GRE (3.4)
In this section, you implement a GRE tunnel.
GRE Overview (3.4.1)
In this topic, you learn about the purpose and benefits GRE tunnels.
GRE Introduction (3.4.1.1)
Generic Routing Encapsulation (GRE) is one example of a basic, nonsecure, site-to-site VPN tunneling protocol. GRE is a tunneling protocol developed by Cisco that can encapsulate a wide variety of protocol packet types inside IP tunnels. GRE creates a virtual point-to-point link to Cisco routers at remote points, over an IP internetwork.
GRE is designed to manage the transportation of multiprotocol and IP multicast traffic between two or more sites that may have only IP connectivity. It can encapsulate multiple protocol packet types inside an IP tunnel.
As shown in Figure 3-22, a tunnel interface supports a header for each of the following:
Passenger protocol: This is the original IPv4 or IPv6 packet that will be encapsulated by the carrier protocol. It could also be a legacy AppleTalk, DECnet, or IPX packet.
Carrier protocol: This is the encapsulation protocol such as GRE that encapsulates the passenger protocol.
Transport protocol: This is the delivery protocol such as IP that carries the carrier protocol.
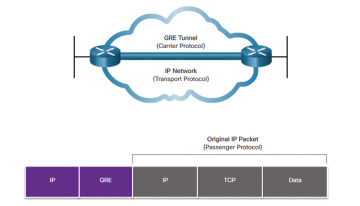
Figure 3-22 Generic Routing Encapsulation
GRE Characteristics (3.4.1.2)
GRE is a tunneling protocol developed by Cisco that can encapsulate a wide variety of protocol packet types inside IP tunnels, creating a virtual point-to-point link to Cisco routers at remote points over an IP internetwork. IP tunneling using GRE enables network expansion across a single-protocol backbone environment. It does this by connecting multiprotocol subnetworks in a single-protocol backbone environment.
GRE has these characteristics:
GRE is defined as an IETF standard (RFC 2784).
GRE is identified as IP protocol 47 in the Transport protocol IP protocol field.
GRE encapsulation includes a protocol type field in its header to provide multiprotocol support. Protocol types are defined in RFC 1700 as “EtherTypes.”
GRE is stateless, which means that, by default, it does not include any flow-control mechanisms.
GRE does not include any strong security mechanisms to protect its payload.
The GRE header consumes at least 24 bytes of additional overhead for tunneled packets.
Figure 3-23 illustrates the GRE header components.
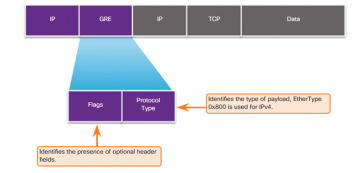
Figure 3-23 Header for GRE Encapsulated Packet Header

Activity 3.4.1.3: Identify GRE Characteristics
Implement GRE (3.4.2)
In this topic, you learn how to troubleshoot a site-to-site GRE tunnel.
Configure GRE (3.4.2.1)
The topology displayed in Figure 3-24 will be used to create a GRE VPN tunnel between two sites.
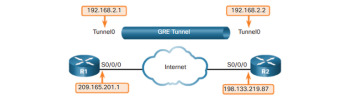
Figure 3-24 GRE Tunnel Configuration Topology
To implement a GRE tunnel, the network administrator must know the reachable IP addresses of the endpoints.
There are five steps to configuring a GRE tunnel:
Step 1. Create a tunnel interface using the interface tunnel number global configuration command.
Step 2. Configure an IP address for the tunnel interface using the ip address ip-address interface configuration command. This is normally a private IP address.
Step 3. Specify the tunnel source IP address or source interface using the tunnel source {ip-address | interface-name} interface configuration command.
Step 4. Specify the tunnel destination IP address using the tunnel destination ip-address interface configuration command.
Step 5. (Optional) Specify GRE tunnel mode as the tunnel interface mode using the tunnel mode gre protocol interface configuration command. GRE tunnel mode is the default tunnel interface mode for Cisco IOS software.
The sample configuration in Example 3-11 illustrates a basic GRE tunnel configuration for R1 and R2.
Example 3-11 R1 and R2 GRE Tunnel Configuration
R1(config)# interface Tunnel0 R1(config-if)# ip address 192.168.2.1 255.255.255.0 R1(config-if)# tunnel source 209.165.201.1 R1(config-if)# tunnel destination 209.165.201.2 R1(config-if)# tunnel mode gre ip R1(config-if)# exit R1(config)# router ospf 1 R1(config-router)# network 192.168.2.0 0.0.0.255 area 0 R2(config)# interface Tunnel0 R2(config-if)# ip address 192.168.2.2 255.255.255.0 R2(config-if)# tunnel source 209.165.201.2 R2(config-if)# tunnel destination 209.165.201.1 R2(config-if)# tunnel mode gre ip R2(config-if)# exit R2(config)# router ospf 1 R2(config-router)# network 192.168.2.0 0.0.0.255 area 0
The minimum configuration requires specification of the tunnel source and destination addresses. The IP subnet must also be configured to provide IP connectivity across the tunnel link. Both tunnel interfaces have the tunnel source set using the IP address of their local serial S0/0/0 interface and the tunnel destination set to the IP address of the peer router serial S0/0/0 interface. The tunnel interface IP address is typically assigned a private IP address. Finally, OSPF is configured to advertise the tunnel network route over the GRE tunnel.
Table 3-1 provides the individual GRE tunnel command descriptions.
