Past Solutions to Today’s Problems
Over the years, demands on the network have steadily increased, and the IT industry has adapted to these demands. However, this doesn’t mean that the industry has adapted quickly or properly. Networks only exist to carry applications and data. The methods of how these applications and data have been handled have also been in constant flux. From a design perspective, the mechanisms implemented in the network ultimately depend on the outcome the business is trying to achieve. This means that the mechanisms aren’t always best practice or validated designs. The configurations of these devices are often ad hoc in nature and usually include point-in-time fixes for issues that arise in the network that need to be addressed.
Spanning-Tree and Layer 2–Based Networks
One of the most common technologies that gets a lot of notoriety is Spanning Tree. Spanning Tree was designed to prevent loops in the Layer 2 network. However, it can cause a tremendous amount of problems in the network if not tuned and managed properly. There are many settings and configuration techniques for Spanning Tree as well as multiple versions that provide some variation of what the protocol was designed to do. Table 1-2 lists the many versions or flavors of Spanning Tree and their associated abbreviations.
Table 1-2 Spanning Tree Versions
Type of Spanning Tree |
Abbreviation |
Legacy Spanning Tree Protocol |
STP |
Per-VLAN Spanning Tree |
PVST |
Per-VLAN Spanning Tree Plus |
PVST+ |
Rapid Spanning Tree Protocol |
RSTP |
Rapid Per-VLAN Spanning Tree Plus |
RPVST+ |
Multiple Spanning Tree |
MST |
Spanning Tree is often used in three-tier campus architectures that rely on Layer 2 distribution and access layers, with routing typically done at the distribution block. This entirely depends on design, of course, but this is the usual place for Spanning Tree. First hop redundancy protocols (FHRPs) are used for each subnet and are configured to provide gateway information for the local subnets and aid in routing the traffic to its destination. The following are examples of first hop redundancy protocols:
Hot Standby Routing Protocol (HSRP)
Virtual Router Redundancy Protocol (VRRP)
Gateway Load Balancing Protocol (GLBP)
Prior to the advent of Layer 3 routed access, Spanning Tree was also primarily used in Layer 2 networks that had stretched VLANs to support mobile wireless users. This was because wireless users required the capability to roam anywhere in the campus and maintain the same Service Set Identifier (SSID), IP address, and security policy. This was necessary due to the reliance on IP addresses and VLANs to dictate which policy or access list was associated to which wired or wireless user. However, there were inherent limitations of Spanning Tree, such as only being able to use half the bandwidth of a pair of redundant links. This is because the other path is in a blocked state. There are, however, many different ways to manipulate this per VLAN or per instance, but this is still the case for Spanning Tree. Other drawbacks are the potential for flooding issues or blocked links causing an outage in the network. This impacts business continuity and disrupts users, making it difficult to get the network back online in a quick fashion. Some Spanning Tree outages can last for hours or days if the issue is not found and remedied.
Figure 1-8 illustrates a typical three-tier campus network architecture design that leverages Spanning Tree and HSRP, showing that there are certain links that are unusable because Spanning Tree blocks links to avoid a looped path within the network.
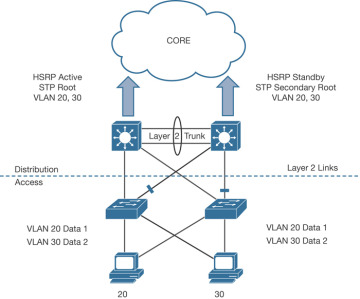
Figure 1-8 Spanning Tree Example
With the advent of Layer 3 routed access, Spanning Tree is no longer necessary to prevent loops because there is no longer a Layer 2 network. However, Layer 3 routed access introduced another set of issues that needed to be addressed. There is still the issue of security policy relying on IP addressing. In addition, now that VLANs are not being stretched across the network using trunking, wireless networks have to change how they operate. This means that wireless SSIDs have to map to subnets, and if a user moves from one access point on an SSID and goes to the same SSID in another area of the network on a different access point, it is likely that their IP address would change. This means there has to be another access list on the new subnet with the same settings as the access list on the previous subnet; otherwise, the user’s security policy would change. Imagine the overhead of having to configure multiple access lists on multiple subnets. This is how networks were traditionally configured. The amount of manual configuration, potential for misconfiguration, and time wasted are just some of the caveats of this type of network design. Figure 1-9 depicts a Layer 3 routed access network.
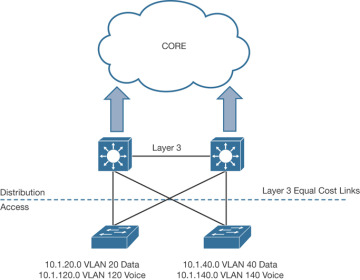
Figure 1-9 Routed Access Example
Layer 3 routed access is also very prominent in the data center environment. This is due to all the benefits of moving to a Layer 3 routed access model versus a Layer 2 network. The following is a list of benefits to using a routed access network:
Increased availability
Reduced complexity
Simplified design
Removal of Spanning Tree
As mentioned earlier in this chapter, real-time and interactive video applications are becoming more mainstream, and organizations expect their users to have the capability to connect from anywhere at any time. The campus network must be available at all times to support this type of business case. Routed access leverages point-to-point links, which not only reduces the amount of time it takes to recover from a direct link failure, but simplifies the design by relying only on a dynamic routing protocol (versus Layer 2 complexities, Spanning Tree, and Layer 3 routing protocols). Coupled with all links in the environment now being active and forwarding traffic, there is a large gain in bandwidth and faster failure detection with point-to-point links versus Layer 2. The industry is demanding networks that include ultra-fast, low-latency, high-bandwidth links that are always available and that are able to scale to meet the demands of the organizations that are using them. Figure 1-10 illustrates the difference between Layer 2– and Layer 3–based campus designs.
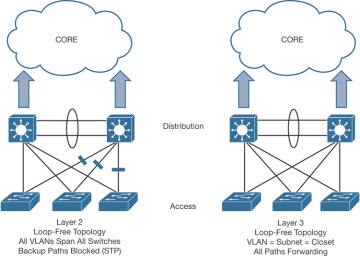
Figure 1-10 Layer 2 Versus Layer 3 Campus Design