Campus Wired LAN Designs (1.1)
Enterprise networks come in all sizes. There are small networks consisting of a few hosts, medium-sized networks consisting of a few hundred hosts, and large networks consisting of thousands of hosts. Besides the number of hosts these networks must support, consideration must be given to the applications and services that must be supported to meet the organizational goals.
Fortunately, proven methods are available to design all types of networks. The Cisco Enterprise Architecture is an example of a proven campus network design.
In this section, you will learn why it is important to design a scalable hierarchical network.
Cisco Validated Designs (1.1.1)
Networks must be scalable, which means they must be able to accommodate an increase or a decrease in size. The focus of this topic is to discover how the hierarchical design model is used to help accomplish this task.
The Need to Scale the Network (1.1.1.1)
Businesses increasingly rely on their network infrastructure to provide mission-critical services. As businesses grow and evolve, they hire more employees, open branch offices, and expand into global markets. These changes directly affect the requirements of a network.
The LAN is the networking infrastructure that provides access to network communication services and resources for end users and devices spread over a single floor or building. A campus network is created by interconnecting a group of LANs that are spread over a small geographic area.
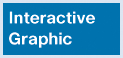
Campus network designs include small networks that use a single LAN switch, up to very large networks with thousands of connections. For example, in Figure 1-1, the company is located in a single location with one connection to the Internet.

Figure 1-1 A Small, Single-Location Company
In Figure 1-2, the company grows to multiple locations in the same city.
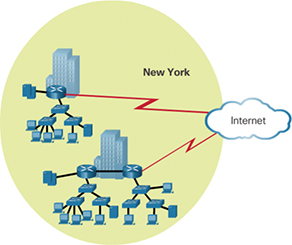
Figure 1-2 The Company Grows to Multiple Locations in the Same City
In Figure 1-3, the company continues to grow and expands to more cities. It also hires and connects teleworkers.
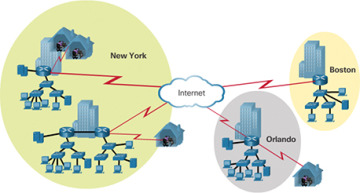
Figure 1-3 Enterprise Grows to Multiple Cities and Adds Teleworkers
In Figure 1-4, the company expands to other countries and centralizes management in a network operations center (NOC).
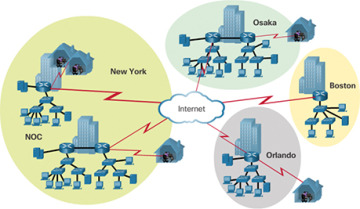
Figure 1-4 Enterprise Becomes Global and Centralizes Network Operations
In addition to supporting physical growth, a network must also support the exchange of all types of network traffic, including data files, email, IP telephony, and video applications for multiple business units.
Specifically, all enterprise networks must:
Support mission-critical services and applications
Support converged network traffic
Support diverse business needs
Provide centralized administrative control
To help campus LANs meet these requirements, a hierarchical design model is used.
Hierarchical Design Model (1.1.1.2)
The campus wired LAN enables communications between devices in a building or group of buildings, as well as interconnection to the WAN and Internet edge at the network core.
Early networks used a flat or meshed network design, in which large numbers of hosts were connected in the same network. Changes affected many hosts in this type of network architecture.
Campus wired LANs now use a hierarchical design model that divides network design into modular groups or layers. Dividing (or breaking) the network design into layers enables each layer to implement specific functions. This simplifies the network design and the deployment and management of the network.
A hierarchical LAN design consists of the following three layers, as shown in Figure 1-5:
Access layer
Distribution layer
Core layer
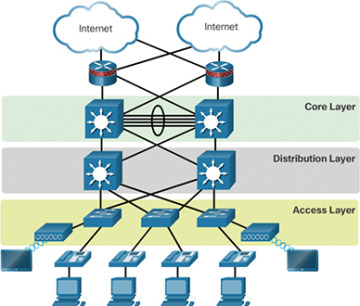
Figure 1-5 Hierarchical Design Model
Each layer is designed to meet specific functions.
The access layer provides endpoints and users direct access to the network. The distribution layer aggregates access layers and provides connectivity to services. Finally, the core layer provides connectivity between distribution layers for large LAN environments. User traffic is initiated at the access layer and passes through the other layers if the functionality of those layers is required.
Medium-sized to large enterprise networks commonly implement the three-layer hierarchical design model. However, some smaller enterprise networks may implement a two-tier hierarchical design, referred to as a collapsed core design. In a two-tier hierarchical design, the core and distribution layers are collapsed into one layer, reducing cost and complexity, as shown in Figure 1-6.

