STP Topology Tuning
A properly designed network strategically places the root bridge on a specific switch and modifies which ports should be designated ports (that is, forwarding state) and which ports should be alternate ports (that is, discarding/blocking state). Design considerations factor in hardware platform, resiliency, and network topology. This chapter uses the same reference topology from Chapter 2, “Spanning Tree Protocol,” as shown in Figure 3-1.

FIGURE 3-1 STP Topology for Tuning
Root Bridge Placement
Ideally the root bridge is placed on a core switch, and a secondary root bridge is designated to minimize changes to the overall spanning tree. Root bridge placement is accomplished by lowering the system priority on the root bridge to the lowest value possible, raising the secondary root bridge to a value slightly higher than that of the root bridge, and (ideally) increasing the system priority on all other switches. This ensures consistent placement of the root bridge. The priority is set with either of the following commands:
spanning-tree vlan vlan-id priority priority: The priority is a value between 0 and 61,440, in increments of 4,096.
spanning-tree vlan vlan-id root {primary | secondary} [diameter diameter]: This command executes a script that modifies certain values. The primary keyword sets the priority to 24,576, and the secondary keyword sets the priority to 28,672.
The optional diameter command makes it possible to tune the Spanning Tree Protocol (STP) convergence and modifies the timers; it should reference the maximum number of Layer 2 hops between a switch and the root bridge. The timers do not need to be modified on other switches because they are carried throughout the topology through the root bridge’s bridge protocol data units (BPDUs).
Example 3-1 verifies the initial priority for VLAN 1 on SW1 and then checks how the change is made. Afterward, the priority is checked again to ensure that the priority is lowered.
Example 3-1 Changing the STP System Priority on SW1
! Verification of SW1 Priority before modifying the priority
SW1# show spanning-tree vlan 1
VLAN0001
Spanning tree enabled protocol rstp
Root ID Priority 32769
Address 0062.ec9d.c500
This bridge is the root
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 32769 (priority 32768 sys-id-ext 1)
Address 0062.ec9d.c500
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 300 sec
! Configuring the SW1 priority as primary root for VLAN 1 SW1(config)# spanning-tree vlan 1 root primary
! Verification of SW1 Priority after modifying the priority
SW1# show spanning-tree vlan 1
VLAN0001
Spanning tree enabled protocol rstp
Root ID Priority 24577
Address 0062.ec9d.c500
This bridge is the root
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 24577 (priority 24576 sys-id-ext 1)
Address 0062.ec9d.c500
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 300 sec
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi1/0/2 Desg FWD 4 128.2 P2p
Gi1/0/3 Desg FWD 4 128.3 P2p
Gi1/0/14 Desg FWD 4 128.14 P2p
Example 3-2 verifies the priority for VLAN 1 on SW2 before changing its priority so that it will be the backup root bridge in the event of a failure with SW1. Notice that the root bridge priority is now 24,577, and the local switch’s priority is initially set to 32,769 (the default). Then the command spanning-tree vlan 1 root secondary is executed to modify SW2’s priority, setting it to 28,673.
Example 3-2 Changing the STP System Priority on SW2
! Verification of SW2 Priority before modifying the priority
SW2# show spanning-tree vlan 1
! Output omitted for brevity
VLAN0001
Spanning tree enabled protocol rstp
Root ID Priority 24577
Address 0062.ec9d.c500
Cost 4
Port 1 (GigabitEthernet1/0/1)
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 32769 (priority 32768 sys-id-ext 1)
Address 0081.c4ff.8b00
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 300 sec
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi1/0/1 Root FWD 4 128.1 P2p
Gi1/0/3 Desg FWD 4 128.3 P2p
Gi1/0/4 Desg FWD 4 128.4 P2p
! Configuring the SW2 priority as root secondary for VLAN 1 SW2(config)# spanning-tree vlan 1 root secondary
SW2# show spanning-tree vlan 1
VLAN0001
Spanning tree enabled protocol rstp
Root ID Priority 24577
Address 0062.ec9d.c500
Cost 4
Port 1 (GigabitEthernet1/0/1)
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 28673 (priority 28672 sys-id-ext 1)
Address 0081.c4ff.8b00
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 300 sec
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi1/0/1 Root FWD 4 128.1 P2p
Gi1/0/3 Desg FWD 4 128.3 P2p
Gi1/0/4 Desg FWD 4 128.4 P2p
The placement of the root bridge is an important decision and often should be chosen to minimize the number of hops to the furthest switch in the topology. The design should consider where redundant connections exist, connections that will be blocked, and the ability (performance) for the root switch to handle cross-switch traffic. Generally, root switches are at Layer 2/Layer 3 boundaries.
