The Network as a Platform (1.3)
The network has become a platform for distributing a wide range of services to end users in a reliable, efficient, and secure manner.
Converged Networks (1.3.1)
Modern networks are constantly evolving to meet user demands. Today’s networks are used for data, phone, and video.
Traditional Separate Networks (1.3.1.1)
Consider a school built thirty years ago. Back then, some classrooms were cabled for the data network, telephone network, and video network for televisions. These separate networks could not communicate with each other, as shown in Figure 1-22.
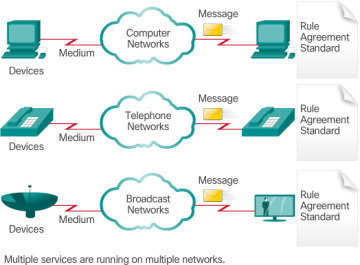
Figure 1-22 Multiple Networks
Each network used different technologies to carry the communication signal. Each network had its own set of rules and standards to ensure successful communication.
The Converging Network (1.3.1.2)
Today, the separate data, telephone, and video networks are converging. Unlike dedicated networks, converged networks are capable of delivering data, voice, and video between many different types of devices over the same network infrastructure, as shown in Figure 1-23. This network infrastructure uses the same set of rules, agreements, and implementation standards.
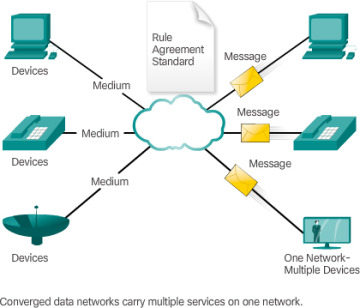
Figure 1-23 Converged Networks
Reliable Network (1.3.2)
With our reliance on networks, certain precautions must be taken to ensure that the network functions as designed, even if things go wrong. Networks must be able to expand to meet the increased needs of an organization. The services provided by the network must be secure and provide the quality of service to meet the expectations of the organization.
Network Architecture (1.3.2.1)
Networks must support a wide range of applications and services as well as operate over many different types of cables and devices, which make up the physical infrastructure. The term network architecture, in this context, refers to the technologies that support the infrastructure and the programmed services and rules, or protocols, that move data across the network.
As networks evolve, we are discovering that there are four basic characteristics that the underlying architectures need to address in order to meet user expectations:
Fault Tolerance
Scalability
Quality of Service (QoS)
Security
Fault Tolerance (1.3.2.2)
The expectation is that the Internet is always available to the millions of users who rely on it. This requires a network architecture that is built to be fault tolerant. A fault-tolerant network is one that limits the impact of a failure, so that the fewest number of devices are affected. It is also built in a way that allows quick recovery when such a failure occurs. These networks depend on multiple paths between the source and destination of a message. If one path fails, the messages can be instantly sent over a different link. Having multiple paths to a destination is known as redundancy.
One way reliable networks provide redundancy is by implementing a packet-switched network. Packet switching splits traffic into packets that are routed over a shared network. A single message, such as an email or a video stream, is broken into multiple message blocks, called packets. Each packet has the necessary addressing information of the source and destination of the message. The routers within the network switch the packets based on the condition of the network at that moment. This means that all the packets in a single message could take very different paths to the destination. In Figure 1-24, the user is not aware and is unaffected by the router dynamically changing the route when a link fails.
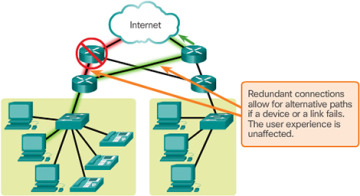
Figure 1-24 Fault Tolerance
This is not the case in circuit-switched networks traditionally used for voice communications. A circuit-switched network is one that establishes a dedicated circuit between the source and destination before the users may communicate. If the call is unexpectedly terminated, the users must initiate a new connection.
Scalability (1.3.2.3)
A scalable network can expand quickly to support new users and applications without impacting the performance of the service being delivered to existing users. Figure 1-25 shows how a new network can be easily added to an existing network.
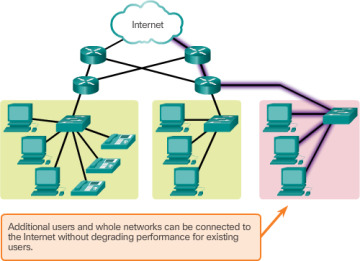
Figure 1-25 Scalability
In addition, networks are scalable because the designers follow accepted standards and protocols. This allows software and hardware vendors to focus on improving products and services without worrying about designing a new set of rules for operating within the network.
Quality of Service (1.3.2.4)
Quality of Service (QoS) is also an ever-increasing requirement of networks today. New applications available to users over internetworks, such as voice and live video transmissions, create higher expectations for the quality of the delivered services. Have you ever tried to watch a video with constant breaks and pauses? As data, voice, and video content continue to converge onto the same network, QoS becomes a primary mechanism for managing congestion and ensuring reliable delivery of content to all users.
Congestion occurs when the demand for bandwidth exceeds the amount available. Network bandwidth is measured in the number of bits that can be transmitted in a single second, or bits per second (bps). When simultaneous communications are attempted across the network, the demand for network bandwidth can exceed its availability, creating network congestion.
When the volume of traffic is greater than what can be transported across the network, devices queue, or hold, the packets in memory until resources become available to transmit them. In Figure 1-26, one user is requesting a web page and another is on a phone call. With a QoS policy in place, the router can manage the flow of data and voice traffic, giving priority to voice communications if the network experiences congestion.
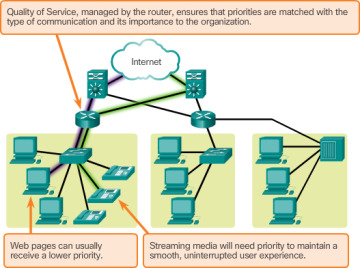
Figure 1-26 Quality of Service (QoS)
Security (1.3.2.5)
The network infrastructure, services, and the data contained on network-attached devices are crucial personal and business assets. There are two types of network security concerns that must be addressed: network infrastructure security and information security.
Securing a network infrastructure includes the physical securing of devices that provide network connectivity, and preventing unauthorized access to the management software that resides on them, as shown in Figure 1-27.
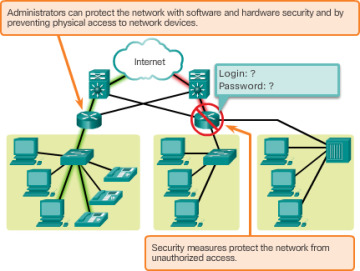
Figure 1-27 Security
Information security refers to protecting the information contained within the packets being transmitted over the network and the information stored on network attached devices. In order to achieve the goals of network security, there are three primary requirements, as shown in Figure 1-28.
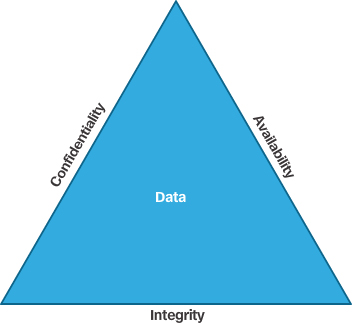
Figure 1-28 CIA Triad
Confidentiality – Data confidentiality means that only the intended and authorized recipients can access and read data.
Integrity – Data integrity means having the assurance that the information has not been altered in transmission, from origin to destination.
Availability – Data availability means having the assurance of timely and reliable access to data services for authorized users.
Activity 1.3.2.6: Reliable Networks
Go to the online course to perform this practice activity.
 Lab 1.3.1.3: Researching Converged Network Services
Lab 1.3.1.3: Researching Converged Network Services