Varieties of Spanning Tree Protocols (3.2)
There have been several implementations of STP. In this section, you will learn how different varieties of spanning-tree protocols operate.
Overview (3.2.1)
The focus of this topic is on the different spanning-tree varieties.
Types of Spanning Tree Protocols (3.2.1.1)
Several varieties of spanning-tree protocols have emerged since the original IEEE 802.1D.
The varieties of spanning-tree protocols include the following:
STP—Defined in IEEE 802.1D, this is the original standard that provided a loop-free topology in a network with redundant links. Also called Common Spanning Tree (CST), it assumed one spanning-tree instance for the entire bridged network, regardless of the number of VLANs.
Per-VLAN Spanning Tree (PVST+)—PVST+ is a Cisco enhancement of STP that provides a separate 802.1D spanning-tree instance for each VLAN configured in the network.
Rapid Spanning Tree Protocol (RSTP)—RSTP is defined in IEEE 802.1w. It is an evolution of STP that provides faster convergence than STP.
Rapid Per-VLAN Spanning Tree (Rapid PVST+)—Rapid PVST+ is a Cisco enhancement of RSTP that uses PVST+ and provides a separate instance of 802.1w for each VLAN.
Multiple Spanning Tree Protocol (MSTP)—MSTP, defined in IEEE 802.1s, maps multiple VLANs into the same spanning-tree instance. The Cisco implementation of MSTP is often referred to as Multiple Spanning Tree (MST).
A network professional whose duties include switch administration may be required to decide which type of spanning-tree protocol to implement.
Characteristics of the Spanning Tree Protocols (3.2.1.2)
Table 3-3 lists the characteristics of the various STP versions.
Table 3-3 Spanning Tree Protocol Characteristics
| STP Version | Characteristics |
|---|---|
| STP |
|
| PVST+ |
|
| RSTP |
|
| Rapid PVST+ |
|
| MSTP |
|
Table 3-4 summarizes the STP characteristics.
Table 3-4 Comparing Spanning Tree Protocols
| Protocol | Standard | Resources Needed | Convergence | STP Tree Calculation |
|---|---|---|---|---|
| STP | IEEE 802.1D | Low | Slow | All VLANs |
| PVST+ | Cisco | High | Slow | Per VLAN |
| RSTP | IEEE 802.1w | Medium | Fast | All VLANs |
| Rapid PVST+ | Cisco | High | Fast | Per VLAN |
| MSTP (MST) | IEEE 802.1s, Cisco | Medium or high | Fast | Per instance |
Cisco switches running IOS 15.0 or later run PVST+ by default.
Cisco Catalyst switches support PVST+, Rapid PVST+, and MSTP. However, only one version can be active at any time.
PVST+ (3.2.2)
The focus of this topic is on how the default mode of PVST+ on Cisco Catalyst switches operates.
Overview of PVST+ (3.2.2.1)
The original IEEE 802.1D standard defines only one spanning-tree instance for the entire switched network, regardless of the number of VLANs. A network running 802.1D has these characteristics:
No load sharing is possible. One uplink must block for all VLANs.
The CPU is spared. Only one instance of spanning tree must be computed.
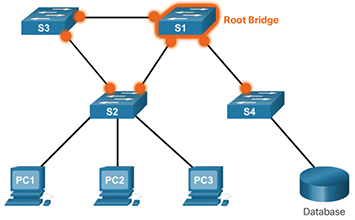
Cisco developed PVST+ so that a network can run an independent instance of the Cisco implementation of IEEE 802.1D for each VLAN in the network. A PVST+ topology is shown in Figure 3-32.
With PVST+, it is possible for one trunk port on a switch to block for a VLAN while forwarding for other VLANs. PVST+ can be used to manually implement Layer 2 load balancing. The switches in a PVST+ environment require greater CPU process and BPDU bandwidth consumption than a traditional STP because each VLAN runs a separate instance of STP.
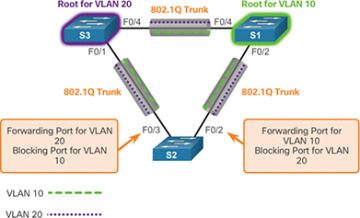
Figure 3-32 PVST+
In a PVST+ environment, spanning-tree parameters can be tuned so that half of the VLANs forward on each uplink trunk. In Figure 3-32, port F0/3 on S2 is the forwarding port for VLAN 20, and F0/2 on S2 is the forwarding port for VLAN 10. This is accomplished by configuring one switch to be elected the root bridge for half of the VLANs in the network and a second switch to be elected the root bridge for the other half of the VLANs. In the figure, S3 is the root bridge for VLAN 20, and S1 is the root bridge for VLAN 10. Having multiple STP root bridges per VLAN increases redundancy in the network.
Networks running PVST+ have these characteristics:
Optimum load balancing can result.
One spanning-tree instance for each VLAN maintained can mean a considerable waste of CPU cycles for all the switches in the network (in addition to the bandwidth that is used for each instance to send its own BPDU). This is problematic only if a large number of VLANs are configured.
