Network Communication Models (5.3)
Network communication models help you understand the various components and protocols used in network communications. These models help you see the function of each protocol and their relationship to other protocols.

Video—Network Protocols (5.3.1)
Refer to the online course to view this video.

Video—The Protocol Stack (5.3.2)
Refer to the online course to view this video.
The Protocol Stack (5.3.3)
Successful communication between hosts requires interaction between many protocols. These protocols are implemented in software and hardware that are installed on each host and networking device.
The interaction between the different protocols on a device can be illustrated as a protocol stack, as shown in Figure 5-6. A stack illustrates the protocols as a layered hierarchy, with each higher-level protocol depending on the services of the protocols shown in the lower levels.
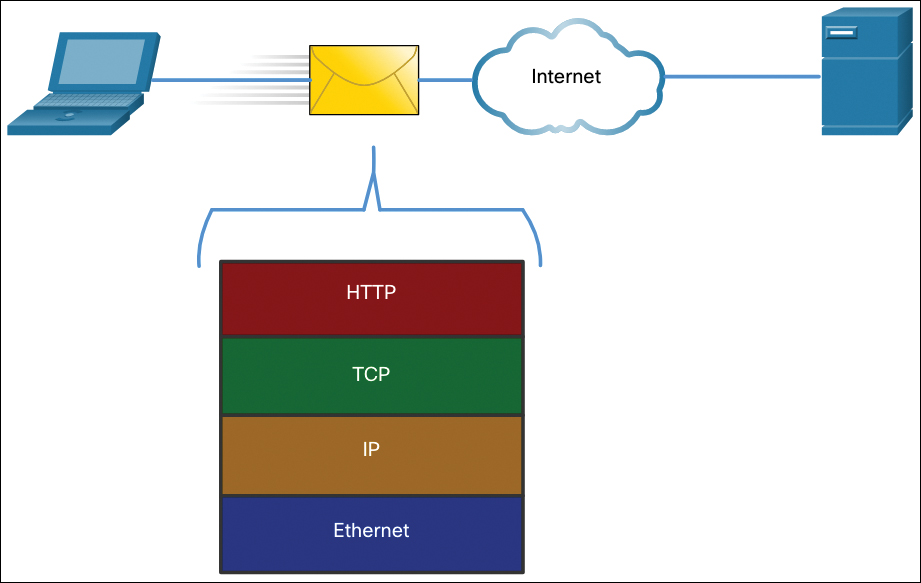
Figure 5-6 A Protocol Stack for Internet Communications
The separation of functions enables each layer in the stack to operate independently of others. For example, you can use your laptop computer connected to a cable modem at home to access your favorite website, or you can view the same website on your laptop using a wireless connection at the library. The function of the web browser is not affected by the change in the physical location or the method of connectivity.
The protocols in Figure 5-6 are described as follows:
Hypertext Transfer Protocol (HTTP)—This protocol governs the way a web server and a web client interact. HTTP defines the content and formatting of the requests and responses that are exchanged between the client and server. Both the client and the web server software implement HTTP as part of the application. HTTP relies on other protocols to govern how the messages are transported between the client and server.
Transmission Control Protocol (TCP)—This protocol manages the individual conversations. TCP is responsible for guaranteeing the reliable delivery of the information and managing flow control between the end devices.
Internet Protocol (IP)—This protocol is responsible for delivering messages from the sender to the receiver. IP is used by routers to forward the messages across multiple networks.
Ethernet—This protocol is responsible for the delivery of messages from one NIC to another NIC on the same Ethernet local-area network (LAN).
The TCP/IP Model (5.3.4)
Layered models help you visualize how the various protocols work together to enable network communications. A layered model depicts the operation of the protocols occurring within each layer, as well as the interaction with the layers above and below it. The layered model has many benefits:
Assists in protocol design, because protocols that operate at a specific layer have defined information that they act upon and a defined interface to the layers above and below
Fosters competition because products from different vendors can work together
Enables technology changes to occur at one level without affecting the other levels
Provides a common language to describe networking functions and capabilities
The first layered model for internetwork communications was created in the early 1970s and is referred to as the Internet model. It defines four categories of functions that must occur in order for communications to be successful. The suite of TCP/IP protocols that are used for Internet communications follows the structure of this model, as shown in Table 5-2. Because of this, the Internet model is commonly referred to as the TCP/IP model.
