Standards for NFV, SDN, and Data Modeling for Services
A 2015 Gartner report recommends a number of principles for IoT solutions architects:
Design IoT solutions for software-defined things, leveraging a software-defined architecture.
Build up the technology skills and expertise for the management of large-scale, automated, event-driven systems.
Invest in technology and expertise in virtualization and software portability, including containerized microservices.
Choose platforms that offer agility, extensibility, and openness.
These relate directly to the capabilities of NFV and SDN and the level of flexibility, programmability, and automation they provide. NFV and SDN are often used interchangeably, but they are two very distinct technology areas. However, combining them in discussion can bring additional value to some of the complex IoT challenges, as you will see in later chapters of this book. Interestingly, as with IoT, no single standards body exists for NFV or SDN. The SDX Central research repository monitors organizations and standards bodies that exist to enhance SDN, NFV, and NV (network virtualization) adoption and implementation. Its annual report in 2016 listed 138 different organizations. However, we do see a lot of interoperability and openness in the industry to allow different vendor solutions to come together. Not only do we continue to see adoption in the service provider and enterprise spaces, but there is a trend for adoption in the ever-growing IoT space because of the flexibility and features they provide over traditional static network architectures.
Chapter 6, “Evolution and Benefits of SDX and NFV Technologies and Their Impact on IoT,” covers NFV and SDN in detail but a brief overview is provided here to give some context in terms of the technology and standards.
Network functions virtualization (NFV) offers a standardized way to architect, implement, and manage networking services. (As we highlight later in this chapter, this can also be extended to other services beyond the network.) The concept involves replacing dedicated network infrastructure devices such as routers and firewalls with standard servers, switches, storage, cloud, or even a fog/edge computing infrastructure. NFV decouples network functions such as routing, switching, and security from proprietary or dedicated hardware appliances, to allow them to run in software.
The aim is to leverage standard IT virtualization technologies to consolidate hardware and to virtualize network functions into building blocks that can connect or chain together to create end-to-end communication services. This can be realized for any control plane function or data plane processing in wired and wireless network environments.
NFV was really born in 2012 when seven of the leading global network service providers came together under the ETSI Industry Specification Group for NFV. This is the main group for developing the requirements and architecture for virtualization for various functions within telecom networks and for the architectural standards for NFV, such as the NFV MANO (Management and Orchestration) architecture. It has become the de facto standard for NFV.
The NFV framework has three main components, as Figure 4-3 shows. The Virtualized Network Functions (VNF) are network functions that are implemented in software and can be deployed in a network functions virtualization infrastructure (NFVI). The NFVI is the overall hardware and software components where VNFs are deployed. The NFV management and orchestration (MANO) environment is the architectural framework that contains the functional blocks, data repositories used by these blocks, and interfaces through which the functional blocks exchange information for the purpose of managing and orchestrating NFVI and VNFs.
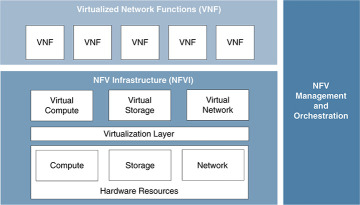
Figure 4-3 Network Functions Virtualization Overview
Software-defined networking (SDN) is an approach to design, build, and operate networks by separating the control and data forwarding planes. This enables the network to become directly programmable and dynamic, and it abstracts the lower-level infrastructure functionality. The term arose in the mid-1990s. However, it really became established in 2011 when the Open Networking Foundation was founded to promote SDN and used OpenFlow as the key protocol to describe how to make changes to the network in a standardized way. SDN and OpenFlow are sometimes used interchangeably, but this is inaccurate. OpenFlow is a protocol, and other communication mechanisms can be used to deliver SDN capabilities.
Several different architectures separate the control logic to off-device resources, but all SDN approaches include an SDN controller and both southbound and northbound APIs (see Figure 4-4).
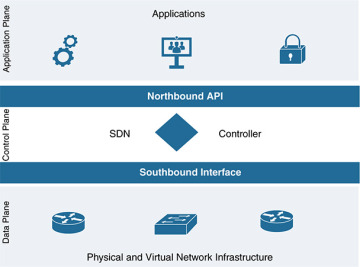
Figure 4-4 Software-Defined Networking Architecture Overview
With the close alignment of NFV and SDN as advanced technology areas, some groups are concerned with standards and best practice for SDN, NFV, or often both. The following is a compilation of the key groups and their focus areas, listed alphabetically.
