Routing Protocols
As of Release 2.0, Cisco ACI supports the following routing mechanisms:
Static routing (supported for IPv4 and IPv6)
OSPFv2 for regular, stub, and not-so-stubby-area (NSSA) areas (IPv4)
OSPFv3 for regular, stub, and NSSA areas (IPv6)
EIGRP (IPv4 only)
iBGP (IPv4 and IPv6)
eBGP (IPv4 and IPv6)
Through the use of subinterfaces or SVIs, border leaf switches can provide L3 Out connectivity for multiple tenants with one physical interface.
Static Routing
Routers forward packets using either route information from route table entries that you manually configure or the route information that is calculated using dynamic routing algorithms.
Static routes, which define explicit paths between two routers, cannot be automatically updated; you must manually reconfigure static routes when network changes occur. Static routes use less bandwidth than dynamic routes. No CPU cycles are used to calculate and analyze routing updates.
Static routes should be used in environments where network traffic is predictable and where the network design is simple. Static routes should not be used in large, constantly changing networks because static routes cannot react to network changes.
Static routes are very easy to configure in ACI. When you configure your L3 Out, a routing protocol will not be selected. Later in the process when a node is defined, you will also define the static routes. When you define the static route, you will be able to modify the following parameters:
Prefix
Priority for the static route
Next hop and next hop priority (the absence of a next hop adds a null route)
Enable BFD
As you would expect, the configuration is very straightforward. This configuration does not exchange routes with neighboring devices. Static routes will need to be added on the neighboring devices as well, so that traffic has a return path.
Enhanced Interior Gateway Routing Protocol
Enhanced Interior Gateway Routing Protocol (EIGRP) was Cisco’s proprietary routing protocol, based on IGRP, but it’s now an open standard. EIGRP is a distance vector routing protocol, with optimizations to minimize routing instability incurred after topology changes and the use of bandwidth and processing power in the router. Most of the routing optimizations are based on the Diffusing Update Algorithm (DUAL), which guarantees loop-free operation and provides fast router convergence.
The EIGRP routing protocol is very easy to configure and manage. For this reason, EIGRP is widely deployed across Cisco customers and is supported in ACI. To become an EIGRP neighbor, three essential configuration values must be matched: active hello packets, autonomous system number (ASN), and K values. EIGRP may use five K values or metric components to select the best route for the routing table. These are Bandwidth, Load, Delay, Reliability, and MTU. By default, EIGRP uses only two components: Bandwidth and Delay. When you configure a routing protocol on the L3 Out connection, you will select EIGRP. It is at this point that the AS number is able to be configured, as shown in Figure 6-12.
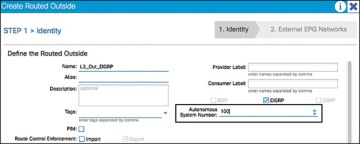
Figure 6-12 Configuring EIGRP on a Routed Outside Connection or L3 Out
During the configuration, you will add a node and interface profile. When the node and router ID are configured, avoid using the loopback. Loopbacks should be used only in BGP routing protocol configuration.
When the EIGRP interface profile is added, and the protocol profile is configured, ACI will ask for an EIGRP interface policy. It is here where the final K values (Bandwidth and Delay) will be configured. The EIGRP interface policy will then be applied to the interface that you choose in the next screens.
Open Shortest Path First
Open Shortest Path First (OSPF) is a routing protocol developed for IP networks by the Interior Gateway Protocol working group of the Internet Engineering Task Force (IETF). It was derived from several research efforts, including a version of OSI’s IS-IS routing protocol.
OSPF has two primary characteristics:
It is an open protocol. Its specification is in the public domain (RFC 1247).
It is based on the Shortest Path First (SPF) algorithm, sometimes known as the Dijkstra algorithm.
OSPF is a link-state routing protocol that calls for the sending of link-state advertisements (LSAs) to all other routers within the same hierarchical area. Information on attached interfaces, metrics used, and other variables are included in OSPF LSAs. As OSPF routers accumulate link-state information, they use the SPF algorithm to calculate the shortest path to each node.
OSPF is widely deployed in enterprises and is a go-to standard for open routing protocols. ACI supports external connectivity to external OSPF routers on OSPF normal areas, NSSA areas, and stub areas, including Area 0 (backbone area). Keep the following points in mind as you are configuring and using OSPF with ACI:
ACI border leafs running OSPF are always autonomous system boundary routers (ASBRs).