The best way to prevent erroneous devices from taking over the STP root role is to set the priority to 0 for the primary root switch and to 4096 for the secondary root switch. In addition, root guard should be used (as discussed later in this chapter).
Modifying STP Root Port and Blocked Switch Port Locations
The STP port cost is used in calculating the STP tree. When a switch generates the BPDUs, the total path cost includes only the calculated metric to the root and does not include the cost of the port out which the BPDU is advertised. The receiving switch adds the port cost for the interface on which the BPDU was received in conjunction to the value of the total path cost in the BPDU.
In Figure 3-2, SW1 advertises its BPDUs to SW3 with a total path cost of 0. SW3 receives the BPDU and adds its STP port cost of 4 to the total path cost in the BPDU (0), resulting in a value of 4. SW3 then advertises the BPDU toward SW5 with a total path cost of 4, to which SW5 then adds its STP port cost cost of 4. SW5 therefore reports a total path cost of 8 to reach the root bridge via SW3.
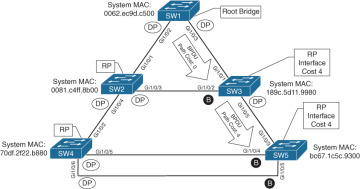
FIGURE 3-2 STP Path Cost Calculation
The logic is confirmed in the output of Example 3-3. Notice that there is not a total path cost in SW1’s output.
Example 3-3 Verifying the Total Path Cost
SW1# show spanning-tree vlan 1
! Output omitted for brevity
VLAN0001
Root ID Priority 32769
Address 0062.ec9d.c500
This bridge is the root
..
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi1/0/2 Desg FWD 4 128.2 P2p
Gi1/0/3 Desg FWD 4 128.3 P2p
SW3# show spanning-tree vlan 1
! Output omitted for brevity
VLAN0001
Root ID Priority 32769
Address 0062.ec9d.c500
Cost 4
Port 1 (GigabitEthernet1/0/1)
..
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi1/0/1 Root FWD 4 128.1 P2p
Gi1/0/2 Altn BLK 4 128.2 P2p
Gi1/0/5 Desg FWD 4 128.5 P2p
SW5# show spanning-tree vlan 1
! Output omitted for brevity
VLAN0001
Root ID Priority 32769
Address 0062.ec9d.c500
Cost 8
Port 3 (GigabitEthernet1/0/3)
..
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi1/0/3 Root FWD 4 128.3 P2p
Gi1/0/4 Altn BLK 4 128.4 P2p
Gi1/0/5 Altn BLK 4 128.5 P2p
By changing the STP port costs with the command spanning tree [vlan vlan-id] cost cost, you can modify the STP forwarding path. You can lower a path that is currently an alternate port while making it designated, or you can raise the cost on a port that is designated to turn it into a blocking port. The spanning tree command modifies the cost for all VLANs unless the optional vlan keyword is used to specify a VLAN.
Example 3-4 demonstrates the modification of SW3’s port cost for Gi1/0/1 to a cost of 1, which impacts the port state between SW2 and SW3. SW2 receives a BPDU from SW3 with a cost of 5, and SW3 receives a BPDU from SW2 with a cost of 8. Now SW3’s Gi1/0/2 is no longer an alternate port but is now a designated port. SW2’s Gi1/0/3 port has changed from a designated port to an alternate port.