The Alliance for Telecommunications Industry Solutions (ATIS; http://www.atis.org/) SDN and NFV Focus Group was launched in January 2014, with a focus on the service chaining of hardware/NFV appliances using SDN concepts. This includes developing application interface APIs and OAM interface APIs for service chaining in an OpenStack and OpenDaylight framework.
The Broadband Forum Member (BBF; https://www.broadband-forum.org/) works on both SDN and NFV, with a focus of delivering cloud-based broadband and NFV into the home via service provider networks. In 2017, the BBF entered into a memorandum of understanding (MoU) with the SDN/NFV Industry Alliance to promote the development of network transformation and cloud evolution.
The European Telecommunications Standards Institute (ETSI; http://www.etsi.org/technologies-clusters/technologies/nfv) is the main global driver for NFV. The NFV group was founded in November 2012 by seven leading telecoms operators, and ISG NFV became the home of the Industry Specification Group for NFV.
The Institute of Electrical and Electronics Engineers (IEEE; https://sdn.ieee.org/) has standardization efforts for SDN underway via two research groups and two study groups. It is examining standardization opportunities in software-defined networks, network functions virtualization, and related areas. The IEEE currently has produced eight standards for SDN.
The International Council on Large Electrical Systems (CIGRE; http://www.cigre.org/) has a working group focused on developing the IEEE P1915.1 standard, which specifies the security framework, models, analytics, and requirements for SDN/NFV. CIGRE seeks to understand and address security models, terminology, and analytics (essential components of SDN and NFV environments) to ensure confidentiality, integrity, and availability. It also aims to produce a framework of guidelines for the procurement, deployment, and management of SDN and NFV technologies.
The International Telecommunication Union Telecommunication Standardization Sector (ITU-T; http://www.itu.int/en/ITU-T/sdn/Pages/default.aspx) has focused on SDN since November 2012. The ITU-T has adopted Resolution 77 to push for standardization in SDN and also performs SDN-focused work in the group WTSA-12.
The Internet Engineering Taskforce (IETF; https://ietf.org) is working on both SDN (through RFC 7426 SDN) and a new IETF SDN standards group (I2RS), to work on southbound programming protocols and NFV and network service chains.
The Internet Research Task Force (IRTF; https://irtf.org/concluded/sdnrg) has an SDN group whose aim is to benefit all types of networks, including wireless, cellular, home, enterprise, data centers, and wide-area networks. The Software-Defined Networking Research Group (SDNRG) seeks to identify approaches that can be defined, deployed, and used in the near term, as well identify future research challenges. Key areas of interest include solution scalability, abstractions, and programming languages and paradigms that are particularly useful in the context of SDN. It also provides a forum for researchers to investigate problems in the SDN field, and it provides direct input into standards for other groups, such as ETSI, the IETF and the IEEE.
The Internet Society (ISOC; https://www.internetsociety.org/) has IRTF and IETF groups that focus on NFV and SDN and provide architectural oversight to the Internet Architecture Board (IAB; https://www.iab.org/).
The Metro Ethernet Forum (MEF; https://mef.net/), founded in 2001, facilitates industry-neutral implementation environments for service orchestration (OpenLSO) and L2–L7 connectivity services (OpenCS) based on technologies such as SDN and NFV. Its goal is to develop agile, assured, and orchestrated services for the digital economy and the hyperconnected world.
The Open Data Centre Alliance (ODCA; https://opendatacenteralliance.org/) was established in October 2010. ODCA is driving a federated cloud architecture with common standards for both hardware and software. It focuses on the widespread adoption of enterprise cloud computing through best practice sharing and collaboration. ODCA has work groups for both SDN and NFV and includes organizations such as BMW, Royal Dutch Shell, and Marriott Hotels.
OpenDaylight (https://www.opendaylight.org/) promotes an open source SDN platform for building programmable and flexible networks. The OpenDaylight Foundation was formed in 2013 and consists of solution providers, individual developers, and end users that include service providers, enterprises, and universities.
The Open Networking Foundation (ONF; https://www.opennetworking.org/) is a nonprofit, user-driven organization dedicated to accelerating the adoption of SDN and NFV. The ONF really drove the SDN movement in 2011; it includes companies such as Deutsche Telekom, Facebook, Google, Microsoft, Verizon, and Yahoo! that aim to standardize SDN and OpenFlow. In 2017, ONF announced an Open Innovation Pipeline to guide the industry toward the next generation of SDN and NFV. Network device disaggregation, open source platforms, and software-defined standards are key priorities.
