WAN Technologies Overview (1.1)
In this section, you learn about WAN access technologies available to small- to medium-sized business networks.
Purpose of WANs (1.1.1)
In this topic, you learn the purpose of the WAN.
Why a WAN? (1.1.1.1)
A WAN operates beyond the geographic scope of a LAN. As shown Figure 1-1, WANs are used to interconnect the enterprise LAN to remote LANs in branch sites and telecommuter sites.
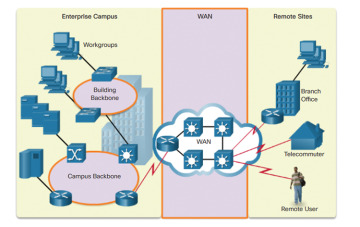
Figure 1-1 WANs Interconnect Users and LANs
A WAN is owned by a service provider. A user must pay a fee to use the provider’s network services to connect remote sites. WAN service providers include carriers, such as a telephone network, cable company, or satellite service. Service providers provide links to interconnect remote sites for the purpose of transporting data, voice, and video.
In contrast, LANs are typically owned by an organization. They are used to connect local computers, peripherals, and other devices within a single building or other small geographic area.
Are WANs Necessary? (1.1.1.2)
Without WANs, LANs would be a series of isolated networks. LANs provide both speed and cost-efficiency for transmitting data over relatively small geographic areas. However, as organizations expand, businesses require communication among geographically separated sites. The following are some examples:
Regional or branch offices of an organization need to be able to communicate and share data with the central site.
Organizations need to share information with other customer organizations. For example, software manufacturers routinely communicate product and promotional information to distributors that sell their products to end users.
Employees who travel on company business frequently need to access information that resides on their corporate networks.
Home computer users also need to send and receive data across increasingly larger distances. Here are some examples:
Consumers now commonly communicate over the Internet with banks, stores, and a variety of providers of goods and services.
Students do research for classes by accessing library indexes and publications located in other parts of their country and in other parts of the world.
It is not feasible to connect computers across a country, or around the world, with physical cables. Therefore, different technologies have evolved to support this communication requirement. Increasingly, the Internet is being used as an inexpensive alternative to enterprise WANs. New technologies are available to businesses to provide security and privacy for their Internet communications and transactions. WANs used by themselves, or in concert with the Internet, allow organizations and individuals to meet their wide-area communication needs.
WAN Topologies (1.1.1.3)
Interconnecting multiple sites across WANs can involve a variety of service provider technologies and WAN topologies. Common WAN topologies are
Point-to-point topology
Hub-and-spoke topology
Full mesh topology
Dual-homed topology
Point-to-Point
A point-to-point topology, as shown in Figure 1-2, employs a point-to-point circuit between two endpoints. Typically involving dedicated leased-line connections like a T1 or an E1 line, a point-to-point connection provides a Layer 2 transport service through the service provider network. Packets sent from one site are delivered to the other site and vice versa. A point-to-point connection is transparent to the customer network, as if there was a direct physical link between two endpoints.
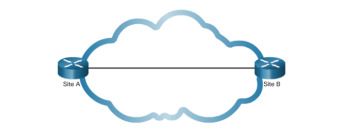
Figure 1-2 Point-to-Point Topology
Hub-and-Spoke
If a private network connection between multiple sites is required, a point-to-point topology with multiple point-to-point circuits is one option. Each point-to-point circuit requires its own dedicated hardware interface that will require multiple routers with multiple WAN interface cards. This interface can be expensive. A less expensive option is a point-to-multipoint topology, also known as a hub-and-spoke topology.
With a hub-and-spoke topology, all spoke circuits can share a single interface to the hub. For example, spoke sites can be interconnected through the hub site using virtual circuits and routed subinterfaces at the hub. A hub-and-spoke topology is also an example of a single-homed topology. Figure 1-3 displays a sample hub-and-spoke topology consisting of four routers with one router as a hub connected to the other three spoke routers across a WAN cloud.