Port States and PVST+ Operation (3.2.2.2)
STP facilitates the logical loop-free path throughout the broadcast domain. The spanning tree is determined through the information learned by the exchange of the BPDU frames between the interconnected switches. To facilitate the learning of the logical spanning tree, each switch port transitions through five possible port states and three BPDU timers.
The spanning tree is determined immediately after a switch is finished booting up. If a switch port transitions directly from the blocking state to the forwarding state without information about the full topology during the transition, the port can temporarily create a data loop. For this reason, STP introduced five port states that PVST+ uses as well. Table 3-5 lists and explains the five port states.
Table 3-5 STP Port States
| Port State | Characteristics |
|---|---|
| Blocking state |
|
| Listening state |
|
| Learning state |
|
| Forwarding state |
|
| Disabled state |
|
Table 3-6 summarizes the port states which ensure that no loops are created during the creation of the logical spanning tree.
Table 3-6 Port States
| Operation Allowed | Port State | ||||
|---|---|---|---|---|---|
| Blocking | Listening | Learning | Forwarding | Disabled | |
| Can receive and process BPDUs | Yes | Yes | Yes | No | No |
| Can forward data frames received on the interface | No | No | No | Yes | No |
| Can forward data frames switched from another interface | No | No | No | Yes | No |
| Can learn MAC addresses | No | No | Yes | Yes | No |
Note that the number of ports in each of the various states (blocking, listening, learning, or forwarding) can be displayed with the show spanning-tree summary command.
For each VLAN in a switched network, PVST+ performs four steps to provide a loop-free logical network topology:
Step 1. It elects one root bridge. Only one switch can act as the root bridge (for a given VLAN). The root bridge is the switch with the lowest bridge ID. On the root bridge, all ports are designated ports (no root ports).
Step 2. It selects the root port on each non-root bridge. PVST+ establishes one root port on each non-root bridge for each VLAN. The root port is the lowest-cost path from the non-root bridge to the root bridge, which indicates the direction of the best path to the root bridge. Root ports are normally in the forwarding state.
Step 3. It selects the designated port on each segment. On each link, PVST+ establishes one designated port for each VLAN. The designated port is selected on the switch that has the lowest-cost path to the root bridge. Designated ports are normally in the forwarding state and forwarding traffic for the segment.
Step 4. It makes the remaining ports in the switched network alternate ports. Alternate ports normally remain in the blocking state to logically break the loop topology. When a port is in the blocking state, it does not forward traffic, but it can still process received BPDU messages.
Extended System ID and PVST+ Operation (3.2.2.3)
In a PVST+ environment, the extended system ID (see Figure 3-33) ensures that each switch has a unique BID for each VLAN.
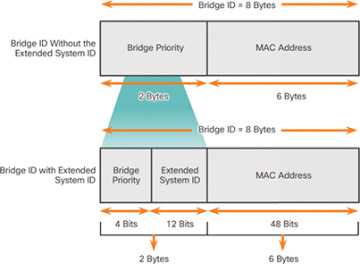
Figure 3-33 PVST+ and the Extended System ID
For example, the VLAN 2 default BID would be 32770 (priority 32768, plus the extended system ID 2). If no priority has been configured, every switch has the same default priority, and the election of the root bridge for each VLAN is based on the MAC address. Because the bridge ID is based on the lowest MAC address, the switch chosen to be root bridge might not be the most powerful or the most optimal switch.
In some situations, an administrator may want a specific switch to be selected as the root bridge. This may be for a variety of reasons, including the following:
The switch is more optimally located within the LAN design in regards to the majority of traffic flow patterns for a particular VLAN.
The switch has higher processing power.
The switch is simply easier to access and manage remotely.
To manipulate the root-bridge election, assign a lower priority to the switch that should be selected as the root bridge for the desired VLAN(s).
Rapid PVST+ (3.2.3)
The focus of this topic is on how Rapid PVST+ operates.
Overview of Rapid PVST+ (3.2.3.1)
RSTP (IEEE 802.1w) is an evolution of the original 802.1D standard and is incorporated into the IEEE 802.1D-2004 standard. The 802.1w STP terminology remains primarily the same as the original IEEE 802.1D STP terminology. Most parameters have been left unchanged, so users who are familiar with STP can easily configure the new protocol. Rapid PVST+ is the Cisco implementation of RSTP on a per-VLAN basis. An independent instance of RSTP runs for each VLAN.
Figure 3-34 shows a network running RSTP. S1 is the root bridge, with two designated ports in a forwarding state. RSTP supports a new port type. Port F0/3 on S2 is an alternate port in discarding state. Notice that there are no blocking ports. RSTP does not have a blocking port state. RSTP defines port states as discarding, learning, or forwarding.
