Configuration of the Routed Interface
In threat defense, you can configure a data interface with a static IP address. A threat defense can also operate as a DHCP client and obtain an IP address from a DHCP server. Furthermore, you can enable the DHCP service on a threat defense and configure it to assign IP addresses dynamically to its hosts.
Configuring Interfaces with Static IP Addresses
To configure a routed interface with a static IP address, follow these steps:
Step 1. Navigate to Devices > Device Management. A list of the managed devices appears.
Step 2. Click the pencil icon that is next to the threat defense name you want to configure. The device management editor page appears, showing all the interfaces of threat defense on the Interfaces tab (see Figure 4-4).
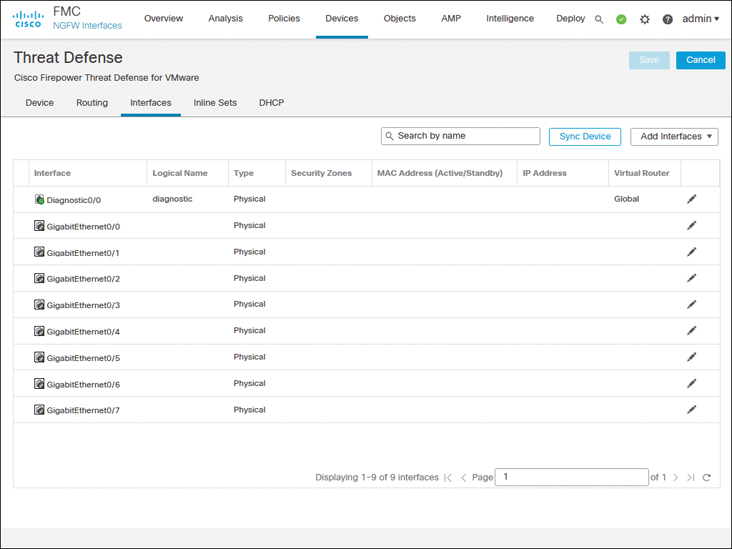
FIGURE 4-4 Interfaces Tab of the Virtual Threat Device
Depending on the threat defense platform you run, you may come across different types of interfaces and model-specific options. For example, threat defense model 1010 comes with an Ethernet type interface with built-in switch ports, as shown in Figure 4-5. To configure this model in routed mode, you need to disable access mode switch ports.
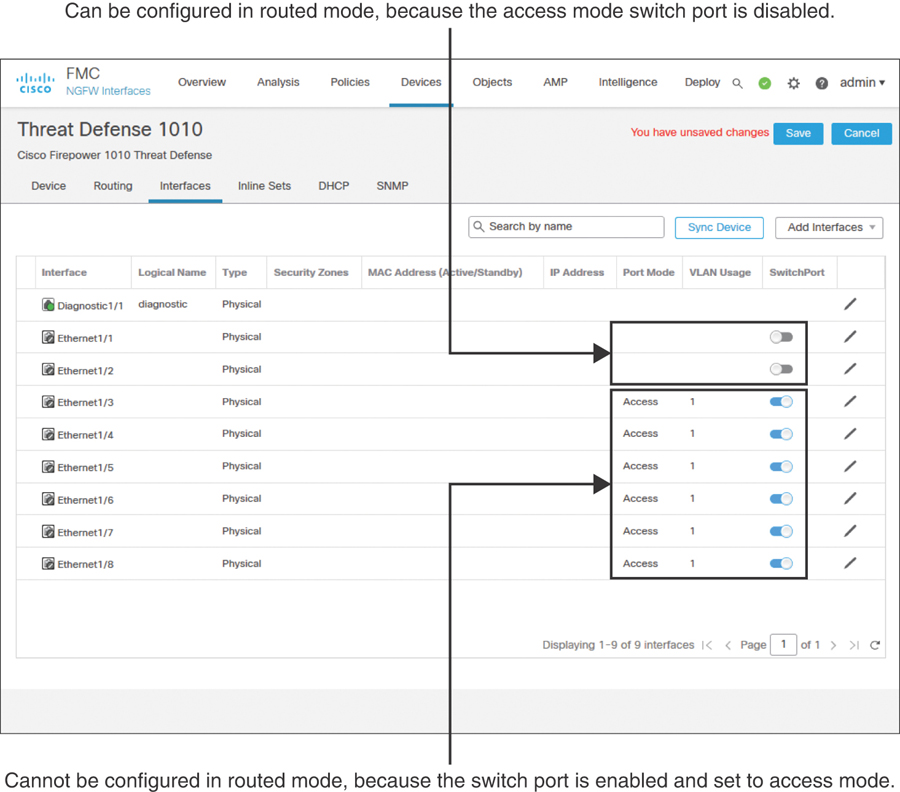
FIGURE 4-5 Interfaces Tab of Threat Defense Model 1010 Shows Switch Port Modes
Step 3. On the Interfaces tab, click the pencil icons next to GigabitEthernet0/0 and GigabitEthernet0/1 to configure these interfaces for the inside and outside networks, respectively. Use the settings shown in Table 4-2 to configure these two interfaces.