Example 3-4 Modifying STP Port Cost
SW3# conf t SW3(config)# interface gi1/0/1 SW3(config-if)# spanning-tree cost 1
SW3# show spanning-tree vlan 1
! Output omitted for brevity
VLAN0001
Root ID Priority 32769
Address 0062.ec9d.c500
Cost 1
Port 1 (GigabitEthernet1/0/1)
Bridge ID Priority 32769 (priority 32768 sys-id-ext 1)
Address 189c.5d11.9980
..
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi1/0/1 Root FWD 1 128.1 P2p
Gi1/0/2 Desg FWD 4 128.2 P2p
Gi1/0/5 Desg FWD 4 128.5 P2p
SW2# show spanning-tree vlan 1
! Output omitted for brevity
VLAN0001
Root ID Priority 32769
Address 0062.ec9d.c500
Cost 4
Port 1 (GigabitEthernet1/0/1)
Bridge ID Priority 32769 (priority 32768 sys-id-ext 1)
Address 0081.c4ff.8b00
..
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi1/0/1 Root FWD 4 128.1 P2p
Gi1/0/3 Altn BLK 4 128.3 P2p
Gi1/0/4 Desg FWD 4 128.4 P2p
Modifying STP Port Priority
The STP port priority impacts which port is an alternate port when multiple links are used between switches. In our test topology, shutting down the link between SW3 and SW5 forces SW5 to choose one of the links connected to SW4 as a root port.
Example 3-5 verifies that this change makes SW5’s Gi1/0/4 the root port (RP) toward SW4. Remember that system ID and port cost are the same, so the next check is port priority, followed by the port number. Both the port priority and port number are controlled by the upstream switch.
Example 3-5 Viewing STP Port Priority
SW5# show spanning-tree vlan 1
! Output omitted for brevity
VLAN0001
Spanning tree enabled protocol rstp
Root ID Priority 32769
Address 0062.ec9d.c500
Cost 12
Port 4 (GigabitEthernet1/0/4)
Bridge ID Priority 32769 (priority 32768 sys-id-ext 1)
Address bc67.1c5c.9300
..
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi1/0/4 Root FWD 4 128.4 P2p
Gi1/0/5 Altn BLK 4 128.5 P2p
You can modify the port priority on SW4’s Gi1/0/6 (toward R5’s Gi1/0/5 interface) with the command spanning-tree [vlan vlan-id] port-priority priority. The optional vlan keyword allows you to change the priority on a VLAN-by-VLAN basis. Example 3-6 shows how to change the port priority on SW4’s Gi1/0/6 port to 64.
Example 3-6 Verifying Port Priority Impact on an STP Topology
SW4# configure terminal Enter configuration commands, one per line. End with CNTL/Z. SW4(config)# interface gi1/0/6 SW4(config-if)# spanning-tree port-priority 6
Now SW4’s Gi1/0/6 port has a value of 64, which is lower than the value of its Gi1/0/5 port, which is using a default value of 128. SW4’s Gi1/0/6 interface is now preferred and will impact the RP on SW5, as displayed in Example 3-7.
Example 3-7 Determining the Impact of Port Priority on a Topology
SW4# show spanning-tree vlan 1 ! Output omitted for brevity Interface Role Sts Cost Prio.Nbr Type ------------------- ---- --- --------- -------- -------------------------------- Gi1/0/2 Root FWD 4 128.2 P2p Gi1/0/5 Desg FWD 4 128.5 P2p Gi1/0/6 Desg FWD 4 64.6 P2p
SW5# show spanning-tree vlan 1 ! Output omitted for brevity Interface Role Sts Cost Prio.Nbr Type ------------------- ---- --- --------- -------- -------------------------------- Gi1/0/4 Altn BLK 4 128.4 P2p Gi1/0/5 Root FWD 4 128.5 P2p