Spanning Tree Configuration (3.3)
In this section, you will learn how to implement PVST+ and Rapid PVST+ in a switched LAN environment.
PVST+ Configuration (3.3.1)
The focus of this topic is on how to configure PVST+ in a switched LAN environment.
Catalyst 2960 Default Configuration (3.3.1.1)
Table 3-7 shows the default spanning-tree configuration for a Cisco Catalyst 2960 Series switch. Notice that the default spanning-tree mode is PVST+.
Table 3-7 Default Switch Configuration
| Feature | Default Setting |
|---|---|
| Enable state | Enabled on VLAN 1 |
| Spanning-tree mode | PVST+ (Rapid PVST+ and MSTP are disabled.) |
| Switch priority | 32768 |
| Spanning-tree port priority (configurable on a per-interface basis) | 128 |
| Spanning-tree port cost (configurable on a per-interface basis) | 1000 Mbps: 4 |
| 100 Mbps: 19 | |
| 10 Mbps: 100 | |
| Spanning-tree VLAN port priority (configurable on a per-VLAN basis) | 128 |
| Spanning-tree VLAN port cost (configurable on a per-VLAN basis) | 1000 Mbps: 4 |
| 100 Mbps: 19 | |
| 10 Mbps: 100 | |
| Spanning-tree timers | Hello time: 2 seconds |
| Forward-delay time: 15 seconds | |
| Maximum-aging time: 20 seconds | |
| Transmit hold count: 6 BPDUs |
Configuring and Verifying the Bridge ID (3.3.1.2)
When an administrator wants a specific switch to become a root bridge, the bridge priority value must be adjusted to ensure that it is lower than the bridge priority values of all the other switches on the network. There are two different methods to configure the bridge priority value on a Cisco Catalyst switch.
Method 1
To ensure that a switch has the lowest bridge priority value, use the spanning-tree vlan vlan-id root primary command in global configuration mode. The priority for the switch is set to the predefined value of 24,576 or to the highest multiple of 4096 less than the lowest bridge priority detected on the network.
If an alternate root bridge is desired, use the spanning-tree vlan vlan-id root secondary global configuration mode command. This command sets the priority for the switch to the predefined value 28,672. This ensures that the alternate switch becomes the root bridge if the primary root bridge fails. This assumes that the rest of the switches in the network have the default 32,768 priority value defined.
In Figure 3-39, S1 has been assigned as the primary root bridge, using the spanning-tree vlan 1 root primary command, and S2 has been configured as the secondary root bridge, using the spanning-tree vlan 1 root secondary command.
Method 2
Another method for configuring the bridge priority value is by using the spanning-tree vlan vlan-id priority value global configuration mode command. This command gives more granular control over the bridge priority value. The priority value is configured in increments of 4096 between 0 and 61,440.
In the example in Figure 3-39, S3 has been assigned a bridge priority value of 24,576, using the spanning-tree vlan 1 priority 24576 command.

Figure 3-39 Configuring the Bridge ID
To verify the bridge priority of a switch, use the show spanning-tree command. In Example 3-4, the priority of the switch has been set to 24,576. Also notice that the switch is designated as the root bridge for the spanning-tree instance.
Example 3-4 Verifying the Root Bridge and BID
S3# show spanning-tree
VLAN0001
Spanning tree enabled protocol ieee
Root ID Priority 24577
Address 000A.0033.0033
This bridge is the root
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 24577 (priority 24576 sys-id-ext 1)
Address 000A.0033.3333
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 300
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- ------------------------
Fa0/1 Desg FWD 4 128.1 P2p
Fa0/2 Desg FWD 4 128.2 P2p
PortFast and BPDU Guard (3.3.1.3)
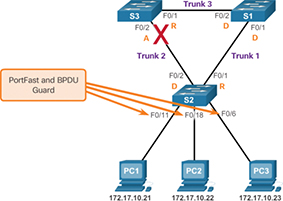
PortFast is a Cisco feature for PVST+ environments. When a switch port is configured with PortFast, that port transitions from blocking to forwarding state immediately, bypassing the usual 802.1D STP transition states (the listening and learning states). As shown in Figure 3-40, you can use PortFast on access ports to allow these devices to connect to the network immediately rather than wait for IEEE 802.1D STP to converge on each VLAN. Access ports are ports that are connected to a single workstation or to a server.
In a valid PortFast configuration, BPDUs should never be received because that would indicate that another bridge or switch is connected to the port, potentially causing a spanning-tree loop. Cisco switches support a feature called BPDU guard. When it is enabled, BPDU guard puts the port in an errdisabled (error-disabled) state on receipt of a BPDU. This effectively shuts down the port. The BPDU guard feature provides a secure response to invalid configurations because you must manually put the interface back into service.
Cisco PortFast technology is useful for DHCP. Without PortFast, a PC can send a DHCP request before the port is in forwarding state, denying the host from getting a usable IP address and other information. Because PortFast immediately changes the state to forwarding, the PC always gets a usable IP address (if the DHCP server has been configured correctly and communication with the DHCP server has occurred).
