The Cloud
When a business starts planning to leverage cloud in any form, there are three use cases that network designers should consider throughout the design process:
Securely extending a private network to a single or multiple public cloud environments: Includes multiple clouds (for example, multiple Amazon Web Services [AWS] and Azure), multiple regions in a cloud, or multiple VPCs in a cloud; VPN; multi-cloud and multi-VPC connectivity; scaling; and performance optimization of transit VPC. Also supports extending data centers into the cloud and enabling direct branch-to-cloud connectivity.
Optimizing data center and branch connectivity performance to cloud IaaS and SaaS: Includes best path to a destination, cloud segmentation, monitoring to assure the best performance, visibility into traffic going to applications, and traffic shaping/Quality of Service (QoS). Also supports extending data centers into the cloud and enabling direct branch-to-cloud connectivity.
Securing access to the Internet and SaaS from the branch: Includes connecting and protecting branch office users directly to the multi-cloud environment using Direct Internet Access (DIA) and properly securing them.
Cloud Connectivity Models
When businesses start to leverage cloud in any form, be it public, private, hybrid, or multi-cloud, how the business is going to connect to cloud environments is a topic for a network designer to address. There are multiple options, each with its own pros and cons.
Direct Cloud Access
Direct cloud access (DCA) allows a remote site to access SaaS applications directly from the Internet and through dedicated private connections. The cloud permits only the designated application traffic to use the directly connected Internet transport securely, while all other Internet-bound traffic takes the usual path, which could be through a regional hub, a data center, or a carrier-neutral facility (CNF). This feature allows the remote site to bypass the latency of tunneling Internet-bound traffic to a central site, subsequently improving the connectivity to the prioritized SaaS application; this feature is commonly referred to as Direct Internet Access (DIA). The edge router chooses the most optimal Internet path for access to these SaaS applications. Different applications could traverse different paths because the path selection is calculated on a per-application basis.
If any SaaS application path becomes unreachable or its performance score falls below an unacceptable level, the path is removed as a candidate path option. If all paths cannot be path candidates because of reachability or performance, then traffic to the SaaS application follows the normal, routed path. Figure 3-1 illustrates a remote site using DIA to access SaaS applications
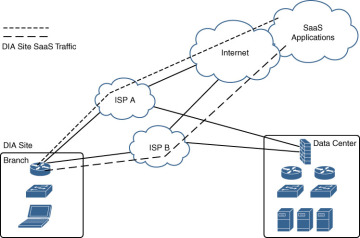
Figure 3-1 DCA/DCI Remote Site with DIA to Access SaaS Applications
Cloud Access Through a Gateway (Cloud Access Point)
Many businesses do not use DIA at the branch office, because either their sites are connected only by private providers (MPLS, VPLS, etc.) or centralized policy or security requirements do not permit it. They may use data centers, regional hubs, or even CNFs to enable Internet connectivity. In this case, SaaS traffic is tunneled to the best-performing gateway site, where it is subsequently routed to the Internet to reach the requested SaaS application service.
Figure 3-2 shows how cloud access can be achieved through a gateway in a data center or a cloud access point (CAP). A branch office tunnels SaaS traffic to a gateway location and then uses the Internet at the gateway location to access the SaaS application.
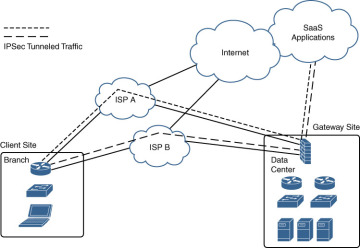
Figure 3-2 Cloud Access Through a Gateway
Hybrid Approach
It is possible to have a combination of DIA and client/gateway sites. When defining both DIA and gateway sites, SaaS applications can use either the DIA exits of the remote site or the gateway sites for any given application, depending on which path provides the best performance. DIA sites are, technically, a special case of a client site, but the Internet exits are local instead of remote.