Table 4-2 Settings for Ingress and Egress Interfaces
GigabitEthernet0/0
GigabitEthernet0/1
Interface name
INSIDE_INTERFACE
OUTSIDE_INTERFACE
Security zone (optional)
INSIDE_ZONE
OUTSIDE_ZONE
IP address
192.168.1.1/24
172.16.1.1/24
To enable an interface, you must give it a name; this is a requirement. However, configuring a security zone is an optional step. Here, in the Edit Physical Interface window, you can create a security zone and associate it with an interface on the fly. In future, you could use the Objects > Object Management > Interface page to manage the security zones.
Figure 4-6 shows the general settings for GigabitEthernet0/0; for example, it is named INSIDE_INTERFACE. Make sure to enable an interface using the Enabled check box.
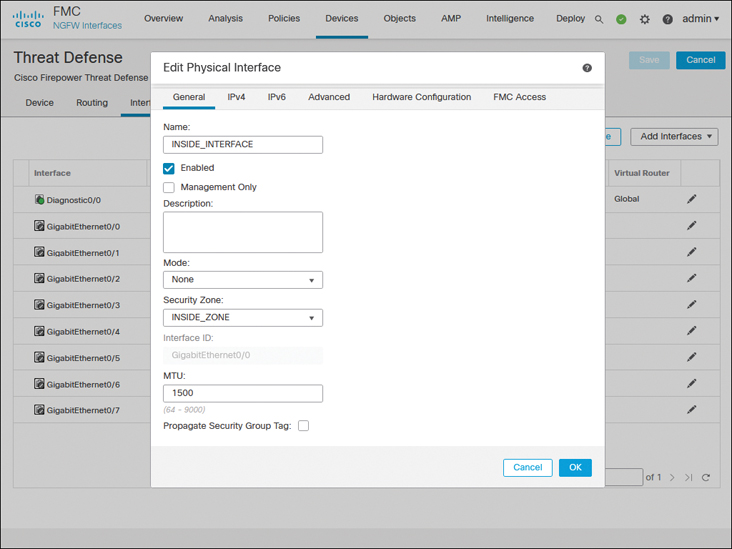
FIGURE 4-6 General Configurations of the Inside Interface
Figure 4-7 shows the manual assignment of a static IP address to the GigabitEthernet0/0 interface.
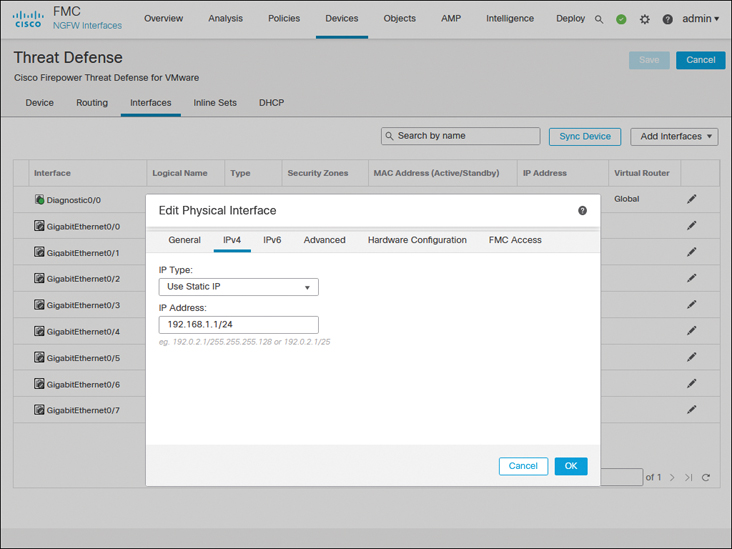
FIGURE 4-7 Static IP Address on the Inside Interface GigabitEthernet0/0
Step 4. Repeat the preceding steps for GigabitEthernet0/1 to enable it for the outside network. When you’re finished, click the Save button to save the changes.
