LANs, WANs, and the Internet (1.2)
Many different components are required to allow a network to provide services and resources. These various components work together to ensure that resources are delivered in an efficient manner to those requiring the services.
Network Components (1.2.1)
Different network components are used within the network to provide services and resources. These various components work together to ensure that resources are delivered in an efficient manner to those requiring the services.
Overview of Network Components (1.2.1.1)
The path that a message takes from source to destination can be as simple as a single cable connecting one computer to another or as complex as a collection of networks that literally spans the globe. This network infrastructure provides the stable and reliable channel over which these communications occur.
The network infrastructure contains three categories of network components, as shown in Figures 1-4, 1-5, and 1-6.
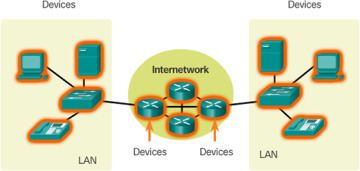
Figure 1-4 Devices
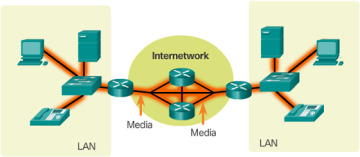
Figure 1-5 Media
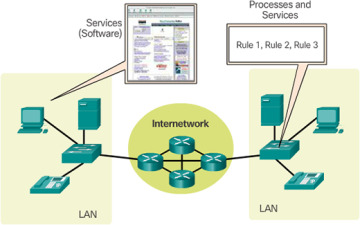
Figure 1-6 Services
Devices and media are the physical elements, or hardware, of the network. Hardware is often the visible components of the network platform such as a laptop, PC, switch, router, wireless access point, or the cabling used to connect the devices.
Services include many of the common network applications people use every day, like email hosting services and web hosting services. Processes provide the functionality that directs and moves the messages through the network. Processes are less obvious to us but are critical to the operation of networks.
End Devices (1.2.1.2)
The network devices that people are most familiar with are called end devices. Some examples of end devices are shown in Figure 1-7.
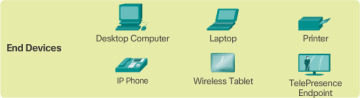
Figure 1-7 Examples of End Devices
An end device is either the source or destination of a message transmitted over the network. To distinguish one end device from another, each end device on a network is identified by an address. When an end device initiates communication, it uses the address of the destination end device to specify where the message should be sent. Devices between the source and destination are responsible for choosing the best path and forwarding messages sent between end devices, as shown in Figure 1-8.
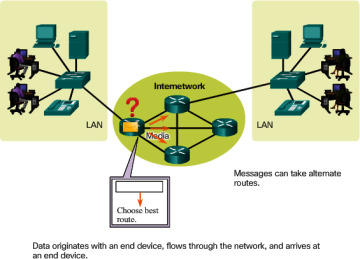
Figure 1-8 End Devices Communicate Across the Internetwork
Intermediary Network Devices (1.2.1.3)
Intermediary devices connect the individual end devices to the network and can connect multiple individual networks to form an internetwork. These intermediary devices provide connectivity and ensure that data flows across the network.
Intermediary devices use the destination end device address, in conjunction with information about the network interconnections, to determine the path that messages should take through the network, as shown in Figure 1-8.
Examples of the more common intermediary devices are shown in Figure 1-9.

Figure 1-9 Examples of Intermediary Devices
Intermediary network devices perform some or all of these functions:
Regenerate and retransmit data signals
Maintain information about what pathways exist through the network and internetwork
Notify other devices of errors and communication failures
Direct data along alternate pathways where there is a link failure
Classify and direct messages according to priorities
Permit or deny the flow of data, based on security settings
Network Media (1.2.1.4)
Communication across a network is carried on a medium. The medium provides the channel over which the message travels from source to destination.