Figure 1-6 Collapsed Core
In flat or meshed network architectures, changes tend to affect a large number of systems. Hierarchical design helps constrain operational changes to a subset of the network, which makes it easy to manage and improves resiliency. Modular structuring of the network into small, easy-to-understand elements also facilitates resiliency via improved fault isolation.
Expanding the Network (1.1.2)
Networks must be scalable, which means they must be able to accommodate an increase or a decrease in size. The focus of this topic is to discover how the hierarchical design model is used to help accomplish this task.
Design for Scalability (1.1.2.1)
To support a large, medium, or small network, the network designer must develop a strategy to enable the network to be available and to scale effectively and easily. Included in a basic network design strategy are the following recommendations:
Use expandable, modular equipment or clustered devices that can be easily upgraded to increase capabilities. Device modules can be added to the existing equipment to support new features and devices without requiring major equipment upgrades. Some devices can be integrated in a cluster to act as one device to simplify management and configuration.
Design a hierarchical network to include modules that can be added, upgraded, and modified as necessary, without affecting the design of the other functional areas of the network. For example, you might create a separate access layer that can be expanded without affecting the distribution and core layers of the campus network.
Create an IPv4 or IPv6 address strategy that is hierarchical. Careful address planning eliminates the need to re-address the network to support additional users and services.
Use a router or multilayer switch to limit broadcasts and filter other undesirable traffic from the network. Use Layer 3 devices to filter and reduce traffic to the network core.
As shown in Figure 1-7, more advanced network design requirements include:
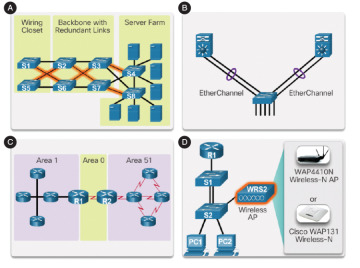
Figure 1-7 Design for Scalability
A. Redundant links—Implementing redundant links in the network between critical devices and between access layer and core layer devices.
B. Link aggregation—Implementing multiple links between equipment, with either link aggregation (EtherChannel) or equal-cost load balancing, to increase bandwidth. Combining multiple Ethernet links into a single, load-balanced EtherChannel configuration increases the available bandwidth. EtherChannel implementations can be used when budget restrictions prohibit purchasing high-speed interfaces and fiber runs.
C. Scalable routing protocols—Using a scalable routing protocol such as multiarea OSPF and implementing features within that routing protocol to isolate routing updates and minimize the size of the routing table.
D. Wireless mobility—Implementing wireless connectivity to allow for mobility and expansion.
Planning for Redundancy (1.1.2.2)
For many organizations, the availability of the network is essential to supporting business needs. Redundancy is an important part of network design for preventing disruption of network services by minimizing the possibility of a single point of failure. One method of implementing redundancy is to install duplicate equipment and provide failover services for critical devices.
Another method of implementing redundancy is using redundant paths, as shown in Figure 1-8. Redundant paths offer alternate physical paths for data to traverse the network. Redundant paths in a switched network support high availability. However, due to the operation of switches, redundant paths in a switched Ethernet network may cause logical Layer 2 loops. For this reason, Spanning Tree Protocol (STP) is required.
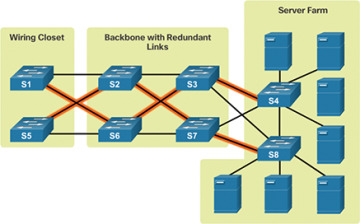
Figure 1-8 LAN Redundancy
STP eliminates Layer 2 loops when redundant links are used between switches. It does this by providing a mechanism for disabling redundant paths in a switched network until the path is necessary, such as when failures occur. STP is an open standard protocol used in a switched environment to create a loop-free logical topology.
Chapter 3, “STP,” provides more details about LAN redundancy and the operation of STP.
Failure Domains (1.1.2.3)
A well-designed network not only controls traffic but also limits the size of failure domains. A failure domain is the area of a network that is impacted when a critical device or network service experiences problems.
The function of the device that initially fails determines the impact of a failure domain. For example, a malfunctioning switch on a network segment normally affects only the hosts on that segment. However, if the router that connects this segment to others fails, the impact is much greater.
The use of redundant links and reliable enterprise-class equipment minimizes the chance of disruption in a network. Smaller failure domains reduce the impact of a failure on company productivity. They also simplify the troubleshooting process, thereby shortening the downtime for all users.
Figure 1-9 shows an example of the failure domain for a router.

Figure 1-9 Failure Domain—Router
Figure 1-10 shows an example of the failure domain for a switch.

Figure 1-10 Failure Domain—Switch
Figure 1-11 shows an example of the failure domain for a wireless access point (AP).

Figure 1-11 Failure Domain—Wireless Access Point
Because a failure at the core layer of a network can have a potentially large impact, the network designer often concentrates on efforts to prevent failures. These efforts can greatly increase the cost of implementing the network.
In the hierarchical design model, it is easiest and usually least expensive to control the size of a failure domain in the distribution layer. Limiting the size of failure domains in the distribution layer confines network errors to a smaller area and thereby affects fewer users. When using Layer 3 devices at the distribution layer, every router functions as a gateway for a limited number of access layer users.
Routers or multilayer switches are usually deployed in pairs, with access layer switches evenly divided between them. This configuration is referred to as a building switch block or a departmental switch block. Each switch block acts independently of the others. As a result, the failure of a single device does not cause the network to go down. Even the failure of an entire switch block does not affect a significant number of end users.
Increasing Bandwidth (1.1.2.4)
In hierarchical network design, some links between access and distribution switches may need to process a greater amount of traffic than other links. As traffic from multiple links converges onto a single, outgoing link, it is possible for that link to become a bottleneck.
Link aggregation allows an administrator to increase the amount of bandwidth between devices by creating one logical link by grouping several physical links together. EtherChannel is a form of link aggregation used in switched networks, as shown in Figure 1-12.

