Sometimes, internships turn into an offer of full-time employment. However, even a temporary internship allows you the opportunity to gain experience in the inner workings of a cybersecurity organization. The contacts you make during an internship can also prove to be a valuable resource as you continue your career.
Search the Internet for a Forbes article titled “The 10 Best Websites For Finding An Internship.”
Cisco Cybersecurity Scholarship
To help close the security skills gap, Cisco introduced the Global Cybersecurity Scholarship program in 2016. Cisco is motivated to increase the pool of talent with critical cybersecurity proficiency. Registration opens in spring and awards are announced in late fall. Visit the following website to learn more about the scholarship:
https://mkto.cisco.com/Security-Scholarship
Temporary Agencies
If you are having difficulty finding your first job, a temporary agency can be a great place to start. Most temporary agencies will help you polish your resume and make recommendations on additional skills you may need to obtain to make yourself more attractive to potential employers.
Many organizations use temporary agencies to fill job openings for the first 90 days. Then, if the employee is a good match, the organization may offer to buy the contract from the temporary agency, converting the employee to a full-time, permanent position.
Your First Job
If you have no experience in the cybersecurity field, then you will most likely look for a company that is willing to train you for a position similar to a Tier 1 Analyst. Working for a call center or support desk may be your first step into gaining the experience you need to move ahead in your career.
How long should you stay in your first job? Generally, you want to make it through a full review cycle before leaving a company. That is, you typically want to make it past 18 months. Potential employers will normally want to know if you met or exceeded expectations in your current or past jobs.
 ACTIVITY 1.2.1.7: IDENTIFY THE SOC TERMINOLOGY
ACTIVITY 1.2.1.7: IDENTIFY THE SOC TERMINOLOGY LAB 1.2.2.5: BECOMING A DEFENDER
LAB 1.2.2.5: BECOMING A DEFENDER