Cisco Intersight Kubernetes Service
Cisco Intersight Kubernetes Service (IKS) effectively expands CCP’s functionality to benefit from Intersight’s native infrastructure management capabilities, further simplifying building and managing Kubernetes environments. IKS is a SaaS offering, taking away the hassle of installing, hosting, and managing a container management solution. For organizations with specific requirements, it also offers two additional deployment options (with a virtual appliance). So, let’s take a look at how IKS can make our lives easier. Figure 5-12 provides an overview of Intersight Cloud management.

Figure 5-12 Intersight Cloud management
Benefits of IKS
The following are the benefits of using IKS:
Simplify Kubernetes Day 0 to Day N operations and increase application agility with a turnkey SaaS platform that makes it easy to deploy and manage clusters across data centers, the edge, and public clouds.
Reduce risk, lower cost, improve governance, and take multicloud control on a security-hardened platform, with enhanced availability, native integrations with AWS, Azure, and Google Cloud, and end-to-end industry-leading Cisco TAC support.
Get more value from your investments with a flexible, extensible Kubernetes platform that supports multiple delivery options, hypervisors, storage, and bare-metal configurations.
Automate and simplify with self-service built-in add-ons and optimizations such as AI/ML frameworks, service mesh, networking, monitoring, logging, and persistent object storage.
Common Use Case
A good example comes from the retail sector: an IT admin needs to quickly create and configure hundreds of edge locations for the company’s retail branches to perform AI/ML processing and a few core ones in privately owned or co-located data centers. The reason it makes sense for processing or storing large chunks of data at the edge is the cost of shipping the data back to the core DC or to a public cloud (and latency to a certain extent).
Creating those Kubernetes clusters would require firmware upgrades as well as OS and hypervisor installations before the IT admin can even get to the container layer. With Cisco Intersight providing a comprehensive, common orchestration and management layer—from server and fabric management to hyperconverged infrastructure management to Kubernetes—creating a container environment from scratch can be literally done with just a few clicks. Figure 5-13 illustrates a high-level architecture of IKS.
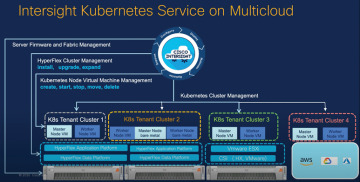
Figure 5-13 Architecture of IKS
IT admins can use either the IKS GUI or its APIs, or they can integrate with an Infrastructure as Code plan (such as HashiCorp’s Terraform) to quickly deploy a Kubernetes environment on a variety of platforms—VMware ESXi hypervisors or Cisco HyperFlex—thus enabling significant savings and efficiency without the need of virtualization.
Deploying Consistent, Production-Grade Kubernetes Anywhere
Few open source projects have been as widely and rapidly adopted as Kubernetes (K8s), the de facto container orchestration platform. With Kubernetes, development teams can deploy, manage, and scale their containerized applications with ease, making innovations more accessible to their continuous delivery pipelines. However, Kubernetes comes with operational challenges, because it requires time and technical expertise to install and configure. Multiple open source packages need to be combined on top of a heterogeneous infrastructure, across on-premises data centers, edge locations, and, of course, public clouds. Installing Kubernetes and the different software components required, creating clusters, configuring storage, networking, and security, optimizing for AI/ML, and other manual tasks can slow down the pace of development and can result in teams spending hours debugging. In addition, maintaining all these moving parts (for example, upgrading, updating, and patching critical security bugs) requires ongoing significant human capital investment.
The solution? Cisco Intersight Kubernetes Service (IKS), a turnkey SaaS solution for managing consistent, production-grade Kubernetes anywhere.
