Ethernet MAC Address (7.2)
Ethernet technology relies on MAC addresses to function. MAC addresses are used to identify the frame source and destination.
MAC Address and Hexadecimal (7.2.1)
As discussed in detail in Chapter 5, “Number Systems,” in networking, IPv4 addresses are represented using the decimal (base 10) number system and the binary (base 2) number system. IPv6 addresses and Ethernet addresses are represented using the hexadecimal (base 16) number system. To understand hexadecimal, you must first be very familiar with binary and decimal.
The hexadecimal numbering system uses the numbers 0 to 9 and the letters A to F.
An Ethernet MAC address consists of a 48-bit binary value. Hexadecimal is used to identify an Ethernet address because a single hexadecimal digit represents 4 binary bits. Therefore, a 48-bit Ethernet MAC address can be expressed using only 12 hexadecimal values.
Figure 7-5 compares the equivalent decimal and hexadecimal values for binary 0000 to 1111.
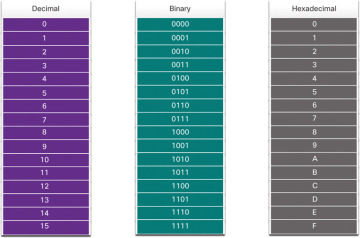
Figure 7-5 Decimal to Binary to Hexadecimal Conversion
Given that 8 bits (1 byte) is a common binary grouping, binary 00000000 to 11111111 can be represented in hexadecimal as the range 00 to FF, as shown in the Figure 7-6.
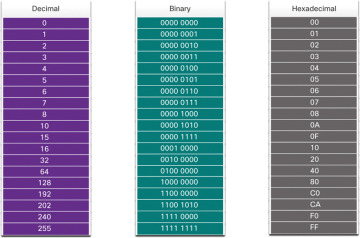
Figure 7-6 Selected Examples of Decimal to Binary to Hexadecimal Conversions
When using hexadecimal, leading zeros are always displayed to complete the 8-bit representation. For example, in Figure 7-6, the binary value 0000 1010 is shown to be 0A in hexadecimal.
Hexadecimal numbers are often represented by a value preceded by 0x (for example, 0x73) to distinguish between decimal and hexadecimal values in documentation.
Hexadecimal may also be represented using a subscript 16 or by using the hex number followed by an H (for example, 73H).
You might have to convert between decimal and hexadecimal values. If such conversions are required, convert the decimal or hexadecimal value to binary and then to convert the binary value to either decimal or hexadecimal as appropriate. See Chapter 5 for more information.
Ethernet MAC Address (7.2.2)
In an Ethernet LAN, every network device is connected to the same shared medium. The MAC address is used to identify the physical source and destination devices (NICs) on the local network segment. MAC addressing provides a method for device identification at the data link layer of the OSI model.
An Ethernet MAC address is a 48-bit address expressed using 12 hexadecimal digits, as shown in Figure 7-7. Because 1 byte equals 8 bits, we can also say that a MAC address is 6 bytes in length.

Figure 7-7 Ethernet MAC Address in Bits, Hextets, and Bytes
All MAC addresses must be unique to the Ethernet device or Ethernet interface. To ensure uniqueness, every vendor that sells Ethernet devices must register with the IEEE to obtain a unique 6-digit hexadecimal (that is, 24-bit or 3-byte) code called an organizationally unique identifier (OUI).
When a vendor assigns a MAC address to a device or to an Ethernet interface, the vendor must do as follows:
Use its assigned OUI as the first 6 hexadecimal digits.
Assign a unique value in the last 6 hexadecimal digits.
Therefore, an Ethernet MAC address consists of a 6-digit hexadecimal vendor OUI code followed by a 6-digit hexadecimal vendor-assigned value, as shown in Figure 7-8.

Figure 7-8 The Ethernet MAC Address Structure
For example, say that Cisco needs to assign a unique MAC address to a new device, and the IEEE has assigned Cisco the OUI 00-60-2F. Cisco would configure the device with a unique vendor code such as 3A-07-BC. Therefore, the Ethernet MAC address of that device would be 00-60-2F-3A-07-BC.
It is the responsibility of a vendor to ensure that no two of its devices are assigned the same MAC address. However, it is possible for duplicate MAC addresses to exist because of mistakes made during manufacturing, mistakes made in some virtual machine implementation methods, or modifications made using one of several software tools. In such a case, it is necessary to modify the MAC address with a new NIC or make modifications by using software.
Frame Processing (7.2.3)
Sometimes a MAC address is referred to as a burned-in address (BIA) because the address is hard coded into read-only memory (ROM) on the NIC. This means that the address is permanently encoded into the ROM chip.
When the computer boots up, the NIC copies its MAC address from ROM into RAM. When a device is forwarding a message to an Ethernet network, as shown in Figure 7-9, the Ethernet header includes the following:
Source MAC address: This is the MAC address of the source device NIC.
Destination MAC address: This is the MAC address of the destination device NIC.
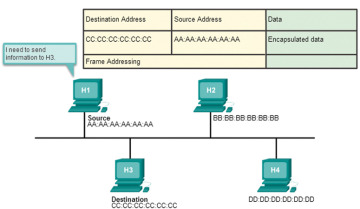
Figure 7-9 The Source Prepares a Frame to Send to the Destination
When a NIC receives an Ethernet frame, it examines the destination MAC address to see if it matches the physical MAC address that is stored in RAM. If there is no match, the device discards the frame. In Figure 7-10, H2 and H4 discard the frame. The MAC address matches for H4, so H4 passes the frame up the OSI layers, where the de-encapsulation process takes place.