All external routes learned in OSPF are redistributed into MP-BGP.
MP-BGP routes are redistributed into OSPF as external Type-2 routes.
OSPF areas on different border leafs (border leaf pairs) are different OSPF areas, even if area IDs match, as shown in Figure 6-13.
Supports IPv4 (OSPFv2) and IPv6 (OSPFv3).
ACI border leaf switches follow OSPF protocol rules, as shown in Figure 6-14.
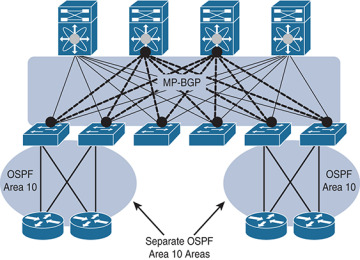
Figure 6-13 OSPF Areas on Different Border Leaf Switches Are Different OSPF Areas
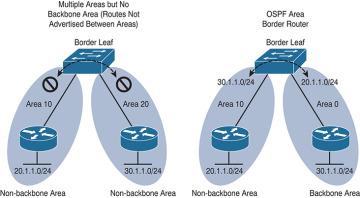
Figure 6-14 ACI Border Routers Follow Traditional OSPF Rules
When you configure a routing protocol on the L3 Out connection, you will select OSPF. It is at this point that the particulars of your OSPF area and the area number are configured, as shown in Figure 6-15.

Figure 6-15 Configuring the OSPF Area and Area ID for a Routed Outside or L3 Out
During the configuration, you will add a node and interface profile. When the node and router ID are configured, avoid using the loopback. Loopbacks should only be used in a BGP routing protocol configuration. When the OSPF interface profile is added, and the protocol profile is configured, ACI will ask for authentication information as well as an OSPF policy. The OSPF policy (see Figure 6-16) is where you can manage parameters such as the type of link (broadcast or point-to-point), passive participation, BFD, and MTU ignore. The OSPF interface policy will then be applied to the interface(s) you choose in the next screens.
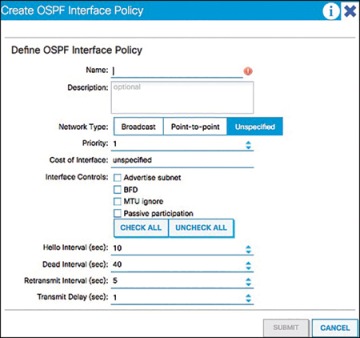
Figure 6-16 OSPF Interface Policy
OSPF Summarization
For OSPF route summarization, two options are available: external route summarization (equivalent to the summary-address configuration in Cisco IOS Software and Cisco NX-OS Software) and inter-area summarization (equivalent to the area range configuration in Cisco IOS Software and NX-OS).
When tenant routes or transit routes are injected into OSPF, the Cisco ACI leaf node where the L3 Out connection resides is acting as an OSPF autonomous system boundary router (ASBR). In this case, the summary-address configuration (that is, external route summarization) should be used. Figure 6-17 illustrates this concept.
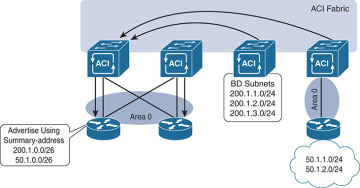
Figure 6-17 OSPF Summary-Address Operation
For scenarios where there are two L3 Out connections, each using a different area and attached to the same border leaf switch, the area range configuration will be used to summarize, as shown in Figure 6-18.
The OSPF route summarization policy is used to determine whether the summarization will use the area range or summary-address configuration, as shown in Figure 6-19.
In this example, checking the Inter-Area Enabled box means that area range will be used for the summary configuration. If this box is unchecked, summary address will be used.