Figure 1-3 Hub-and-Spoke Topology
Full Mesh
One of the disadvantages of hub-and-spoke topologies is that all communication has to go through the hub. With a full mesh topology using virtual circuits, any site can communicate directly with any other site. The disadvantage here is the large number of virtual circuits that need to be configured and maintained. Figure 1-4 displays a sample full mesh topology consisting of four routers connected to each other across a WAN cloud.
Dual-homed Topology
A dual-homed topology provides redundancy. As shown in Figure 1-5, the spoke routers are dual-homed and redundantly attached to two hub routers across a WAN cloud. The disadvantage to dual-homed topologies is that they are more expensive to implement than a single-homed topology. The reason is that they require additional networking hardware, like additional routers and switches. Dual-homed topologies are also more difficult to implement because they require additional, and more complex, configurations. However, the advantage of dual-homed topologies is that they offer enhanced network redundancy, load balancing, distributed computing or processing, and the ability to implement backup service provider connections.

Figure 1-4 Full Mesh Topology

Figure 1-5 Dual-Homed Topology
Evolving Networks (1.1.1.4)
Every business is unique, so how an organization grows depends on many factors. These factors include the types of products or services the business sells, the management philosophy of the owners, and the economic climate of the country in which the business operates.
In slow economic times, many businesses focus on increasing their profitability by improving the efficiency of their existing operations, increasing employee productivity, and lowering operating costs. Establishing and managing networks can represent significant installation and operating expenses. To justify such a large expense, companies expect their networks to perform optimally and to be able to deliver an ever-increasing array of services and applications to support productivity and profitability.
The example used in this chapter and shown in Figure 1-6 is of a fictitious company called SPAN Engineering. This topic will illustrate how SPAN’s network requirements change as the company grows from a small, local business into a global enterprise.
Figure 1-6 SPAN Engineering
Small Office (1.1.1.5)
SPAN Engineering, an environmental consulting firm, has developed a special process for converting household waste into electricity and is developing a small pilot project for a municipal government in its local area. The company, which has been in business for four years, is a small office consisting of 15 employees: six engineers, four computer-aided drawing (CAD) designers, a receptionist, two senior partners, and two office assistants.
SPAN Engineering’s management is working to win full-scale contracts after the pilot project successfully demonstrates the feasibility of the company’s process. Until then, the company must manage its costs carefully.
As shown in Figure 1-7, SPAN Engineering uses a single LAN to share information between computers and to share peripherals, such as a printer, a large-scale plotter (to print engineering drawings), and fax equipment.
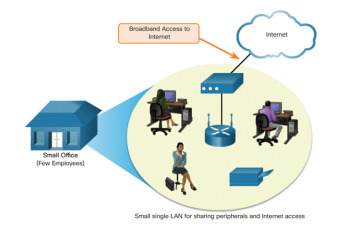
Figure 1-7 Connecting a Small Office
The company has recently upgraded its LAN to provide inexpensive voice over IP (VoIP) service to save on the costs of separate phone lines for employees.
Internet connectivity is provided using a common broadband service called digital subscriber line (DSL), which is supplied by the local telephone service provider. Because SPAN has so few employees, bandwidth is not a significant problem.
The company cannot afford in-house IT support staff, so it uses support services purchased from the DSL provider. The company also uses a hosting service rather than purchasing and operating its own FTP and email servers.
Campus Network (1.1.1.6)
Five years later, SPAN Engineering has grown rapidly. The company was contracted to design and implement a full-size waste conversion facility soon after the successful implementation of its first pilot plant. Since then, SPAN has won other projects in neighboring municipalities and in other parts of the country.
To handle the additional workload, the business has hired more staff and leased more office space. It is now a small- to medium-sized business with several hundred employees. Many projects are being developed at the same time, and each requires a project manager and support staff. The company has organized itself into functional departments, with each department having its own organizational team. To meet its growing needs, the company has moved into several floors of a larger office building.
As the business has expanded, the network has also grown. Instead of a single small LAN, the network now consists of several subnetworks, each devoted to a different department. For example, all the engineering staff is on one LAN, while the marketing staff is on another LAN. These multiple LANs are joined to create a companywide network, or campus, which spans several floors of the building.
Figure 1-8 shows an example of SPAN’s campus network.
