EIGRP Fundamentals
EIGRP overcomes the deficiencies of other distance vector routing protocols, such as Routing Information Protocol (RIP), with features such as unequal-cost load balancing, support for networks 255 hops away, and rapid convergence features. EIGRP uses a diffusing update algorithm (DUAL) to identify network paths and provides for fast convergence using precalculated loop-free backup paths. Most distance vector routing protocols use hop count as the metric for routing decisions. However, a route-selection algorithm that uses only hop count for path selection does not take into account link speed and total delay. EIGRP adds logic to the route-selection algorithm to use factors other than hop count alone.
Autonomous Systems
A router can run multiple EIGRP processes. Each process operates under the context of an autonomous system, which represents a common routing domain. Routers within the same domain use the same metric calculation formula and exchange routes only with members of the same autonomous system (AS). Do not confuse an EIGRP autonomous system with a Border Gateway Protocol (BGP) autonomous system.
In Figure 2-1, EIGRP AS 100 consists of R1, R2, R3, and R4, and EIGRP AS 200 consists of R3, R5, and R6. Each EIGRP process correlates to a specific autonomous system and maintains an independent EIGRP topology table. R1 does not have knowledge of routes from AS 200 because it is different from its own autonomous system, AS 100. R3 is able to participate in both autonomous systems and, by default, does not transfer routes learned from one autonomous system into a different autonomous system.

Figure 2-1 EIGRP Autonomous Systems
EIGRP uses protocol-dependent modules (PDMs) to support multiple network protocols, such as IPv4, IPv6, AppleTalk, and IPX. EIGRP is written so that the PDM is responsible for the functions to handle the route selection criteria for each communication protocol. In theory, new PDMs can be written as new communication protocols are created. Current implementations of EIGRP support only IPv4 and IPv6.
EIGRP Terminology
This section explains some of the core concepts of EIGRP, along with the path selection process. Figure 2-2 is a reference topology for this section, showing R1 calculating the best path and alternative loop-free paths to the 10.4.4.0/24 network. A value in parentheses represents the link’s calculated metric for a segment based on bandwidth and delay.
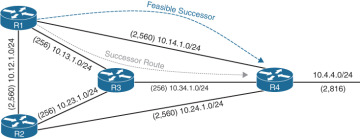
Figure 2-2 EIGRP Reference Topology
Table 2-2 defines important terms related to EIGRP and correlates them to Figure 2-2.

Table 2-2 EIGRP Terminology
Term |
Definition |
|---|---|
Successor route |
The route with the lowest path metric to reach a destination. The successor route for R1 to reach 10.4.4.0/24 on R4 is R1→R3→R4. |
Successor |
The first next-hop router for the successor route. R1’s successor for 10.4.4.0/24 is R3. |
Feasible distance (FD) |
The metric value for the lowest path metric to reach a destination. The feasible distance is calculated locally using the formula shown in the “Path Metric Calculation” section, later in this chapter. The FD calculated by R1 for the 10.4.4.0/24 destination network is 3328 (that is, 256 + 256 + 2816). |
Reported distance (RD) |
Distance reported by a router to reach a destination. The reported distance value is the feasible distance for the advertising router. R3 advertises the 10.4.4.0/24 destination network to R1 and R2 with an RD of 3072. R4 advertises the 10.4.4.0/24 destination network to R1, R2, and R3 with an RD of 2816. |
Feasibility condition |
For a route to be considered a backup route, the RD received for that route must be less than the FD calculated locally. This logic guarantees a loop-free path. |
Feasible successor |
A route that satisfies the feasibility condition is maintained as a backup route. The feasibility condition ensures that the backup route is loop free. The route R1→R4 is the feasible successor because the RD of 2816 is lower than the FD of 3328 for the R1→R3→R4 path. |

