Specific Security Standards and Guidelines
This leads nicely into the focus area of the book: security. This section explores some of the challenges of standardizing security for the IoT. We look at some key standards and guidelines for security in IoT environments and conclude with some considerations for implementing these as part of the security perspectives discussed in Chapter 2. Standards are available for every layer of the IoT stack, such as Internet Protocol Security (IPsec), Transport Layer Security (TLS), and application layer cryptography. This section does not dive into the technologies themselves, but instead looks at the groups working on bringing technologies together into more of a cohesive approach to security for IoT.
As in the previous sections, standards for security are also widespread and diverse. Many applicable security standards exist, and traditional IT or OT best practices are already being leveraged in many cases. These will continue to be applicable for IoT. With many new security technologies being developed to address new use cases, technologies, and protocols, the landscape is still changing. Research from Forrester (see Figure 4-9) shows that this is set to continue for the foreseeable future, with multiple security requirements still developing for IoT.
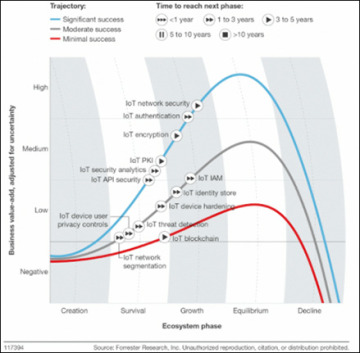
Figure 4-9 Forrester IoT Security Landscape
The following standards and guidelines have a specific focus on IoT security, either as an existing best practice that has been applied to the IoT space or as a new best practice generated by IoT demand. Again, these are listed alphabetically, not in order of importance.
The European Telecommunications Standards Institute (ETSI; http://www.etsi.org/news-events/news/1015-2015-10-news-etsi-nfv-isg-publishes-security-and-reliability-specifications) has several NFV-focused security areas:
Problem statement (NFV-SEC 001)
Cataloguing Security Features in Management Software Relevant to NFV (NFV-SEC 002)
Security and Trust Guidance (NFV-SEC 003)
Privacy and Regulation: Report on Lawful Interception (LI) Implications (NFV-SEC 004)
The Institute of Electrical and Electronics Engineers (IEEE; https://standards.ieee.org/develop/project/1915.1.html) P1915.1 standard for SDN and NFV provides a framework to build and operate secure SDN/NFV environments. This standard specifies a security framework, models, analytics, and requirements to secure SDN and NFV.
The IoT Security Foundation (https://iotsecurityfoundation.org/) was established in September 2015 to help secure IoT, accelerate adoption, and maximize potential benefits by providing knowledge and clear security best practices to those who specify, make, and use IoT products and systems.
The Open Web Application Security Project (OWASP; https://www.owasp.org/index.php/OWASP_Internet_of_Things_Project) was established to better understand the security issues associated with IoT and to enable better security decisions when building, deploying, or assessing IoT technologies. OWASP has ten IoT security projects to help with this: IoT Attack Surface Areas; IoT Vulnerabilities; Firmware Analysis; ICS/SCADA Software Weaknesses; Community Information; IoT Testing Guides; IoT Security Guidance; Principles of IoT Security; IoT Framework Assessment, Developer, Consumer and Manufacturer Guidance; and Design Principles.
The Online Trust Alliance (OTA; https://otalliance.org/), established in 2005, aims to educate users and develop and advance best practices and tools to enhance users’ security, privacy, and identity. OTA does this with data sharing and collaboration through working groups, committees, and training. OTA is also a member of other organizations committed to collaboration, law enforcement, and data sharing.
The Secure Technology Alliance (https://www.securetechalliance.org/?utm=scapop), formed in March 2017, is a multi-industry association working to stimulate the understanding, adoption, and widespread application of secure solutions, including smart cards, embedded chip technology, and related hardware and software. This includes secure technologies for authentication, commerce, and IoT to protect privacy and data. The Secure Technology Alliance was formerly called the Smart Card Alliance; it changed its name in March 2017.
IoT IAP (http://www.iotiap.com/), established in November 2016, addresses security challenges related to IoT. As a working paper, it outlines ideas and approaches to improve today’s security situation.
The Cloud Security Alliance (CSA; https://cloudsecurityalliance.org/) is a leading organization dedicated to defining and raising awareness of best practices to secure cloud computing environments. CSA offers cloud security-specific research, education, certification, events, and products, including ones focused on IoT.
I am the Cavalry (https://www.iamthecavalry.org/), formed in 2013, aims to ensure that technologies with the potential to impact public safety and human life are worthy of trust and focus on IoT. It accomplishes this in a number of ways, including education, outreach, and research.