Figure 1-12 Advantages of EtherChannel
EtherChannel uses the existing switch ports. Therefore, additional costs to upgrade the link to a faster and more expensive connection are not necessary. The EtherChannel is seen as one logical link, using an EtherChannel interface.
On a Cisco Catalyst switch, an EtherChannel is configured as a port channel interface. Most configuration tasks are done on the port channel interface instead of on each individual port to ensure configuration consistency throughout the links.
Finally, the EtherChannel configuration takes advantage of load balancing between links that are part of the same EtherChannel, and depending on the hardware platform, one or more load balancing methods can be implemented.
EtherChannel operation and configuration are covered in more detail Chapter 4, “EtherChannel and HSRP.”
Expanding the Access Layer (1.1.2.5)
A network must be designed to be able to expand network access to individuals and devices as needed. An increasingly important aspect of extending access layer connectivity is wireless connectivity. Providing wireless connectivity offers many advantages, such as increased flexibility, reduced costs, and the ability to grow and adapt to changing network and business requirements.
To communicate wirelessly, end devices require a wireless network interface card (NIC) that incorporates a radio transmitter/receiver and the required software driver to make it operational. In addition, a wireless router or a wireless access point (AP) is required for users to connect, as shown in Figure 1-13.
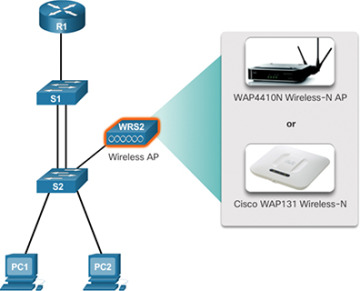
Figure 1-13 Wireless LANs
Implementing a wireless network involves many considerations, such as the types of wireless devices to use, wireless coverage requirements, interference considerations, and security considerations.
Fine-tuning Routing Protocols (1.1.2.6)
Advanced routing protocols, such as Open Shortest Path First (OSPF) and Enhanced Interior Gateway Routing Protocol (EIGRP), are used in large networks.
A link-state routing protocol such as OSPF, as shown in Figure 1-14, works well for larger hierarchical networks where fast convergence is important.
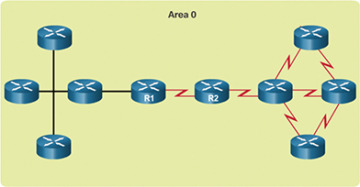
Figure 1-14 Single-Area OSPF
OSPF routers establish and maintain neighbor adjacency or adjacencies with other connected OSPF routers. When routers initiate an adjacency with neighbors, an exchange of link-state updates begins. Routers reach a FULL state of adjacency when they have synchronized views on their link-state database. With OSPF, link-state updates are sent when network changes occur. Single-area OSPF configuration and concepts are covered in Chapter 8, “Single-Area OSPF.”
In addition, OSPF supports a two-layer hierarchical design, referred to as multiarea OSPF, as shown in Figure 1-15.
All multiarea OSPF networks must have an Area 0, also called the backbone area. Non-backbone areas must be directly connected to area 0. Chapter 9, “Multiarea OSPF,” introduces the benefits, operation, and configuration of multiarea OSPF. Chapter 10, “OSPF Tuning and Troubleshooting,” covers more advanced features of OSPF.
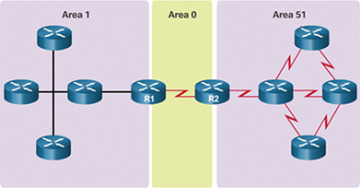
Figure 1-15 Multiarea OSPF
Another popular routing protocol for larger networks is EIGRP. Cisco developed EIGRP as a proprietary distance vector routing protocol with enhanced capabilities. Although configuring EIGRP is relatively simple, the underlying features and options of EIGRP are extensive and robust. For example, EIGRP uses protocol-dependent modules (PDM), which enable support for IPv4 and IPv6 routing tables, as shown in Figure 1-16.
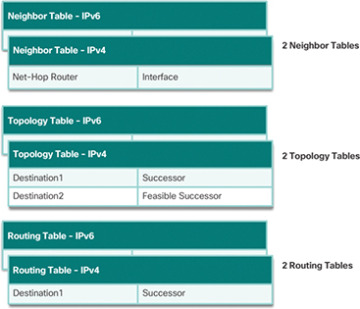
Figure 1-16 EIGRP Protocol-Dependent Modules (PDM)
EIGRP contains many features that are not found in any other routing protocols. It is an excellent choice for large multiprotocol networks that use primarily Cisco devices.
Chapter 6, “EIGRP,” introduces the operation and configuration of the EIGRP routing protocol, and Chapter 7, “EIGRP Tuning and Troubleshooting,” covers some of the more advanced configuration options of EIGRP.