How It Works
Cisco Intersight Kubernetes Service (IKS) is a fully curated, lightweight container management platform for delivering multicloud, production-grade, upstream Kubernetes. Part of the modular SaaS Cisco Intersight offerings (with an air-gapped on-premises option also available), IKS simplifies the process of provisioning, securing, scaling, and managing virtualized or bare-metal Kubernetes clusters by providing end-to-end automation, including the integration of networking, load balancers, native dashboards, and storage provider interfaces. It also works with all the popular public cloud–managed K8s offerings, integrating with common identity access with AWS Elastic Kubernetes Service (EKS), Azure Kubernetes Service (AKS) and Google Cloud Google Kubernetes Engine (GKE). IKS is ideal for AI/ML development and data scientists looking for delivering GPU-enabled clusters, and Kubeflow support with a few clicks. It also offers enhanced availability features, such as multimaster (tenant) and self-healing (operator model).
IKS is easy to install in minutes and can be deployed on top of VMware ESXi hypervisors, Cisco HyperFlex Application Platform (HXAP) hypervisors, and/or directly on Cisco HyperFlex Application Platform bare-metal servers, enabling significant savings and efficiency without the need of virtualization. In addition, with HXAP leveraging container-native virtualization capabilities, you can run virtual machines (VMs), VM-based containers, and bare-metal containers on the same platform! Cisco Intersight also offers native integrations with Cisco HyperFlex (HX) for enterprise-class storage capabilities (for example, persistent volume claims and public cloud-like object storage) and Cisco Application Centric Infrastructure (Cisco ACI) for networking, in addition to the industry- standard Container Storage Interface and Container Network Interface (for example, Calico).
Intersight Kubernetes Service integrates seamlessly with the other Cisco Intersight SaaS offerings to deliver a powerful, comprehensive cloud operations platform to easily and quickly deploy, optimize, and lifecycle-manage end-to-end infrastructure, workloads, and applications. Figure 5-14 illustrates the benefits of IKS.
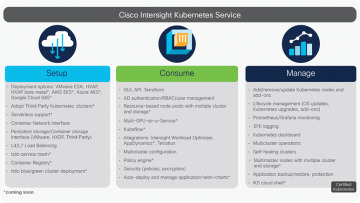
Figure 5-14 Benefits of IKS
IKS Release Model
IKS software follows a continuous-delivery release model that delivers features and maintenance releases. This approach enables Cisco to introduce stable and feature-rich software releases in a reliable and frequent manner that aligns with Kubernetes supported releases.
Intersight Kubernetes Service Release and Support Model:
The IKS team supports releases from N-1 versions of Kubernetes. The team will not fully support/make available IKS versions older than N-1.
IKS follows a fix-forward model that requires release upgrades to fix issues. Release patches are not necessary with this model.
Tenant images are versioned according to which version of Kubernetes they contain.
Deploy Kubernetes from Intersight
The Intersight policies allow simplified deployments, as they abstract the configuration into reusable templates. The following sections outline the steps involved in deploying Kubernetes from Intersight.
Step 1: Configure Policies
All policies are created under the Configure > Polices & Configure > Pools section on Intersight. You can see the path of the policy at the top of each of the following figures.
The IP Pool will be used for IP addresses on your Control and Worker nodes virtual machines, when launched on the ESXi host. Figure 5-15 illustrates the IPv4 Pool details for policy configuration.
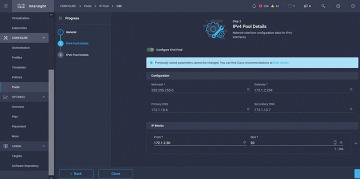
Figure 5-15 IPv4 Pool details for policy configuration
The Pod and Services Network CIDR is defined for internal networking within the Kubernetes cluster. Figure 5-16 illustrates the CIDR network to be used for the pods and services.
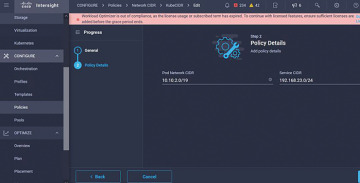
Figure 5-16 CIDR network to be used for the pods and services
The DNS and NTP configuration policy defines your NTP and DNS configuration (see Figure 5-17).