The National Institute of Standards and Technologies (NIST; https://pages.nist.gov/cpspwg/) launched Cyber Physical Systems in 2014. The Cyber-Physical Systems Public Working Group (CPS PWG) focuses on Cyber-Physical Systems, or “smart” systems, that promise increased efficiency and interaction between computer networks and the physical world. It seeks to enable advances that improve the quality of life, including those in personalized healthcare, emergency response, traffic flow management, and electric power generation and delivery. CPS covers many IoT use cases and includes a consensus vocabulary and reference architecture to facilitate interoperability between elements and systems, as well as promote communication across the breadth of CPS. Timing, dependability, data interoperability, and security are considered first-order design principles for CPS.
The National Institute of Standards and Technologies (NIST; https://www.nist.gov/publications/guidelines-smart-grid-cybersecurity) launched its NISTIR 7628 guide-lines in September 2014. This three-volume report, Guidelines for Smart Grid Cybersecurity, presents an analytical framework that can be used to develop effective cybersecurity strategies based on specific characteristics, risks, and vulnerabilities. It provides methods and supporting information that acts as a guide for assessing risk and identifying and applying appropriate security requirements. This approach recognizes that the electric grid is changing from a relatively closed system to a complex, highly interconnected environment that includes IoT elements, and it advocates using cybersecurity requirements that also evolve accordingly.
The National Institute of Standards and Technologies (NIST; http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-160.pdf) publication SP 800-160 Systems Security Engineering, launched in November 2016, addresses IoT from an engineering-driven perspective and documents actions necessary to develop more defensible and survivable systems (including machine, physical, and human components). It also addresses the capabilities and services delivered by those systems.
The International Electrotechnical Commission (IEC; https://www.certsi.es/en/blog/iec62443-evolution-of-isa99) launched the IEC 62443 standard for Cyber Security for Industrial Control Systems in 2009, based on previous work from ISA99 that was started in 2007. IEC 62443 is the most widely adopted industrial security standard globally; it continues to evolve, particularly in areas such as IoT.
The International Electrotechnical Commission (IEC; http://iectc57.ucaiug.org/wg15public/Public%20Documents/White%20Paper%20on%20Security%20Standards%20in%20IEC%20TC57.pdf) launched the IEC 62351standard in 1999. Its focus is on data and communications security in power systems management, along with the associated information exchange. It consists of a series of standards, with a focus on end-to-end security.
The North American Electric Reliability Corporation (NERC: http://www.nerc.com/Pages/default.aspx) launched the Critical Infrastructure Protection regulations for bulk power in North America in 2007. NERC is regulated and requires legal compliance, including cybersecurity.
The IoT Global Council (https://www.iotglobalcouncil.com/), launched in May 2014, is a membership organization for new business leaders of the IoT industry. It focuses on IoT data and security.
The Internet Research Task Force (IRTF; https://www.ietfjournal.org/internet-of-things-standards-and-guidance-from-the-ietf/) has established security-related works with IoT relevance and focus, launched under the IETF. This includes working groups for DTLS In Constrained Environments (DICE), Authentication and Authorization for Constrained Environments (ACE), and Lightweight Implementation Guidance (LWIG).
The Industrial Internet Consortium (IIC; http://www.iiconsortium.org/IISF.htm) is an umbrella type standard with an industrial focus, and has produced a specific cybersecurity framework for the IIoT.
In addition to these established standards and best practices, new ones continue to emerge that focus on interoperability and standardization. A great example is Manufacturer Usage Description (MUD), which introduces a set of network capabilities that provide an additional layer of protection to devices connecting to the IoT system. The focus of this work is security related to smart objects, although it goes further than this. Again, YANG is used as a standardized model to generate and parse manufacturer usage descriptions. Network management systems retrieve these descriptions to instantiate security and communication policies associated with those devices. A manufacturer should know what a device is intended to do; for example, a light bulb should not be communicating with a voice server, but it should be communicating with its controller. The concept, then, is to use the manufacturer’s product knowledge to create network policy that can be easily understood and enforced. Put simply, an IoT system should be capable of automatically finding out what a device should be allowed to do and enforcing policies that prevent it from going beyond those limits. At the time of this writing, MUD is currently being reviewed via the standard RFC process; however, organizations (including Cisco) are already working on adoption.
As you have probably concluded from this chapter, many standards and approaches to standards exist for IoT and IoT security. Later chapters of this book zoom in on providing a standardized methodology to deploy and manage security in an open way, leveraging NFV and SDN and automation to ensure that the approach can scale. Instead of competing with existing IoT and security standards, this methodology will actually provide a way to orchestrate and automate the deployment of standards and guidelines, while also bringing a number of enhancements. Security, particularly for IoT, is a multifaceted and difficult challenge, and we will not likely see standards or best practices that completely (or even partly) eliminate the risks of cyber attacks against IoT devices and systems anytime soon. However, a standardized approach to the IoT system, and to the security of the system and by the system, can ensure that deployments meet and even exceed reasonable standards for security. This moves the focus of the approach away from individual devices (which vary greatly in terms of capability) and more toward system-level security (which can more uniformly be provided by an IoT platform).