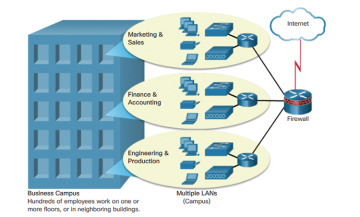
Figure 1-8 Connecting a Campus Network
The business now has in-house IT staff to support and maintain the network. The network includes dedicated servers for email, data transfer, and file storage, and web-based productivity tools and applications. In addition, a company intranet provides in-house documents and information to employees. An extranet provides project information to designated customers.
Branch Networks (1.1.1.7)
Another six years later, SPAN Engineering has been so successful with its patented process that demand for its services has skyrocketed. New projects are underway in multiple cities. To manage those projects, the company has opened small branch offices closer to the project sites.
This situation presents new challenges to the IT team. To manage the delivery of information and services throughout the company, SPAN Engineering now has a data center, which houses the various databases and servers of the company. To ensure that all parts of the business are able to access the same services and applications regardless of where the offices are located, the company must now implement a WAN.
For its branch offices that are in nearby cities, the company decides to use private dedicated lines through a local service provider, as shown in Figure 1-9. However, for those offices that are located in other countries, the Internet is an attractive WAN connection option. Although connecting offices through the Internet is economical, this approach introduces security and privacy issues that the IT team must address.
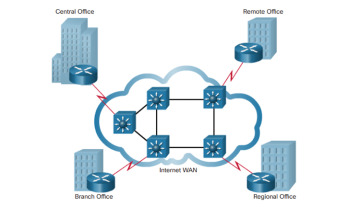
Figure 1-9 Connecting Branch Networks
Distributed Network (1.1.1.8)
SPAN Engineering has now been in business for 20 years and has grown to thousands of employees distributed in offices worldwide, as shown in Figure 1-10.
The cost of the enterprise network and its related services is a significant expense. The company is looking to provide its employees with the best network services at the lowest cost. Optimized network services would allow each employee to work at a high rate of efficiency.

Figure 1-10 SPAN Engineering
To increase profitability, SPAN Engineering must reduce its operating expenses. It has relocated some of its office facilities to less expensive areas. The company is also encouraging teleworking and virtual teams. Web-based applications, including web conferencing, e-learning, and online collaboration tools, are being used to increase productivity and reduce costs. Site-to-site and remote-access virtual private networks (VPNs) enable the company to use the Internet to connect easily and securely with employees and facilities around the world. To meet these requirements, the network must provide the necessary converged services and secure Internet WAN connectivity to remote offices and individuals, as shown in Figure 1-11.
As seen in this example, network requirements of a company can change dramatically as the company grows over time. Distributing employees saves costs in many ways, but it puts increased demands on the network.
A network not only must meet the day-to-day operational needs of the business but also must be able to adapt and grow as the company changes. Network designers and administrators meet these challenges by carefully choosing network technologies, protocols, and service providers. They must also optimize their networks by using many of the network design techniques and architectures described in this course.
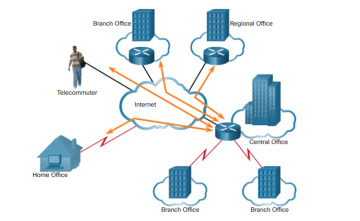
Figure 1-11 Connecting a Global Enterprise Network
WAN Operations (1.1.2)
In this topic, you learn how WANs operate.
WANs in the OSI Model (1.1.2.1)
WAN operations focus primarily on the physical layer (OSI Layer 1) and the data link layer (OSI Layer 2), as illustrated in Figure 1-12. WAN access standards typically describe both physical layer delivery methods and data link layer requirements. The data link layer requirements include physical addressing, flow control, and encapsulation.
WAN access standards are defined and managed by a number of recognized authorities:
Telecommunications Industry Association (TIA)
Electronic Industries Alliance (EIA)
International Organization for Standardization (ISO)
Institute of Electrical and Electronics Engineers (IEEE)
Layer 1 protocols describe how to provide electrical, mechanical, operational, and functional connections to the services of a communications service provider.

