VPNs (3.3)
In this section, you learn how VPNs secure site-to-site and remote-access connectivity.
Fundamentals of VPNs (3.3.1)
In this topic, you learn about the benefits of VPN technology.
Introducing VPNs (3.3.1.1)
Organizations need secure, reliable, and cost-effective ways to interconnect multiple networks, such as allowing branch offices and suppliers to connect to a corporation’s headquarter network. Additionally, with the growing number of teleworkers, enterprises have an increasing need for secure, reliable, and cost-effective ways to connect employees working in small office/home office (SOHO) and other remote locations, with resources on corporate sites.
As shown in Figure 3-16, organizations use VPNs to create an end-to-end private network connection over third-party networks, such as the Internet. The tunnel eliminates the distance barrier and enables remote users to access central site network resources.
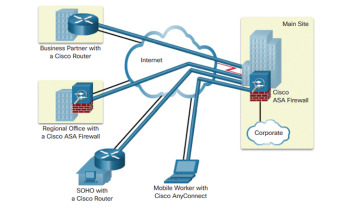
Figure 3-16 VPNs
A VPN is a private network created via tunneling over a public network, usually the Internet. A VPN is a communications environment in which access is strictly controlled to permit peer connections within a defined community of interest.
The first VPNs were strictly IP tunnels that did not include authentication or encryption of the data. For example, Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco that can encapsulate a wide variety of network layer protocol packet types inside IP tunnels. This creates a virtual point-to-point link to Cisco routers at remote points over an IP internetwork. However, GRE does not support encryption.
Today, a secure implementation of VPN with encryption, such as IPsec VPNs, is what is usually meant by virtual private networking.
To implement VPNs, a VPN gateway is necessary. The VPN gateway could be a router, a firewall, or a Cisco Adaptive Security Appliance (ASA). An ASA is a standalone firewall device that combines firewall, VPN concentrator, and intrusion prevention functionality into one software image.
Benefits of VPNs (3.3.1.2)
As shown in Figure 3-17, a VPN uses virtual connections that are routed through the Internet from the private network of an organization to the remote site or employee host. The information from a private network is securely transported over the public network to form a virtual network.
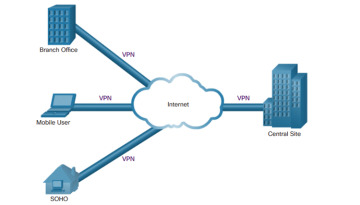
Figure 3-17 VPN Internet Connections
The benefits of a VPN include the following:
Cost savings: VPNs enable organizations to use cost-effective, third-party Internet transport to connect remote offices and remote users to the main site, thus eliminating expensive, dedicated WAN links and modem banks. Furthermore, with the advent of cost-effective, high-bandwidth technologies, such as DSL, organizations can use VPNs to reduce their connectivity costs while simultaneously increasing remote connection bandwidth.
Scalability: VPNs enable organizations to use the Internet infrastructure within ISPs and devices, which makes it easy to add new users. Therefore, organizations are able to add large amounts of capacity without adding significant infrastructure.
Compatibility with broadband technology: VPNs allow mobile workers and teleworkers to take advantage of high-speed, broadband connectivity, such as DSL and cable, to access to their organizations’ networks. Broadband connectivity provides flexibility and efficiency. High-speed, broadband connections also provide a cost-effective solution for connecting remote offices.
Security: VPNs can include security mechanisms that provide the highest level of security by using advanced encryption and authentication protocols that protect data from unauthorized access.
Types of VPNs (3.3.2)
In this topic, you learn about site-to-site and remote-access VPNs.
Site-to-Site VPNs (3.3.2.1)
A site-to-site VPN is created when devices on both sides of the VPN connection are aware of the VPN configuration in advance, as shown in Figure 3-18.