Table 5-2 The Layers of the TCP/IP Model
TCP/IP Model Layer |
Description |
|---|---|
Application |
Represents data to the user, plus encoding and dialogue control |
Transport |
Supports communication between various devices across diverse networks |
Internet |
Determines the best path through the network |
Network Access |
Controls the hardware devices and media that make up the network |
The OSI Reference Model (5.3.5)
Two basic types of models are used to describe the functions that must occur in order for network communications to be successful: protocol models and reference models.
Protocol model—This model closely matches the structure of a particular protocol suite. A protocol suite includes the set of related protocols that typically provide all the functionality required for people to communicate with the data network. The TCP/IP model is a protocol model because it describes the functions that occur at each layer of protocols within the TCP/IP suite.
Reference model—This type of model describes the functions that must be completed at a particular layer but does not specify exactly how a function should be accomplished. A reference model is not intended to provide a sufficient level of detail to define precisely how each protocol should work at each layer. The primary purpose of a reference model is to aid in clearer understanding of the functions and processes necessary for network communications.
The most widely known internetwork reference model was created by the Open Systems Interconnection (OSI) project at the International Organization for Standardization (ISO). It is used for data network design, operation specifications, and troubleshooting. This model is commonly referred to as the OSI model. The OSI layers are described in Table 5-3.
Table 5-3 The Layers of the OSI Model
OSI Model Layer |
Description |
|---|---|
7–Application |
The application layer contains protocols used for process-to-process communications. |
6–Presentation |
The presentation layer provides for common representation of the data transferred between application layer services. |
5–Session |
The session layer provides services to the presentation layer to organize its dialogue and to manage data exchange. |
4–Transport |
The transport layer defines services to segment, transfer, and reassemble the data for individual communications between the end devices. |
3–Network |
The network layer provides services to exchange the individual pieces of data over the network between identified end devices. |
2–Data Link |
The data link layer protocols describe methods for exchanging data frames between devices over a common media. |
1–Physical |
The physical layer protocols describe the mechanical, electrical, functional, and procedural means to activate, maintain, and de-activate physical connections for bit transmission to and from a network device. |
Upper and Lower Layers of the OSI Model (5.3.6)
You can visualize how data moves across a network by using the seven layers of the OSI model, as shown in Table 5-3. The OSI model breaks down network communication into multiple processes, as shown in Table 5-4. Each process is a small part of the larger task.
Table 5-4 Common Components of the Layers of the OSI Model
Group |
Layer Number |
Layer Name |
Common Network Components Associated with This Layer |
|---|---|---|---|
Upper Layers |
7 |
Application |
|
6 |
Presentation |
|
|
5 |
Session |
|
|
Lower Layers |
4 |
Transport |
|
3 |
Network |
|
|
2 |
Data Link |
|
|
1 |
Physical |
|
For example, in a vehicle manufacturing plant, the entire vehicle is not assembled by one person. Rather, the vehicle moves from station to station where specialized teams add specific components. The complex task of assembling a vehicle is made easier by breaking it into manageable and logical tasks. This process also makes troubleshooting easier. When a problem occurs in the manufacturing process, it is possible to isolate the problem to the specific task where the defect was introduced and then fix that problem.
In a similar manner, the OSI model helps you troubleshoot by focusing on a specific layer to identify and resolve network problems. Networking teams often refer to different functions occurring on a network by the number of the OSI model layer that specifies that functionality. For example, the process of encoding the data bits for transmission across the media occurs at Layer 1, the physical layer. The formatting of data so it can be interpreted by the network connection in your laptop or phone is described at Layer 2, the data link layer.
OSI Model and TCP/IP Model Comparison (5.3.7)
Because TCP/IP is the protocol suite in use for Internet communications, why do you need to learn the OSI model as well? The TCP/IP model is a method of visualizing the interactions of the various protocols that make up the TCP/IP protocol suite. It does not describe general functions that are necessary for all networking communications. It describes the networking functions specific to those protocols in use in the TCP/IP protocol suite. For example, at the network access layer, the TCP/IP protocol suite does not specify which protocols to use when transmitting over a physical medium, nor the method of encoding the signals for transmission. OSI Layers 1 and 2 discuss the necessary procedures to access the media and the physical means to send data over a network.
The protocols that make up the TCP/IP protocol suite can be described in terms of the OSI reference model. The functions that occur at the Internet layer in the TCP/IP model are contained in the network layer of the OSI model, as shown in Figure 5-7. The transport layer functionality is the same between both models. However, the network access layer and the application layer of the TCP/IP model are further divided in the OSI model to describe discrete functions that must occur at these layers.