Figure 4-8 shows the configurations of ingress and egress routed interfaces.
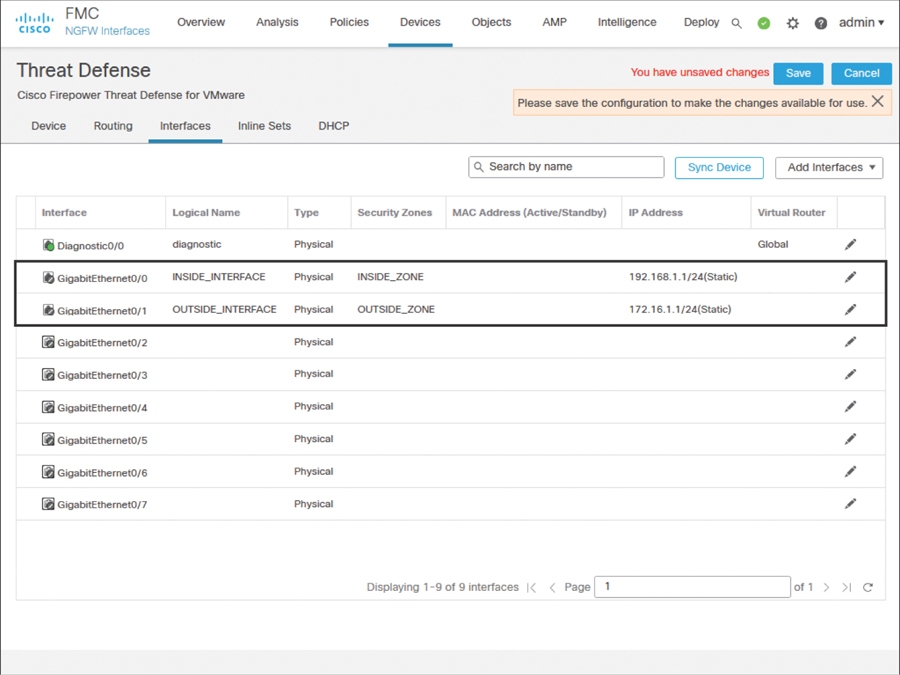
FIGURE 4-8 Inside and Outside Interface Configurations
Step 5. After the configuration is saved, navigate to Deploy > Deployment. Select the threat defense where you want to apply the changes and click the Deploy button to apply the configurations (see Figure 4-9).

FIGURE 4-9 Threat Defense Configuration Deployment
Configuring Interfaces with Automatic IP Addresses
A threat defense can function as a DHCP client as well as a DHCP server. For example, if you deploy a threat defense between the outside interface and an Internet service provider (ISP), the device can obtain an IP address dynamically for its outside interface from the ISP router. Simultaneously, a threat defense can act as a DHCP server and provide IPv4 addresses dynamically to the hosts it inspects through its inside interface. Configuring a threat defense as a DHCP server is an optional choice; it does not influence the deep packet inspection capability.
Figure 4-10 illustrates two scenarios: The inside network obtains an IP address from the DHCP service running on a threat defense, while the outside interface of the threat defense gets an IP address from a service provider.
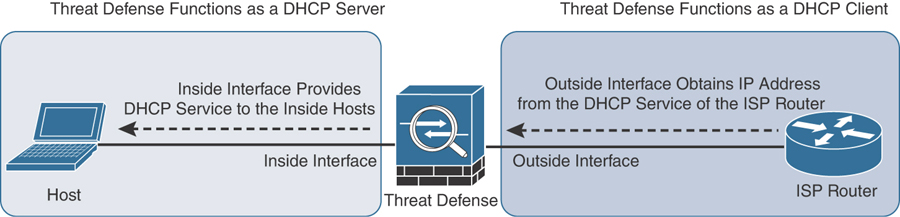
FIGURE 4-10 A Threat Defense as a DHCP Server and a DHCP Client
Enabling an interface to obtain an IP address from a DHCP server is a straightforward process. For example, during the outside interface configuration, when you assign a static IP address to the interface, you simply select Use DHCP from the drop-down instead of selecting the Use Static IP option. That’s it. When this interface configuration is deployed, the outside interface attempts to obtain the IP address from an external DHCP server or the ISP router. See Figure 4-11 to find the Use DHCP option.