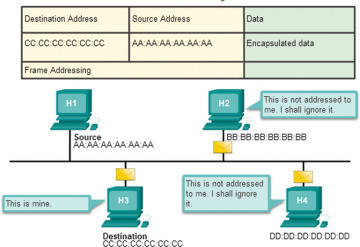
Figure 7-10 All Devices Receive the Frame, but Only the Destination Processes It
Any device that is the source or destination of an Ethernet frame will have an Ethernet NIC and, therefore, a MAC address. This includes workstations, servers, printers, mobile devices, and routers.
Unicast MAC Address (7.2.4)
In Ethernet, different MAC addresses are used for Layer 2 unicast, broadcast, and multicast communications.
A unicast MAC address is a unique address that is used when a frame is sent from a single transmitting device to a single destination device.
In Figure 7-11, the destination MAC address and the destination IP address are both unicast.
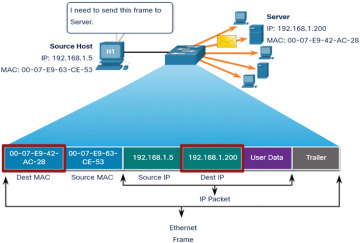
Figure 7-11 Unicast Frame Transmission
A host with IPv4 address 192.168.1.5 (source) requests a web page from the server at IPv4 unicast address 192.168.1.200. For a unicast packet to be sent and received, a destination IP address must be in the IP packet header. A corresponding destination MAC address must also be present in the Ethernet frame header. The IP address and MAC address combine to deliver data to one specific destination host.
The process that a source host uses to determine the destination MAC address associated with an IPv4 address is known as Address Resolution Protocol (ARP). The process that a source host uses to determine the destination MAC address associated with an IPv6 address is known as Neighbor Discovery (ND).
Broadcast MAC Address (7.2.5)
An Ethernet broadcast frame is received and processed by every device on an Ethernet LAN. The features of an Ethernet broadcast are as follows:
It has the destination MAC address FF-FF-FF-FF-FF-FF in hexadecimal (or 48 1s in binary).
It is flooded out all Ethernet switch ports except the incoming port.
It is not forwarded by a router.
If the encapsulated data is an IPv4 broadcast packet, this means the packet contains a destination IPv4 address that has all 1s in the host portion. This numbering in the address means that all hosts on that local network (broadcast domain) receive and process the packet.
In Figure 7-12, the destination MAC address and destination IP address are both broadcast addresses.
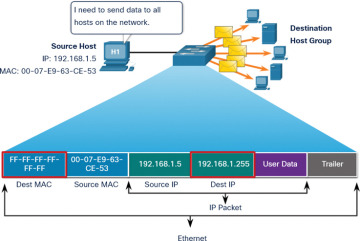
Figure 7-12 Broadcast Frame Transmission
The source host sends an IPv4 broadcast packet to all devices on its network. The IPv4 destination address is a broadcast address, 192.168.1.255. When the IPv4 broadcast packet is encapsulated in the Ethernet frame, the destination MAC address is the broadcast MAC address FF-FF-FF-FF-FF-FF in hexadecimal (or 48 1s in binary).
DHCP for IPv4 is an example of a protocol that uses Ethernet and IPv4 broadcast addresses. However, not all Ethernet broadcasts carry IPv4 broadcast packets. For example, ARP requests do not use IPv4, but the ARP message is sent as an Ethernet broadcast.
Multicast MAC Address (7.2.6)
An Ethernet multicast frame is received and processed by a group of devices on the Ethernet LAN that belong to the same multicast group. The features of an Ethernet multicast frame are as follows:
It has destination MAC address 01-00-5E when the encapsulated data is an IPv4 multicast packet and destination MAC address 33-33 when the encapsulated data is an IPv6 multicast packet.
There are other reserved multicast destination MAC addresses for when the encapsulated data is not IP, such as Spanning Tree Protocol (STP) and Link Layer Discovery Protocol (LLDP).
It is flooded out all Ethernet switch ports except the incoming port, unless the switch is configured for multicast snooping.
It is not forwarded by a router unless the router is configured to route multicast packets.
If the encapsulated data is an IP multicast packet, the devices that belong to a multicast group are assigned a multicast group IP address. The range of IPv4 multicast addresses is 224.0.0.0 to 239.257.257.257. The range of IPv6 multicast addresses begins with ff00::/8. Because a multicast address represents a group of addresses (sometimes called a host group), it can only be used as the destination of a packet. The source is always a unicast address.
As with the unicast and broadcast addresses, a multicast IP address requires a corresponding multicast MAC address to deliver frames on a local network. The multicast MAC address is associated with, and uses addressing information from, the IPv4 or IPv6 multicast address.
In Figure 7-13, the destination MAC address and destination IP address are both multicast addresses.
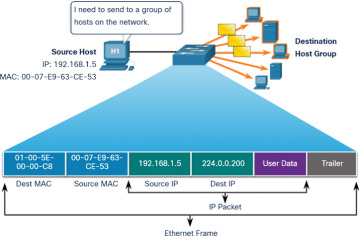
Figure 7-13 Multicast Frame Transmission
Routing protocols and other network protocols use multicast addressing. Applications such as video and imaging software may also use multicast addressing, although multicast applications are not as common.