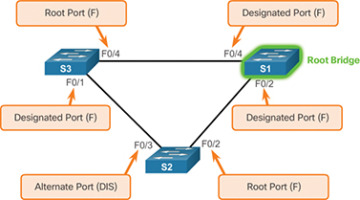
Figure 3-34 RSTP Topology
RSTP speeds the recalculation of the spanning tree when the Layer 2 network topology changes. RSTP can achieve much faster convergence in a properly configured network—sometimes in as little as a few hundred milliseconds.
RSTP redefines the types of ports and their states. If a port is configured to be an alternate port or a backup port, it can immediately change to a forwarding state without waiting for the network to converge.
The following is a brief description of RSTP characteristics:
RSTP is the preferred protocol for preventing Layer 2 loops in a switched network environment. Many of the differences were established by Cisco proprietary enhancements to the original 802.1D. These enhancements, such as BPDUs carrying and sending information about port roles only to neighboring switches, require no additional configuration and generally perform better than the earlier Cisco proprietary versions. They are now transparent and integrated into the protocol’s operation.
RSTP (802.1w) supersedes the original 802.1D while retaining backward compatibility. Much of the original 802.1D terminology remains, and most parameters are unchanged. In addition, 802.1w is capable of reverting to legacy 802.1D to interoperate with legacy switches on a per-port basis. For example, the RSTP spanning-tree algorithm elects a root bridge in exactly the same way as the original 802.1D.
RSTP keeps the same BPDU format as the original IEEE 802.1D, except that the version field is set to 2 to indicate RSTP, and the flags field uses all 8 bits.
RSTP is able to actively confirm that a port can safely transition to the forwarding state without having to rely on a timer configuration.
RSTP BPDUs (3.2.3.2)
RSTP uses type 2, Version 2 BPDUs. The original 802.1D STP uses type 0, Version 0 BPDUs. However, a switch running RSTP can communicate directly with a switch running the original 802.1D STP. RSTP sends BPDUs and populates the flags byte in a slightly different manner than in the original 802.1D:
Protocol information can be immediately aged on a port if hello packets are not received for three consecutive hello times (six seconds, by default) or if the max age timer expires.
BPDUs are used as a keepalive mechanism. Therefore, three consecutively missed BPDUs indicate lost connectivity between a bridge and its neighboring root or designated bridge. The fast aging of the information allows failures to be detected quickly.
As shown in Figure 3-35, RSTP uses the flags byte of a Version 2 BPDU:

Figure 3-35 RSTP BPDU Fields
Bits 0 and 7 are used for topology change and acknowledgment. They are in the original 802.1D.
Bits 1 and 6 are used for the proposal agreement process (used for rapid convergence).
Bits 2 to 5 encode the role and state of the port.
Bits 4 and 5 are used to encode the port role using a 2-bit code.
Edge Ports (3.2.3.3)
An RSTP edge port is a switch port that is never intended to be connected to another switch. It immediately transitions to the forwarding state when enabled.
The RSTP edge port concept corresponds to the PVST+ PortFast feature. An edge port is directly connected to an end station and assumes that no switch device is connected to it. RSTP edge ports should immediately transition to the forwarding state, thereby skipping the time-consuming original 802.1D listening and learning port states.
The Cisco RSTP implementation (Rapid PVST+) maintains the PortFast keyword, using the spanning-tree portfast command for edge port configuration. This makes the transition from STP to RSTP seamless.
Figure 3-36 shows examples of ports that can be configured as edge ports.
Figure 3-37 shows examples of ports that are non-edge ports.
Link Types (3.2.3.4)
The link type provides a categorization for each port participating in RSTP by using the duplex mode on the port. Depending on what is attached to each port, two different link types can be identified:
Point-to-point—A port operating in full-duplex mode typically connects a switch to a switch and is a candidate for a rapid transition to a forwarding state.
Shared—A port operating in half-duplex mode connects a switch to a hub that attaches multiple devices.
Figure 3-38 displays the various RSTP port assignments.
The link type can determine whether the port can immediately transition to a forwarding state, assuming that certain conditions are met. These conditions are different for edge ports and non-edge ports. Non-edge ports are categorized into two link types: point-to-point and shared.
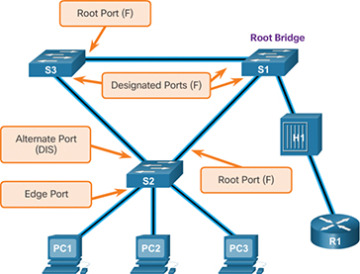
Figure 3-38 Link Types
The link type is automatically determined but can be overridden with an explicit port configuration, using the spanning-tree link-type { point-to-point | shared } command.
Characteristics of port roles, with regard to link types, include the following:
Edge port connections and point-to-point connections are candidates for rapid transition to a forwarding state. However, before the link-type parameter is considered, RSTP must determine the port role.
Root ports do not use the link-type parameter. Root ports are able to make a rapid transition to the forwarding state as soon as the port is in sync (that is, receives a BPDU from the root bridge).
Alternate and backup ports do not use the link-type parameter in most cases.
Designated ports make the most use of the link-type parameter. A rapid transition to the forwarding state for the designated port occurs only if the link-type parameter is set to point-to-point.