Table 3-1 GRE Configuration Command Syntax
| Command | Description |
|---|---|
| ip address ip_address mask | Specifies the IP address of the tunnel interface |
| tunnel source ip_address | Specifies the tunnel source IP address, in interface tunnel configuration mode |
| tunnel destination ip_address | Specifies the tunnel destination IP address, in interface tunnel configuration mode |
| tunnel mode gre ip | Specifies GRE tunnel mode as the tunnel interface mode, in interface tunnel configuration mode |
Verify GRE (3.4.2.2)
Several commands can be used to monitor and troubleshoot GRE tunnels. To determine whether the tunnel interface is up or down, use the show ip interface brief and show interface tunnel number privileged EXEC commands, as demonstrated in Example 3-12.
Example 3-12 Verifying GRE
R1# show ip interface brief | include Tunnel
Tunnel0 192.168.2.1 YES manual up up
R1#
R1# show interface Tunnel 0
Tunnel0 is up, line protocol is up
Hardware is Tunnel
Internet address is 192.168.2.1/24
MTU 17916 bytes, BW 100 Kbit/sec, DLY 50000 usec,
reliability 255/255, txload 1/255, rxload 1/255
Encapsulation TUNNEL, loopback not set
Keepalive not set
Tunnel source 209.165.201.1, destination 209.165.201.2
Tunnel protocol/transport GRE/IP
<output omitted>
The first command verifies that the tunnel 0 interface is up and has an IP address assigned to it. The second command verifies the state of a GRE tunnel, the tunnel source and destination addresses, and the GRE mode supported. The line protocol on a GRE tunnel interface is up as long as there is a route to the tunnel destination. Before a GRE tunnel is implemented, IP connectivity must already be in effect between the IP addresses of the physical interfaces on opposite ends of the potential GRE tunnel.
A routing protocol could also be configured to exchange route information over the tunnel interface. For example if OSPF had also been configured to exchange routes over the GRE tunnel, you could verify that an OSPF adjacency had been established using the show ip ospf neighbor command.
In Example 3-13, note that the peering address for the OSPF neighbor is on the IP network created for the GRE tunnel.
Example 3-13 Verifying OSPF Adjacency via GRE Tunnel
R1# show ip ospf neighbor Neighbor ID Pri State Dead Time Address Interface 209.165.201.2 0 FULL/ - 00:00:37 192.168.2.2 Tunnel0
GRE is considered a VPN because it is a private network that is created by tunneling over a public network. Using encapsulation, a GRE tunnel creates a virtual point-to-point link to Cisco routers at remote points over an IP internetwork.
The advantages of GRE are that it can be used to tunnel non-IP traffic over an IP network, allowing for network expansion by connecting multiprotocol subnetworks across a single-protocol backbone environment. GRE also supports IP multicast tunneling. This means that routing protocols can be used across the tunnel, enabling dynamic exchange of routing information in the virtual network. Finally, it is common practice to create IPv6 over IPv4 GRE tunnels, where IPv6 is the encapsulated protocol and IPv4 is the transport protocol. In the future, these roles will likely be reversed as IPv6 takes over as the standard IP protocol.
However, GRE does not provide encryption or any other security mechanisms. Therefore, data sent across a GRE tunnel is not secure. If secure data communication is needed, IPsec or Secure Sockets Layer (SSL) VPNs should be configured.
Troubleshoot GRE (3.4.2.3)
Issues with GRE are usually due to one or more of the following misconfigurations:
The tunnel interface IP addresses are not on the same network or the subnet masks do not match.
The interfaces for the tunnel source and/or tunnel destination are not configured with the correct IP address or are in the down state.
Static or dynamic routing is not properly configured.
Figure 3-25 shows the GRE configuration topology.
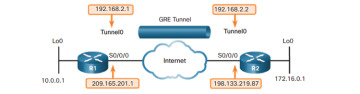
Figure 3-25 GRE Tunnel Configuration Topology
Use the show ip interface brief command on both routers to verify that the tunnel interface is up and configured with the correct IP addresses for the physical interface and the tunnel interface. Also, verify that the source interface on each router is up and configured with the correct IP addresses, as shown in Example 3-14.
Example 3-14 Verifying That All Necessary Interfaces Are Up
R1# show ip interface brief <some output omitted> Interface IP-Address OK? Method Status Protocol Serial0/0/0 209.165.201.1 YES manual up up Loopback0 10.0.0.1 YES manual up up Tunnel0 192.168.2.1 YES manual up up R1# R2# show ip interface brief <some output omitted> Interface IP-Address OK? Method Status Protocol Serial0/0/0 198.133.219.87 YES manual up up Loopback0 172.16.0.1 YES manual up up Tunnel0 192.168.2.2 YES manual up up R2#
Routing can cause an issue. Both routers need a default route pointing to the Internet. Also, both routers need the correct dynamic or static routing configured. You can use the show ip ospf neighbor command to verify neighbor adjacency. Regardless of the routing used, you can also use show ip route to verify that networks are being passed between the two routers, as shown in Example 3-15.
Example 3-15 Verify That Networks Are Being Routed
R1# show ip route ospf
172.16.0.0/32 is subnetted, 1 subnets
O 172.16.0.0 [110/1001] via 192.168.2.2, 00:19:44, Tunnel0
R1#
R2# show ip route ospf
10.0.0.0/32 is subnetted, 1 subnets
O 10.0.0.1 [110/1001] via 192.168.2.1, 00:20:35, Tunnel0
R2#