Cloud Types
When selecting a cloud solution, there are a number of different types to choose from, each with its own associated benefits and limitations:
Private cloud: A private cloud consists of cloud computing resources used by one business. This cloud environment can be located within the business’s data center footprint, or it can be hosted by a cloud service provider (CSP). In a private cloud, the resources, applications, services, data, and infrastructure are always maintained on a private network and all devices are dedicated to the business.
Public cloud: A public cloud is the most common type of cloud computing. The cloud computing resources are owned and operated by a CSP. All infrastructure components are owned and maintained by the CSP. In a public cloud environment, a business shares the same hardware, storage, virtualization, and network devices with other businesses.
Hybrid cloud: A hybrid cloud is the use of both private and public clouds together to allow for a business to receive the benefits of both cloud environments while limiting their negative impacts on the business.
Multi-cloud: Multi-cloud is the use of two or more CSPs, with the ability to move workloads between the different cloud computing environments in real time as needed by the business.
Table 3-4 compares the different cloud types in relation to each other based on various characteristics.
Table 3-4 Cloud Types Detailed Comparison
Cloud Type |
Control |
Maintenance |
Flexibility |
Scalability |
Migration |
Cost |
Private cloud |
Most control |
High |
Least flexibility |
High scalability |
Hard migration |
High cost |
Public cloud |
Least control |
None |
Flexibility |
High scalability |
Hard migration |
Lowest cost |
Hybrid cloud |
Mix of both |
Medium |
Flexible |
Lowest scalability |
Ease of migration |
High cost |
Multi-cloud |
Least control |
No maintenance for each CSP, but across the CSPs is high |
Most flexibility |
Highest scalability |
Hardest migration |
Highest cost |
Cloud-Agnostic Architecture
A cloud-agnostic architecture is when there are no vendor specific features and functionality that are proprietary. It is focused on leveraging the same cloud capabilities across the different cloud providers no matter what vendor it is. When looking at cloud service providers and migrating applications to the cloud, there are three primary focus points that should be leveraged within a cloud-agnostic architecture:
Portability: Moving to the cloud inherently provides a level of portability, but if not carefully architected, applications and services can lose their portability as they get locked into specific CSP services. Portability here specifically allows mobility between different CSPs with a proper abstraction layer.
Abstraction: Leveraging an abstraction layer within the cloud architecture allows for a decoupling from the underlying cloud-specific platform functionality, which provides a direct cost reduction and an increase in flexibility. For example, using this abstraction layer to seamlessly invoke the same cloud capability between cloud provider one and cloud provider two, when there are different mechanisms and processes to do so. In addition, this same capability could be proprietary, but using this abstraction layer mitigates a potential hardcoded proprietary service call.
Interoperability: Developing applications and services with cloud interoperability as a key priority will not be tied to a specific cloud feature set. This allows for these applications and services to leverage different cloud platforms without major redevelopment or changes. This specifically allows for a cloud-agnostic approach.
To achieve a cloud-agnostic architecture, network designers should consider adopting the following practices.
Decoupling
There are two perspectives to think about for decoupling. First, all applications should be designed to be inherently decoupled from the underlying cloud platform they are on. This can be accomplished by leveraging service-oriented architecture (SOA), which is discussed in detail a bit later in this chapter. Second, all cloud components should be decoupled from the applications that leverage them.
Containerization
All applications should follow a containerized architecture. This is critical for cloud applications as well as on-premises data center applications. Ensuring all applications are developed with containerization in mind allows for real cloud adoption and portability. Container technology helps decouple applications from the cloud-specific environment, which provides an abstraction layer away from any of the CSP dependencies. The goal is to ensure that it is relatively easy to migrate applications between different cloud vendors if the mission requires it. Cloud containerized architectures is a topic that is covered in detail in an upcoming section.
Agnostic Versus Proprietary Cloud Services
Each cloud service provider is different and has unique services, with its own avenues to provision them to customers. There is a need to provide a mechanism to differentiate where these specific services interact with applications while also allowing for the standardization of agnostic services. Figure 3-3 shows how to delineate from an architecture perspective between cloud-agnostic services and cloud-proprietary services. This is how you should plan to migrate applications to a CSP.