Modern networks primarily use three types of media to interconnect devices and to provide the pathway over which data can be transmitted. As shown in Figure 1-10, these media are
Metallic wires within cables – data is encoded into electrical impulses
Glass or plastic fibers (fiber optic cable) – data is encoded as pulses of light
Wireless transmission – data is encoded using wavelengths from the electromagnetic spectrum
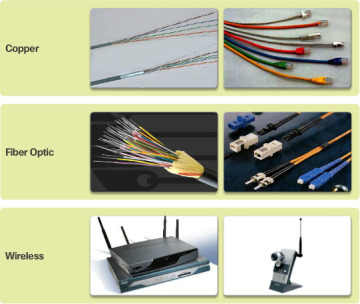
Figure 1-10 Examples of Network Media
Different types of network media have different features and benefits. Not all network media have the same characteristics, nor are they all appropriate for the same purpose.
Criteria to consider when choosing network media includes the following:
What is the maximum distance that the media can successfully carry a signal?
Into what type of environment will the media be installed?
What is the amount of data and the speed at which it must be transmitted?
What is the cost of the media and installation?
Network Representations (1.2.1.5)
Diagrams of networks often use symbols, like those shown in Figure 1-11, to represent the different devices and connections that make up a network.

Figure 1-11 Common Icons Use to Represent Network Devices
A diagram provides an easy way to understand how devices in a large network are connected. This type of “picture” of a network is known as a topology diagram. The ability to recognize the logical representations of the physical networking components is critical to being able to visualize the organization and operation of a network.
In addition to these representations, specialized terminology is used when discussing how each of these devices and media connect to each other. Important terms to remember are
Network Interface Card – A NIC, or LAN adapter, provides the physical connection to the network at the PC or other end device. The media that are connecting the PC to the networking device plug directly into the NIC (Figure 1-12).

Figure 1-12 Network Interface Card
Physical Port – A connector or outlet on a networking device where the media is connected to an end device or another networking device.
Interface – Specialized ports on a networking device that connect to individual networks. Because routers are used to interconnect networks, the ports on a router are referred to as network interfaces.
Topology Diagrams (1.2.1.6)
Topology diagrams are mandatory for anyone working with a network. They provide a visual map of how the network is connected.
There are two types of topology diagrams:
Physical topology diagrams – Identify the physical location of intermediary devices and cable installation (Figure 1-13).
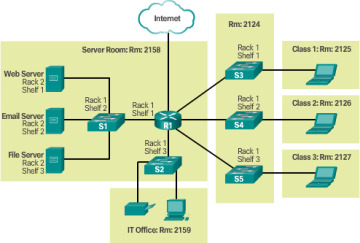
Figure 1-13 Physical Topology
Logical topology diagrams – Identify devices, ports, and addressing scheme (Figure 1-14).
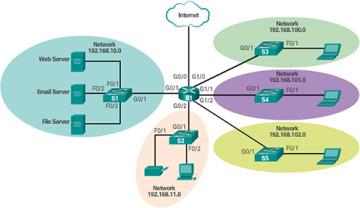
Figure 1-14 Logical Topology
The topologies shown in the physical and logical diagrams are appropriate for your level of understanding at this point in the course. Search the Internet for “network topology diagrams” to see some more complex examples. If you add the “Cisco” to your search phrase, you will find many topologies using similar icons to what you have seen in this chapter.
Activity 1.2.1.7: Network Component Representations and Functions
Go to the online course to perform this practice activity.
LANs and WANs (1.2.2)
Network infrastructures can be differentiated is various ways. Two of the most common types of network infrastructures are LANs and WANs.
Types of Networks (1.2.2.1)
Network infrastructures can vary greatly in terms of
Size of the area covered
Number of users connected
Number and types of services available
Area of responsibility
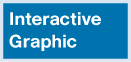
Figure 1-15 illustrates the two most common types of network infrastructures
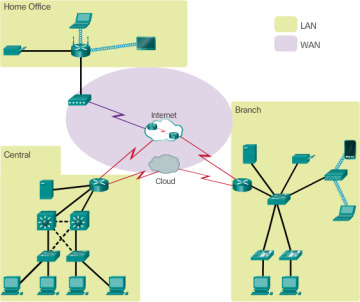
Figure 1-15 LANs and WANs
Local Area Network (LAN) – A network infrastructure that provides access to users and end devices in a small geographical area, which is typically an enterprise, home, or small business network owned and managed by an individual or IT department.