To configure PortFast on a switch port, enter the spanning-tree portfast interface configuration mode command on each interface on which PortFast is to be enabled, as shown in Example 3-5.
Example 3-5 Configuring PortFast
S2(config)# interface FastEthernet 0/11 S2(config-if)# spanning-tree portfast %Warning: portfast should only be enabled on ports connected to a single host. Connecting hubs, concentrators, switches, bridges, etc... to this interface when portfast is enabled, can cause temporary bridging loops. Use with CAUTION %Portfast has been configured on FastEthernet0/11 but will only have effect when the interface is in a non-trunking mode. S2(config-if)#
The spanning-tree portfast default global configuration mode command enables PortFast on all non-trunking interfaces.
To configure BPDU guard on a Layer 2 access port, use the spanning-tree bpduguard enable interface configuration mode command, as shown in Example 3-6.
Example 3-6 Configuring and Verifying BPDU Guard
S2(config-if)# spanning-tree bpduguard enable S2(config-if)# end S2# S2# show running-config interface f0/11 interface FastEthernet0/11 spanning-tree portfast spanning-tree bpduguard enable S2#
The spanning-tree portfast bpduguard default global configuration command enables BPDU guard on all PortFast-enabled ports.
Notice in Example 3-6 how the show running-config interface command can be used to verify that PortFast and BPDU guard have been enabled for a switch port. PortFast and BPDU guard are disabled, by default, on all interfaces.
PVST+ Load Balancing (3.3.1.4)
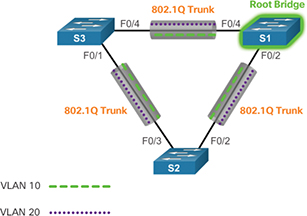
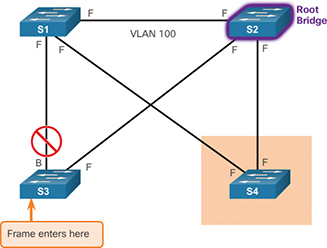
The topology in Figure 3-41 shows three switches with 802.1Q trunks connecting them.
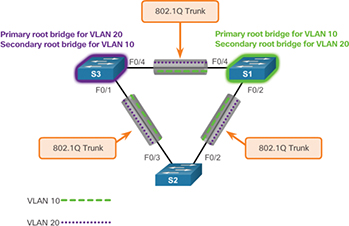
Figure 3-41 PVST+ Configuration Topology
Two VLANs, 10 and 20, are being trunked across these links. The goal is to configure S3 as the root bridge for VLAN 20 and S1 as the root bridge for VLAN 10. Port F0/3 on S2 is the forwarding port for VLAN 20 and the blocking port for VLAN 10. Port F0/2 on S2 is the forwarding port for VLAN 10 and the blocking port for VLAN 20.
In addition to establishing a root bridge, it is also possible to establish a secondary root bridge. A secondary root bridge is a switch that may become the root bridge for a VLAN if the primary root bridge fails. Assuming that the other bridges in the VLAN retain their default STP priority, this switch becomes the root bridge if the primary root bridge fails.
Configuring PVST+ on this topology involves the following steps:
Step 1. Select the switches you want for the primary and secondary root bridges for each VLAN. For example, in Figure 3-41, S3 is the primary bridge for VLAN 20, and S1 is the secondary bridge for VLAN 20.
Step 2. As shown in Example 3-7, configure S3 to be a primary bridge for VLAN 10 and the secondary bridge for VLAN 20 by using the spanning-tree vlan number root { primary | secondary } command.
Example 3-7 Configuring Primary and Secondary Root Bridges for Each VLAN on S3
S3(config)# spanning-tree vlan 20 root primary S3(config)# spanning-tree vlan 10 root secondary
Step 3. As shown in Example 3-8, configure S1 to be a primary bridge for VLAN 20 and the secondary bridge for VLAN 10.
Example 3-8 Configuring Primary and Secondary Root Bridges for Each VLAN on S1
S1(config)# spanning-tree vlan 10 root primary S1(config)# spanning-tree vlan 20 root secondary
Another way to specify the root bridge is to set the spanning-tree priority on each switch to the lowest value so that the switch is selected as the primary bridge for its associated VLAN, as shown in Example 3-9.
Example 3-9 Configuring the Lowest Possible Priority to Ensure That a Switch Is Root
S3(config)# spanning-tree vlan 20 priority 4096
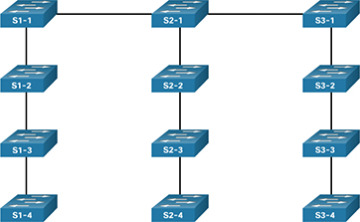
Switch stacks help maintain or reduce the impact of diameter on STP reconvergence. In a switch stack, all switches use the same bridge ID for a given spanning-tree instance. This means that, if the switches are stacked, as shown in Figure 3-51, the maximum diameter becomes 3 instead of 9.

Figure 3-51 Switch Stacking Reduces STP Diameter