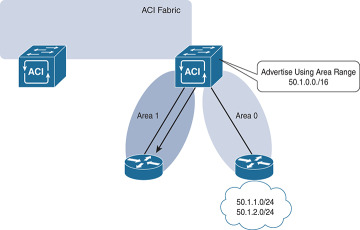
Figure 6-18 OSPF Area Range Operation
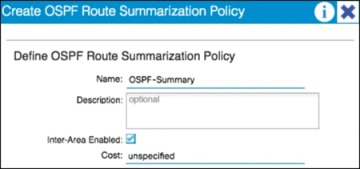
Figure 6-19 OSPF Route Summarization
Border Gateway Protocol
The Border Gateway Protocol (BGP) is an inter-autonomous system routing protocol. An autonomous system (AS) is a network or group of networks under common administration using common routing policies. BGP is used to exchange routing information for the Internet and is the protocol used between ISPs. Customer networks, such as universities and corporations, usually employ an interior gateway protocol (IGP) such as Routing Information Protocol (RIP), Enhanced Interior Gateway Routing Protocol (EIGRP), or Open Shortest Path First (OSPF) for the exchange of routing information within their networks. Customers connect to ISPs, and ISPs use BGP to exchange customer and ISP routes. When BGP is used between autonomous systems, the protocol is referred to as external BGP (eBGP). If a service provider is using BGP to exchange routes within an autonomous system, the protocol is referred to as interior BGP (iBGP).
Application Centric Infrastructure (ACI) has the capability to peer with external BGP networks and redistribute the routing information throughout the fabric. To use this functionality, you will have to select BGP as the routing protocol when you create the L3 routed outside connection. By default, ACI will use the ASN that was defined when the route reflectors were configured during fabric setup.
iBGP design best practices need to be followed for the iBGP deployment between the ACI border leaf switches and external routers. The ACI border leaf needs to have iBGP sessions with all BGP speakers within the AS. In cases where the route reflector technology is deployed, ACI border leaf switches need to have iBGP sessions with all route reflectors in the BGP Route Reflector cluster.
Notice that border leafs don’t have iBGP sessions among themselves. This is not required because border leaf switches can learn routes from each other through MP-BGP.
Unless you are using WAN integration, be sure to follow the VRF-lite best practices for the multitenant deployment scenarios. When the Layer 3 outside connection is required for each tenant, configure separate iBGP sessions for each tenant.
When you are configuring the routed outside connection, the BGP-specific configuration requires you to create a node profile with the following information:
Router IDs (for iBGP peering with external device) with static routes to the next-hop address. Note that a loopback should be created.
BGP peering details, such as the Neighbor IP.
The interface and interface profile you will use with port, IP, and VLAN encapsulation details.
A BGP peer connectivity profile, including the following:
Peer address
Authentication
Next you will create an external endpoint group. This group will represent all the devices (or a subset of devices) that are reachable through this L3 Out and BGP connection. Many enterprises use the subnet 0.0.0.0/0 to assign all external endpoints reachable via this link to the EPG that is being crafted.
Finally, in order to advertise prefixes from the fabric (leaf) to its neighbor, you need to associate the Layer 3 outside network with the bridge domain (which will create a route map) that contains the subnets you want to advertise. The subnets must be marked as advertised externally, and an application profile with an EPG linked to this bridge domain must be created. The public routes will then be advertised to all peers of the associated Layer 3 outside network.
BGP Route Profile
A route profile provides a control mechanism for routes with BGP peers. This can be viewed as a standard route map in the classic BGP configuration.
A route profile can be associated with any of the following:
Prefix
Bridge domain
Layer 3 outside network
When a route profile is associated with a bridge domain, all of the subnets under the bridge domain will be advertised with the same BGP community value. The software also allows the user to associate a route profile with a subnet of a bridge domain; this capability provides the flexibility to mark different BGP community values for different subnets. When a route profile is specified under both the bridge domain and the subnets of a bridge domain, the route profile under the subnet takes precedence.
A route profile with the name “default-export” can be configured and will be applied automatically to the Layer 3 outside network.
Outbound BGP Policy
The ACI border leaf switches support outbound BGP policy to set community or extended community values for tenant routes. The BGP community attributes (standard and extended) are commonly used by network architects to group together certain BGP routes and apply route policy by matching community values.
The following two types of communities are supported:
Standard community: regular:as2-nn2:<community_value>
regular:as2-nn2 is a keyword for the standard community.
Add a standard community value (for example 666:1001).
Extended community: extended:as4-nn2:<community_value>
extended:as4-nn2 is a keyword for the extended community.
Add a extended community value.
BGP Protocol Statistics
BGP protocol statistics can be viewed under Fabric > Inventory (see Figure 6-20). Investigate them by following these steps:
In the navigation pane, expand Pod ID > Leaf Switch ID > Protocols > BGP and click the corresponding tenant and private network.
Click various options, such as Neighbors, Interfaces, Routes, and Traffic to check different statistics related to BGP.

Figure 6-20 Validating Statistics