Wide Area Network (WAN) – A network infrastructure that provides access to other networks over a wide geographical area, which is typically owned and managed by a telecommunications service provider.
Play the video to watch Cisco’s Jimmy Ray Purser explains the difference between LAN and WAN.

Go to the online course to view this video.
Other types of networks include
Metropolitan Area Network (MAN) – A network infrastructure that spans a physical area larger than a LAN but smaller than a WAN (e.g., a city). MANs are typically operated by a single entity such as a large organization.
Wireless LAN (WLAN) – Similar to a LAN but wirelessly interconnects users and end points in a small geographical area.
Storage Area Network (SAN) – A network infrastructure designed to support file servers and provide data storage, retrieval, and replication.
Local Area Networks (1.2.2.2)
LANs are a network infrastructure that spans a small geographical area, as shown in Figure 1-16.
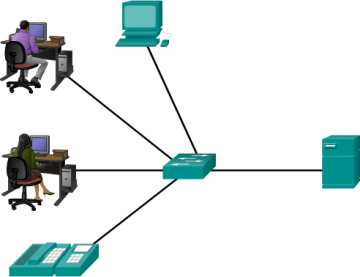
Figure 1-16 Example of a LAN
Specific features of LANs include
LANs interconnect end devices in a limited area such as a home, school, office building, or campus.
A LAN is usually administered by a single organization or individual.
LANs provide high-speed bandwidth to internal end devices and intermediary devices.
Wide Area Networks (1.2.2.3)
WANs are a network infrastructure that spans a wide geographical area, as shown in Figure 1-17. WANs are typically managed by service providers (SP) or Internet Service Providers (ISP).

Figure 1-17 Example of a WAN
Specific features of WANs include
WANs interconnect LANs over wide geographical areas such as between cities, states, provinces, countries, or continents.
WANs are usually administered by multiple service providers.
WANs typically provide slower-speed links between LANs.
The Internet, Intranets, and Extranets (1.2.3)
Most individuals need to communicate with a resource on another network, outside of the local network within the home, campus, or organization. This is done using the Internet.
The Internet (1.2.3.1)
The Internet is a worldwide collection of interconnected networks (internetworks or internet for short). Figure 1-18 one way to view the Internet as a collection of interconnected LANs and WANs.
Figure 1-18 Collection of Interconnected LANs and WANs
Some of the LAN examples are connected to each other through a WAN connection. WANs are then connected to each other. The red WAN connection lines represent all the varieties of ways we connect networks. WANs can connect through copper wires, fiber optic cables, and wireless transmissions (not shown).
The Internet is not owned by any individual or group. Ensuring effective communication across this diverse infrastructure requires the application of consistent and commonly recognized technologies and standards as well as the cooperation of many network administration agencies. There are organizations that have been developed for the purpose of helping to maintain structure and standardization of Internet protocols and processes. These organizations include the Internet Engineering Task Force (IETF), Internet Corporation for Assigned Names and Numbers (ICANN), and the Internet Architecture Board (IAB), plus many others.
Intranets and Extranets (1.2.3.2)
There are two other terms that are similar to the term Internet:
Intranet
Extranet
Figure 1-19 shows the relationship of the Internet, extranets, and intranets.
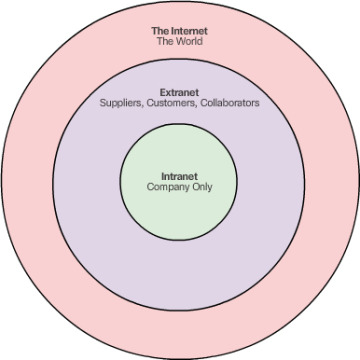
Figure 1-19 Internet, Extranet, and Intranet
Intranet is a term often used to refer to a private connection of LANs and WANs that belongs to an organization and is designed to be accessible only by the organization’s members, employees, or others with authorization.
An organization may use an extranet to provide secure and safe access to individuals who work for a different organization but require access to the organization’s data. Examples of extranets include
A company that is providing access to outside suppliers and contractors.