The Open Platform for NFV (OPNFV; https://www.opnfv.org), formed in 2014 by the Linux foundation, facilitates the development and evolution of NFV components for open source ecosystems. OPNFV created a reference platform through system-level integration, deployment, and testing, to accelerate the transformation of enterprise and service provider networks. Members include AT&T, Juniper, Brocade, China Mobile, Cisco, Dell, Ericsson, IBM, and Intel.
The Optical Internetworking Forum (OIF; http://www.oiforum.com/) has an architecture and signaling working group that is defining interfaces for SDN.
Data Modeling and Services
Data modeling is the process of creating a data model for an information system by applying formal methodologies to model data in a standard, consistent, and predictable way so that it can be managed as a resource. As with everything else, data modeling has a number of competing standards. A data modeling language is required to standardize how we describe and create capabilities and how we can deploy this as a service. For automation and scale into an open heterogenous environment in which any service from any vendor might need to be deployed into any device, we need to leverage a standards-based, model-driven, service-centric approach. This must abstract the service intention from the service instantiation and also separate the instantiation from the devices services will be deployed in. This means being open to device type (multivendor) and also to where the device is deployed (edge, fog, network, data center, or cloud). The standard must also be understood and processed by an NFV- and SDN-based orchestration system.
Many debates have questioned the best choice of modeling language for services in NFV and SDN environments. Typically, the choice comes down to YANG or TOSCA. Both have merits and strengths, but in the context of IoT, with a potentially widely distributed environment with multiple devices from multiple vendors and an architecture that could be very non–cloud focused, YANG has the best applicability. Indeed, YANG has become the standard data modeling language of choice in all environments for a number of reasons, including its applicability throughout an automation and orchestration stack:
Network infrastructure
Data plane programmability
Operating systems
Controller programmability
Cloud and virtualization management
Orchestration and policy
In addition, we have recently seen some of the first IoT- and fog-specific YANG models created for customer implementations in smart cities, automotive manufacturing, oil and gas, and power utilities. All are orchestrated and automated to deliver end-to-end secure customer use cases, leveraging the NFV- and SDN-based platform we describe in Chapter 8. We highlight this new approach later in this section, to show the additional flexibility and capability of YANG.
The IETF uses YANG to specify models, and YANG is also used in many standards-development organizations (SDO), consortia, and open source projects, including the Broadband Forum, IEEE, ITU, MEF, and OpenDaylight, among others. As a data modeling language, YANG is used to model configuration and state data manipulated by the NETCONF network configuration protocol. Figure 4-5 shows an overview of YANG.
YANG can be used to model both configuration data and the state data of network elements, in addition to event notifications from network elements. Data modelers thus can define remote procedure calls that can be invoked on network elements via the IETF standardized NETCONF protocol. YANG is protocol independent and can be converted into any encoding format, such as XML or JSON, that the configuration process supports.
YANG models have traditionally been used to describe networking capabilities and device configurations that leverage the NETCONF protocol. However, it is flexible and powerful enough to be extended to other areas of service definition. As mentioned earlier in this chapter, for IoT, it is essential to include the fog and edge devices, the data pipeline, service assurance, multitenancy, and additional security (see Figure 4-6). The flexibility of YANG enables the extension of the ETSI MANO architecture to encompass these additional areas and address the entire IoT stack.
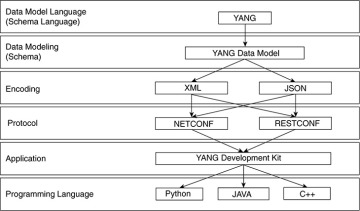
Figure 4-5 YANG Model Overview
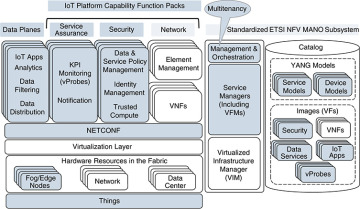
Figure 4-6 Extending the ETSI MANO Architecture via YANG Service Models
In the advanced IoT orchestration and automation system that will be detailed in Chapter 8, YANG is the service model language leveraged for both device and service modeling. Chapter 8 outlines how the YANG model works and how the orchestration system leverages it to translate service intent, through to an automated deployment of the service for full use cases via service “function packs.” This includes automation capabilities for the complete IoT stack, including infrastructure, virtual network infrastructure, physical devices, virtual environments (VMware, Linux docker, and so on), service assurance, the data pipeline (message brokers, data transformation, and so on), applications and microservices, and, of course, security.