Figure 3-3 Agnostic vs. Proprietary Cloud Services
Service-Oriented Architecture
To ensure a successful cloud-agnostic architecture, incorporating the software design service-oriented architecture (SOA) is hyper-critical. SOA is a style of software design where services are provided to other parts of an application component themselves. This is accomplished through network communication protocols. The underlying principles are vendor and technology agnostic. In SOA, services communicate with other services in two ways. The first way is to simply pass data between the different services. The second way is to logistically coordinate an activity event between two or more services. There are many benefits to SOA:
Code can be created so that it is reusable, which cuts down on time spent in the development process.
Developers can leverage multiple coding languages with SOA because it uses a central interface, which allows for flexibility and scalability within the software development cycle.
With SOA, a standard communication process is created that allows systems to function on their own and communicate effectively between them.
SOA is much more scalable, limiting client-server interaction, which allows for a direct increase in efficiency.
Cloud Containerized Architecture
Containerization is a large part of a cloud-agnostic architecture. Figure 3-4 shows the progression from a traditional on-premises deployment to a containerized cloud deployment.
Traditional Deployment Architecture
Traditionally, organizations and companies ran applications on physical servers. You could deploy multiple applications on the same physical server, but there was no way to properly restrict resources or set up controls to govern application guidelines. Because of these issues, there were a number of allocation and performance issues. Most of the time, each physical server was dedicated to a single application because of these limitations. This increased cost and resources and limited overall scalability.

Figure 3-4 Progression from Traditional to Containerized Deployment
Virtualization Deployment Architecture
Virtualization allows for multiple virtual machines (VMs) to be deployed on a single physical server. Each VM is isolated from other applications with its own resources and security controls allocated to it individually. Virtualization allows for better utilization of resources on a physical server and scales better because applications (VMs) can be added and removed as needed depending on the needed resources. Each VM runs all components that a physical server would run, such as the application and the operating system.
Container Deployment Architecture
Containers are similar to VMs but have less stringent isolation controls that allows them to share the operating system among other applications. Because of this, containers are lightweight. A container has its own file system, shares CPU time, memory, process space, and more. Because containers are decoupled from the underlying infrastructure, they are moveable between different fabrics as needed by the underlying business requirements.
Containers provide a number of benefits:
Agile application creation and deployment (CI/CD)
Separation of responsibilities between development and operational tasks
Real-time application-level health analytics
Standardization and consistency across all environments and enclaves
Real-time distribution with the capability to port into other operating systems and locations as required
Increased overall predictability of application performance and requirements
Increased resource efficiency
Cloud Application Strategy
As a business readies its business lines of efforts and their respective applications for migration to the cloud, it is highly recommended that the business incorporate an application assessment process. As part of this process an application assessment team should be created with the following roles and purposes:
Line of business owner: The business stakeholder for this application. They understand the application’s business role and impact. They also understand the implications of this application and can appropriate business resources and priorities to this effort.
Security specialist, compliance auditor: The security team member in charge of the security controls, compliance regulations, and auditing of code. These are all critical roles that will direct decisions and actions from a risk management perspective for this application.
Application owner, application developer: The software engineering member responsible for this application. Creates code, modifies current code, and drives associated technical requirements for the application.
Network engineer, network designer, network architect: Facilitates the network resources to properly service the application based on the different requirements from the line of business owner, security specialist, and application owner.
Each application will have different requirements as it’s being reviewed in this process. The team will need to properly identify what the application is dependent on and make appropriate decisions to ensure the application is ready for the migration to the cloud environment.
The application assessment team will document in an application binder (or run book) everything that is discovered, decided on, and implemented for this application. The application binder should include all requirements and where they originated from; all security controls and regulatory standards that this application must comply with; and where the application is in the migration process and what is needed for it to be successful.