Figure 3-18 Site-to-Site VPNs
The VPN remains static, and internal hosts have no knowledge that a VPN exists. In a site-to-site VPN, end hosts send and receive normal TCP/IP traffic through a VPN “gateway.” The VPN gateway is responsible for encapsulating and encrypting outbound traffic for all traffic from a particular site. The VPN gateway then sends it through a VPN tunnel over the Internet to a peer VPN gateway at the target site. Upon receipt, the peer VPN gateway strips the headers, decrypts the content, and relays the packet toward the target host inside its private network.
A site-to-site VPN is an extension of a classic WAN network. Site-to-site VPNs connect entire networks to each other; for example, they can connect a branch office network to a company headquarters network. In the past, a leased-line or Frame Relay connection was required to connect sites, but because most corporations now have Internet access, these connections are commonly replaced with site-to-site VPNs.
Remote-Access VPNs (3.3.2.2)
Where a site-to-site VPN is used to connect entire networks, a remote-access VPN supports the needs of telecommuters, mobile users, and extranet, consumer-to-business traffic. A remote-access VPN is created when VPN information is not statically set up, but instead allows for dynamically changing information, and can be enabled and disabled. Remote-access VPNs support a client/server architecture, where the VPN client (remote host) gains secure access to the enterprise network via a VPN server device at the network edge, as shown Figure 3-19.
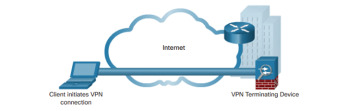
Figure 3-19 Remote-Access VPNs
Remote-access VPNs are used to connect individual hosts that must access their company network securely over the Internet. Internet connectivity used by telecommuters is typically a broadband connection.
VPN client software, such as the Cisco AnyConnect Secure Mobility Client software, is installed on the teleworker host. When the host sends traffic, the Cisco AnyConnect VPN Client software encapsulates, encrypts, and sends the traffic over the Internet to the destination VPN gateway. Upon receipt, the VPN gateway behaves as it does for site-to-site VPNs.
DMVPN (3.3.2.3)
Dynamic Multipoint VPN (DMVPN) is a Cisco software solution for building multiple VPNs in an easy, dynamic, and scalable manner. The goal is to simplify the configuration while easily and flexibly connecting central office sites with branch sites in a hub-and-spoke (or hub-to-spoke) topology, as shown in Figure 3-20.

Figure 3-20 DMVPN Hub-to-Spoke Tunnels
With DMVPNs, branch sites can also communicate directly with other branch sites, as shown in Figure 3-21.
DMVPN is built using the following technologies:
Next Hop Resolution Protocol (NHRP)
Multipoint Generic Routing Encapsulation (mGRE) tunnels
IP Security (IPsec) encryption
NHRP is a Layer 2 resolution and caching protocol similar to Address Resolution Protocol (ARP). NHRP creates a distributed mapping database of public IP addresses for all tunnel spokes. NHRP is a client/server protocol consisting of the NHRP hub known as the Next Hop Server (NHS) and the NHRP spokes known as the Next Hop Clients (NHCs). NHRP supports hub-and-spoke as well as spoke-to-spoke configurations.
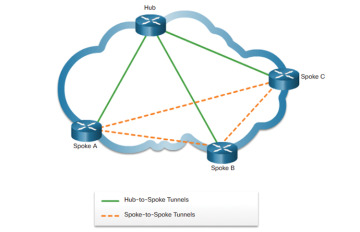
Figure 3-21 DMVPN Hub-to-Spoke and Spoke-to-Spoke Tunnels
Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco that can encapsulate a wide variety of protocol packet types inside IP tunnels. DMVPN makes use of Multipoint Generic Routing Encapsulation (mGRE) tunnel. An mGRE tunnel interface allows a single GRE interface to support multiple IPsec tunnels. With mGRE, dynamically allocated tunnels are created through a permanent tunnel source at the hub and dynamically allocated tunnel destinations, created as necessary, at the spokes. This reduces the size and simplifies the complexity of the configuration.
Like other VPN types, DMVPN relies on IPsec to provide secure transport of private information over public networks, such as the Internet.