Figure 1-12 WANs Operate in Layers 1 and 2
Layer 2 protocols define how data is encapsulated for transmission toward a remote location and the mechanisms for transferring the resulting frames. A variety of different technologies are used, such as the Point-to-Point Protocol (PPP), Frame Relay, and Asynchronous Transfer Mode (ATM). Some of these protocols use the same basic framing or a subset of the High-Level Data Link Control (HDLC) mechanism.
Most WAN links are point-to-point. For this reason, the address field in the Layer 2 frame is usually not used.
Common WAN Terminology (1.1.2.2)
One primary difference between a WAN and a LAN is that a company or organization must subscribe to an outside WAN service provider to use WAN carrier network services. A WAN uses data links provided by carrier services to access the Internet and connect different locations of an organization to each other. These data links also connect to locations of other organizations, to external services, and to remote users.
The physical layer of a WAN describes the physical connections between the company network and the service provider network. Figure 1-13 illustrates the terminology commonly used to describe WAN connections:
Customer premises equipment (CPE): The CPE consists of the devices and inside wiring located on the enterprise edge connecting to a carrier link. The subscriber (that is, customer) either owns the CPE or leases the CPE from the service provider. A subscriber, in this context, is a company that arranges for WAN services from a service provider.
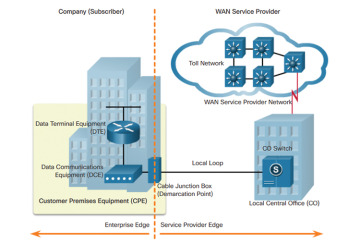
Figure 1-13 WAN Terminology
Data communications equipment (DCE): This is an EIA term. Also called data circuit-terminating equipment by the ITU. The DCE consists of devices that put data on the local loop. The DCE primarily provides an interface to connect subscribers to a communication link on the WAN cloud.
Data terminal equipment (DTE): These customer devices pass the data from a customer network or host computer for transmission over the WAN. The DTE connects to the local loop through the DCE.
Demarcation point: This point is established in a building or complex to separate customer equipment from service provider equipment. Physically, the demarcation point is the cabling junction box, located on the customer premises, that connects the CPE wiring to the local loop. It is usually placed so that a technician can access it easily. The demarcation point is the place where the responsibility for the connection changes from the user to the service provider. When problems arise, it is necessary to determine whether the user or the service provider is responsible for troubleshooting or repair.
Local loop: This loop is the actual copper or fiber cable that connects the CPE to the CO of the service provider. The local loop is also sometimes called the last-mile.
Central office (CO): The CO is the local service provider facility or building that connects the CPE to the provider network.
Toll network: This network consists of the long-haul, all-digital, fiber-optic communications lines, switches, routers, and other equipment inside the WAN provider network.
WAN Devices (1.1.2.3)
Many types of devices are specific to WAN environments, as shown in Figure 1-14, and are described in the list that follows.
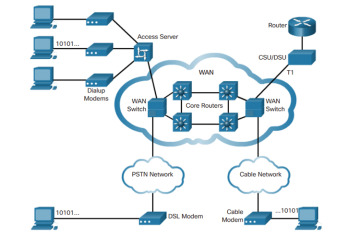
Figure 1-14 Common WAN Devices
Dialup modem: Voiceband modems are considered to be a legacy WAN technology. A voiceband modem modulates (that is, converts) the digital signals produced by a computer into voice frequencies. These frequencies are then transmitted over the analog lines of the public telephone network. On the other side of the connection, another modem demodulates the sounds back into a digital signal for input to a computer or network connection.
Access server: This server controls and coordinates dialup modem, dial-in, and dial-out user communications. Considered to be a legacy technology, an access server may have a mixture of analog and digital interfaces and support hundreds of simultaneous users.
Broadband modem: This type of digital modem is used with high-speed DSL or cable Internet service. Both operate in a similar manner to the voiceband modem but use higher broadband frequencies to achieve higher transmission speeds.
Channel service unit/data service unit (CSU/DSU): Digital leased lines require a CSU and a DSU. A CSU/DSU can be a separate device like a modem, or it can be an interface on a router. The CSU provides termination for the digital signal and ensures connection integrity through error correction and line monitoring. The DSU converts the line frames into frames that the LAN can interpret and vice versa.