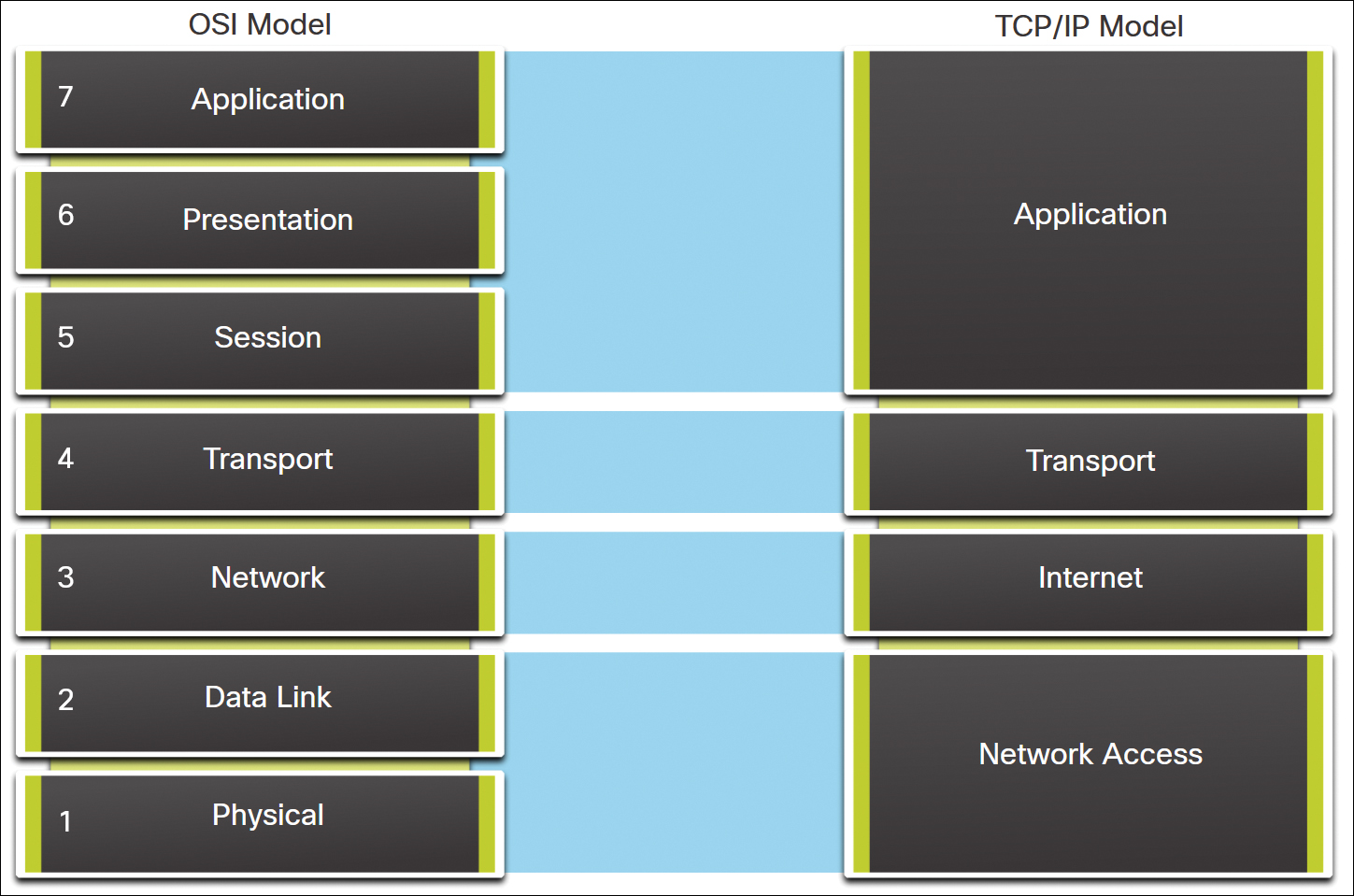
Figure 5-7 The OSI and TCP/IP Models
The key similarities are in the transport and network layers; however, the two models differ in how they relate to the layers above and below each layer:
OSI Layer 3, the network layer, maps directly to the TCP/IP Internet layer. This layer is used to describe protocols that address and route messages through an internetwork.
OSI Layer 4, the transport layer, maps directly to the TCP/IP transport layer. This layer describes general services and functions that provide ordered and reliable delivery of data between source and destination hosts.
The TCP/IP application layer includes several protocols that provide specific functionality to a variety of end-user applications. The OSI model Layers 5, 6, and 7 are used as references for application software developers and vendors to produce applications that operate on networks.
Both the TCP/IP and OSI models are commonly used when referring to protocols at various layers. Because the OSI model separates the data link layer from the physical layer, it is commonly used when referring to these lower layers.