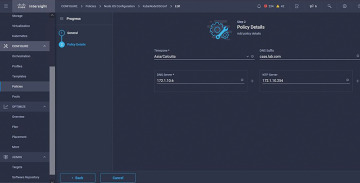
Figure 5-17 DNS and NTP configuration policy
You can define the proxy configuration policy for your Docker container runtime. Figure 5-18 illustrates this policy.
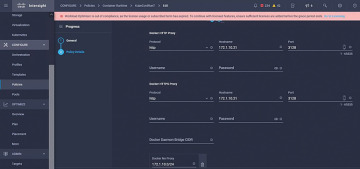
Figure 5-18 Policy for configuring a proxy for Docker
In the master and worker node VM policy, you define the configuration needed on the virtual machines deployed as Master and Worker nodes (see Figure 5-19).
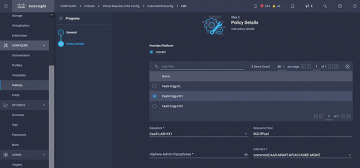
Figure 5-19 Master and worker node VM policy
Step 2: Configure Profile
Once we have created the preceding policies, you would then bind them into a profile that you can then deploy.
Deploying the configuration using policies and profiles abstracts the configuration layer so that it can be repeatedly deployed quickly.
You can copy this profile and create a new one with modifications on the underlying policies within minutes, to one or more Kubernetes clusters, in a fraction of the time needed for the manual process. Figure 5-20 illustrates the name and tag configuration in the profile.
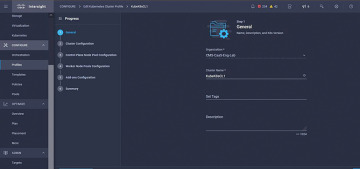
Figure 5-20 Name and tag configuration in the profile
Set the Pool, Node OS, and Network CIDR policies. You also need to configure a user ID and SSH key (public). Its corresponding private key would be used to ssh into the Master and Worker nodes. Figure 5-21 illustrates the created policies being referred to in the profile.
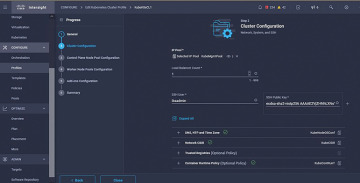
Figure 5-21 Created policies being referred to in the profile
Configure the control plane. You can define how many Master nodes you would need on the control plane. Figure 5-22 illustrates the K8s cluster configuration and number of Master nodes.
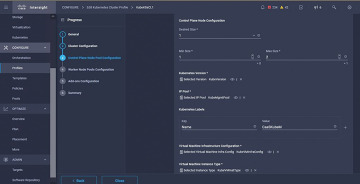
Figure 5-22 Cluster configuration and number of Master nodes
Configure the Worker nodes. Depending on the application requirements, you can scale up or scale down your Worker nodes. Figure 5-23 illustrates the K8s cluster configuration and number of Worker nodes.
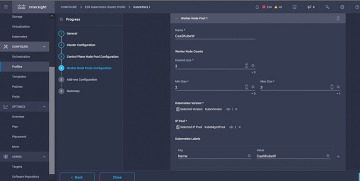
Figure 5-23 Cluster configuration and number of Worker nodes
Configure add-ons. As of now, you can automatically deploy Kubernetes Dashboard and Graffana with Prometheus monitoring. In the future, you can add more add-ons, which you can automatically deploy using IKS. Figure 5-24 illustrates the K8s cluster add-ons configuration.
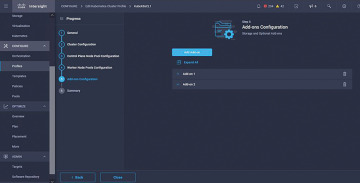
Figure 5-24 Cluster add-ons configuration
Check the Summary and click Deploy.
Figure 5-25 illustrates the K8s cluster Summary and Deployment screen.
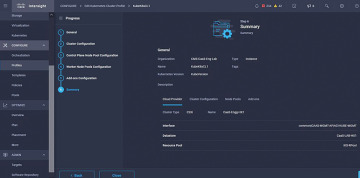
Figure 5-25 Cluster Summary and Deployment screen