Topology Table
EIGRP contains a topology table, which makes it different from a true distance vector routing protocol. EIGRP’s topology table is a vital component of DUAL and contains information to identify loop-free backup routes. The topology table contains all the network prefixes advertised within an EIGRP autonomous system. Each entry in the table contains the following:
Network prefix
EIGRP neighbors that have advertised that prefix
Metrics from each neighbor (reported distance and hop count)
Values used for calculating the metric (load, reliability, total delay, and minimum bandwidth)
The command show ip eigrp topology [all-links] provides the topology table. By default, only the successor and feasible successor routes are displayed, but the optional all-links keyword shows the paths that did not pass the feasibility condition.
Figure 2-3 shows the topology table for R1 from Figure 2-2. This section focuses on the 10.4.4.0/24 network when explaining the topology table.
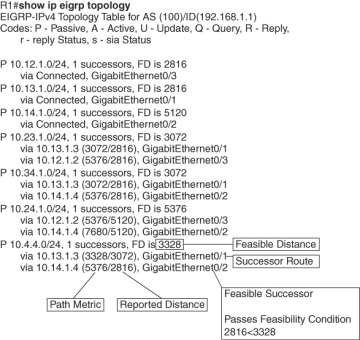
Figure 2-3 EIGRP Topology Output
Examine the 10.4.4.0/24 prefix and notice that R1 calculates an FD of 3328 for the successor route. The successor (upstream router) advertises the successor route with an RD of 3072. The second path entry has a metric of 5376 and has an RD of 2816. Because 2816 is less than 3328, the second entry passes the feasibility condition, which means the second entry is classified as the feasible successor for the 10.4.4.0/24 prefix.
The 10.4.4.0/24 route is passive (P), which means the topology is stable. During a topology change, routes go into an active (A) state when computing a new path.
EIGRP Neighbors
Unlike a number of routing protocols—such as Routing Information Protocol (RIP), Open Shortest Path First (OSPF), and Intermediate System-to-Intermediate System (IS-IS)—EIGRP does not rely on periodic advertisement of all the network prefixes in an autonomous system. EIGRP neighbors exchange the entire routing table when forming an adjacency, and they advertise incremental updates only as topology changes occur within a network. The neighbor adjacency table is vital for tracking neighbor status and the updates sent to each neighbor.
Inter-Router Communication
EIGRP uses five different packet types to communicate with other routers, as shown in Table 2-3. EIGRP uses IP protocol number (88) and uses multicast packets where possible; it uses unicast packets when necessary. Communication between routers is done with multicast using the group address 224.0.0.10 or the MAC address 01:00:5e:00:00:0a when possible.

Table 2-3 EIGRP Packet Types
Opcode Value |
Packet Type |
Function |
|---|---|---|
1 |
Update |
Used to transmit routing and reachability information with other EIGRP neighbors |
2 |
Request |
Used to get specific information from one or more neighbors |
3 |
Query |
Sent out to search for another path during convergence |
4 |
Reply |
Sent in response to a query packet |
5 |
Hello |
Used for discovery of EIGRP neighbors and for detecting when a neighbor is no longer available |
EIGRP uses Reliable Transport Protocol (RTP) to ensure that packets are delivered in order and to ensure that routers receive specific packets. A sequence number is included in each EIGRP packet. The sequence value zero does not require a response from the receiving EIGRP router; all other values require an ACK packet that includes the original sequence number.
Ensuring that packets are received makes the transport method reliable. All update, query, and reply packets are deemed reliable, and hello and ACK packets do not require acknowledgment and could be unreliable.
If the originating router does not receive an ACK packet from the neighbor before the retransmit timeout expires, it notifies the non-acknowledging router to stop processing its multicast packets. The originating router sends all traffic by unicast until the neighbor is fully synchronized. Upon complete synchronization, the originating router notifies the destination router to start processing multicast packets again. All unicast packets require acknowledgment. EIGRP retries up to 16 times for each packet that requires confirmation, and it resets the neighbor relationship when the neighbor reaches the retry limit of 16.

Forming EIGRP Neighbors
Unlike other distance vector routing protocols, EIGRP requires a neighbor relationship to form before routes are processed and added to the Routing Information Base (RIB). Upon hearing an EIGRP hello packet, a router attempts to become the neighbor of the other router. The following parameters must match for the two routers to become neighbors:
Metric formula K values
Primary subnet matches
Autonomous system number (ASN) matches
Authentication parameters
Figure 2-4 shows the process EIGRP uses for forming neighbor adjacencies.
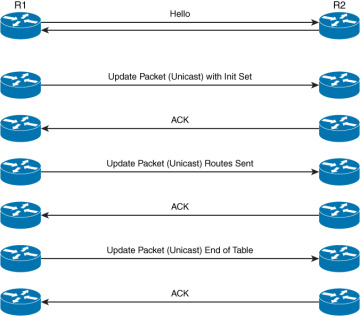
Figure 2-4 EIGRP Neighbor Adjacency Process from R1’s Perspective