A hospital that is providing a booking system to doctors so they can make appointments for their patients.
A local office of education that is providing budget and personnel information to the schools in its district.
Internet Connections (1.2.4)
The type of connection to the Internet will depend on the type of network being connected. A business network will usually require a connection with more bandwidth than a home network.
Internet Access Technologies (1.2.4.1)
There are many different ways to connect users and organizations to the Internet.
Home users, teleworkers (remote workers), and small offices typically require a connection to an Internet Service Provider (ISP) to access the Internet. Connection options vary greatly between ISP and geographical location. However, popular choices include broadband cable, broadband digital subscriber line (DSL), wireless WANs, and mobile services.
Organizations typically require access to other corporate sites and the Internet. Fast connections are required to support business services including IP phones, video conferencing, and data center storage.
Business-class interconnections are usually provided by service providers (SP). Popular business-class services include business DSL, leased lines, and Metro Ethernet.
Home and Small Office Internet Connections (1.2.4.2)
Figure 1-20 illustrates common connection options for small office and home office users.
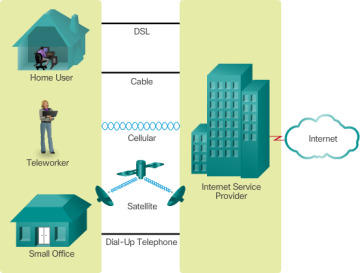
Figure 1-20 Connection Options
Cable – Typically offered by cable television service providers, the Internet data signal is carried on the same cable that delivers cable television. It provides a high bandwidth, always on, connection to the Internet.
DSL – Digital Subscriber Lines provide a high bandwidth, always on, connection to the Internet. DSL runs over a telephone line. In general, small office and home office users connect using Asymmetrical DSL (ADSL), which means that the download speed is faster than the upload speed.
Cellular – Cellular Internet access uses a cell phone network to connect. Wherever you can get a cellular signal, you can get cellular Internet access. Performance will be limited by the capabilities of the phone and the cell tower to which it is connected.
Satellite – The availability of satellite Internet access is a real benefit in those areas that would otherwise have no Internet connectivity at all. Satellite dishes require a clear line of sight to the satellite.
Dial-up Telephone – An inexpensive option that uses any phone line and a modem. The low bandwidth provided by a dial-up modem connection is usually not sufficient for large data transfer, although it is useful for mobile access while traveling.
Many homes and small offices are more commonly being connected directly with fiber optic cables. This enables an ISP to provide higher bandwidth speeds and support more services such as Internet, phone, and TV.
The choice of connection varies depending on geographical location and service provider availability.
Businesses Internet Connections (1.2.4.3)
Corporate connection options differ from home user options. Businesses may require higher bandwidth, dedicated bandwidth, and managed services. Connection options available differ depending on the type of service providers located nearby.
Figure 1-21 illustrates common connection options for businesses.
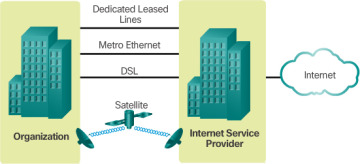
Figure 1-21 Typical Business Connection Options
Dedicated Leased Line – Leased lines are actually reserved circuits within the service provider’s network that connect geographically separated offices for private voice and/or data networking. The circuits are typically rented at a monthly or yearly rate. They can be expensive.
Ethernet WAN – Ethernet WANs extend LAN access technology into the WAN. Ethernet is a LAN technology you will learn about in a later chapter. The benefits of Ethernet are now being extended into the WAN.
DSL – Business DSL is available in various formats. A popular choice is Symmetric Digital Subscriber Lines (SDSL), which is similar to the consumer version of DSL but provides uploads and downloads at the same speeds.
Satellite – Similar to small office and home office users, satellite service can provide a connection when a wired solution is not available.
The choice of connection varies depending on geographical location and service provider availability.
 Packet Tracer 1.2.4.4: Help and Navigation Tips
Packet Tracer 1.2.4.4: Help and Navigation Tips