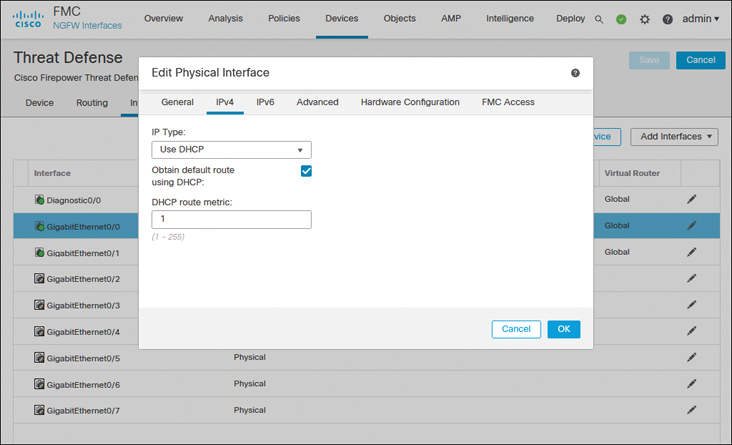
FIGURE 4-11 Interface Configuration to Run a Threat Defense as a DHCP Client
However, if you want the threat defense to provide IP addresses dynamically to its connected hosts, you need to enable DHCP services on it. The following steps describe how to configure a threat defense with DHCP services and allow its inside interface to provide IP addresses to its connected host computers:
Step 1. Go to Devices > Device Management and click the pencil icon to edit the threat defense configuration.
Step 2. Assign the static IP address 192.168.1.1 on GigabitEthernet0/0—the inside interface of the threat defense. Your end users (DHCP clients) will be using this IP address as their default gateway. (Figure 4-10 illustrates the purpose of the inside interface.)
Step 3. On the device editor page, go to the DHCP tab. By default, the DHCP Server page appears.
Step 4. Click the Add button on the Server tab (located near the bottom part of the DHCP Server page). The Add Server window appears.
Step 5. In the Add Server window, select the inside interface from the drop-down list because it will be offering IP addresses to the inside network.
Step 6. Create an address pool for the DHCP server. Remember that the addresses in the pool must be within the same subnet as the connected interface. For example, if you assign 192.168.1.1/24 to the inside interface, the DHCP address pool should be between 192.168.1.2 and 192.168.1.254.
Figure 4-12 shows that a DHCP server is enabled on the threat defense’s inside interface with the address pool 192.168.1.2 to 192.168.1.10.
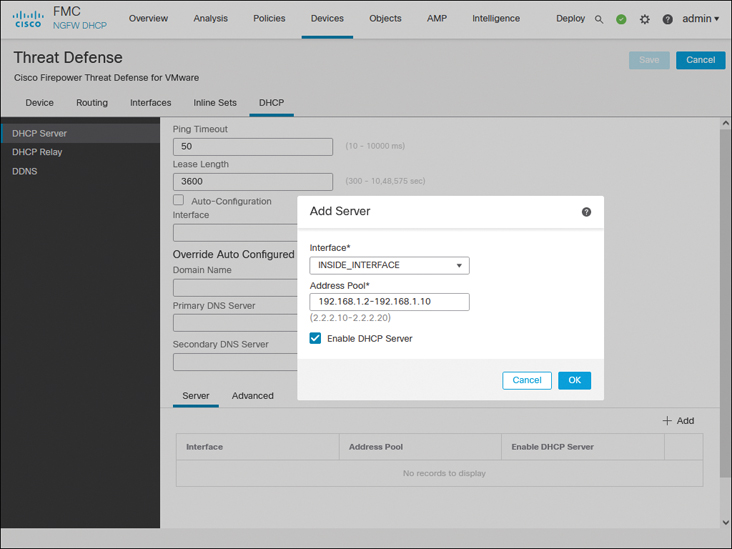
FIGURE 4-12 DHCP Server Configurations on a Threat Defense
Step 7. Select the Enable DHCP Server check box to enable the service and click OK. You return to the device editor page.
Step 8. Optionally, through the DHCP service, a threat defense can transfer any DNS-related information to your DHCP clients. The DHCP Server page allows you to enter domain names and DNS addresses manually. Alternatively, you can select the Auto-Configuration check box to let the threat defense obtain any DNS information automatically from a DHCP client connected to a predefined interface.
Step 9. Click the Save button to save the configurations. To deploy the configurations to your threat defense, go to Deploy > Deployment, select the threat defense you wish to configure, and click the Deploy button (shown previously in Figure 4-9).