WAN switch: This multiport internetworking device is used in service provider networks. These devices typically switch traffic, such as Frame Relay or ATM, and operate at Layer 2.
Router: This device provides internetworking and WAN access interface ports that are used to connect to the service provider network. These interfaces may be serial connections, Ethernet, or other WAN interfaces. With some types of WAN interfaces, an external device, such as a DSU/CSU or modem (analog, cable, or DSL), is required to connect the router to the local service provider.
Core router/Multilayer switch: This router or multilayer switch resides within the middle or backbone of the WAN, rather than at its periphery. To fulfill this role, a router or multilayer switch must be able to support multiple telecommunications interfaces of the highest speed used in the WAN core. It must also be able to forward IP packets at full speed on all of those interfaces. The router or multilayer switch must also support the routing protocols being used in the core.
WAN technologies are either circuit-switched or packet-switched. The type of device used depends on the WAN technology implemented.
Circuit Switching (1.1.2.4)
A circuit-switched network is one that establishes a dedicated circuit (or channel) between nodes and terminals before the users may communicate. Specifically, circuit switching dynamically establishes a dedicated virtual connection for voice or data between a sender and a receiver. Before communication can start, it is necessary to establish the connection through the network of the service provider, as shown in Figure 1-15.
As an example, when a subscriber makes a telephone call, the dialed number is used to set switches in the exchanges along the route of the call so that there is a continuous circuit from the caller to the called party. Because of the switching operation used to establish the circuit, the telephone system is called a circuit-switched network. If the telephones are replaced with modems, the switched circuit is able to carry computer data.

Figure 1-15 Circuit-Switched Network
If the circuit carries computer data, the usage of this fixed capacity may not be efficient. For example, if the circuit is used to access the Internet, a burst of activity occurs on the circuit while a web page is transferred. This burst could be followed by no activity while the user reads the page and then another burst of activity while the next page is transferred. This variation in usage between none and maximum is typical of computer network traffic. Because the subscriber has sole use of the fixed capacity allocation, switched circuits are generally an inefficient way of moving data.
The two most common types of circuit-switched WAN technologies are the public switched telephone network (PSTN) and the Integrated Services Digital Network (ISDN).
Packet Switching (1.1.2.5)
In contrast to circuit switching, a packet-switched network (PSN) splits traffic data into packets that are routed over a shared network. Packet-switching networks do not require a circuit to be established, and they allow many pairs of nodes to communicate over the same channel.
The switches in a PSN determine the links that packets must be sent over based on the addressing information in each packet. The following are two approaches to this link determination:
Connectionless systems: Full addressing information must be carried in each packet. Each switch must evaluate the address to determine where to send the packet. An example of a connectionless system is the Internet.
Connection-oriented systems: The network predetermines the route for a packet, and each packet only has to carry an identifier. The switch determines the onward route by looking up the identifier in tables held in memory. The set of entries in the tables identifies a particular route or circuit through the system. When the circuit is established temporarily while a packet is traveling through it and then breaks down again, it is called a virtual circuit (VC). An example of a connection-oriented system is Frame Relay. In the case of Frame Relay, the identifiers used are called data-link connection identifiers (DLCIs).
Because the internal links between the switches are shared between many users, the cost of packet switching is lower than that of circuit switching. However, latency (delays) and jitter (variability of delay) are greater in packet-switched networks than in circuit-switched networks. The reason is that the links are shared, and packets must be entirely received at one switch before moving to the next. Despite the latency and jitter inherent in shared networks, modern technology allows satisfactory transport of voice and video communications on these networks.
In Figure 1-16, SRV1 is sending data to SRV2. As packets traverse the provider network, they arrive at the first provider switch. Packets are added to the queue and forwarded after other packets in the queue have been forwarded. Eventually, the packets reach SRV2.
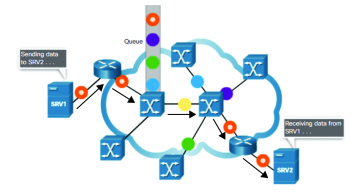
Figure 1-16 Packet-Switched Network
