Linux Overview (3.1)
In this section, you will learn Linux basics including the Linux shell and the role of Linux servers and clients.
Linux Basics (3.1.1)
In this topic, you will learn what Linux is, its value, its role in a Security Operations Center (SOC), and some of the more important Linux tools.
What is Linux? (3.1.1.1)
Linux is an operating system created in 1991. Linux is open source, fast, reliable, and small. It requires very little hardware resources to run, and is highly customizable. Unlike other operating systems such as Windows and macOS X, Linux was created, and is currently maintained, by a community of programmers. Linux is part of several platforms and can be found on devices anywhere from “wristwatches to supercomputers.”
Another important aspect of Linux is that it is designed to be connected to the network, which makes it much simpler to write and use network-based applications. Because Linux is open source, any person or company can get the kernel’s source code, inspect it, modify it, and recompile it at will. They are also allowed to redistribute the program with or without charges.
A Linux distribution is the term used to describe packages created by different organizations. Linux distributions (or distros) include the Linux kernel with customized tools and software packages. While some of these organizations may charge for their Linux distribution support (geared toward Linux-based businesses), the majority of them also offer their distribution for free without support. Debian, Red Hat, Ubuntu, CentOS, and SUSE are just a few examples of Linux distributions.
The Value of Linux (3.1.1.2)
Linux is often the operating system of choice in the SOC. These are some of the reasons to choose Linux:
Linux is open source: Any person can acquire Linux at no charge and modify it to fit specific needs. This flexibility allows analysts and administrators to tailor-build an operating system specifically for security analysis.
The Linux CLI is very powerful: While a GUI makes many tasks easier to perform, it adds complexity and requires more computer resources to run. The Linux command line interface (CLI) is extremely powerful and enables analysts to perform tasks not only directly on a terminal, but also remotely because the CLI requires very few resources.
The user has more control over the OS: The administrator user in Linux, known as the root user, or superuser, has absolute power over the computer. Unlike other operating systems, the root user can modify any aspect of the computer with a few keystrokes. This ability is especially valuable when working with low-level functions such as the network stack. It allows the root user to have precise control over the way network packets are handled by the operating system.
It allows for better network communication control: Control is an inherent part of Linux. Because the OS can be tweaked and adjusted in practically every aspect, it is a great platform for creating network applications. This is the same reason why many great network-based software tools are available for Linux only.
Linux in the SOC (3.1.1.3)
The flexibility provided by Linux is a great feature for the SOC. The entire operating system can be tailored to become the perfect security analysis platform. For example, administrators can add only the necessary packages to the OS, making it lean and efficient. Specific software tools can be installed and configured to work in conjunction, allowing administrators to build a customized computer that fits perfectly in the workflow of an SOC.
These are a few tools that are often found in an SOC:
Network packet capture software: This software is used for network packet captures. This is a crucial tool for an SOC analyst as it makes it possible to observe and understand every detail of a network transaction. Figure 3-1 shows a screenshot of Wireshark, a popular packet capture tool.
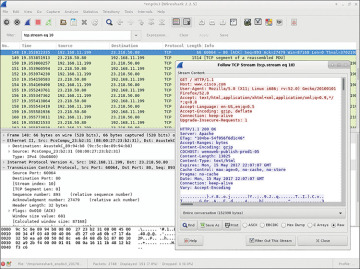
Figure 3-1 Wireshark Capture of a Web Page Request
Malware analysis tools: In the case of new malware detection, these tools allow analysts to safely run and observe malware execution without the risk of compromising the underlying system.
Intrusion detection systems (IDSs): These tools are used for real-time traffic monitoring and inspection. If any aspect of the currently flowing traffic matches any of the established rules, a predefined action is taken.
Firewalls: This software is used to specify, based on predefined rules, whether traffic is allowed to enter or leave the network.
Log managers: Log files are used to record events. Because a large network can generate a very large number of events log entries, log managers are employed to facilitate log monitoring.
Security information and event management (SIEM): SIEM systems provide real-time analysis of alerts and log entries generated by network appliances such as IDSs and firewalls.
Ticketing systems: Ticket assignment, editing, and recording is done through a ticket management system.
Linux Tools (3.1.1.4)
In addition to SOC-specific tools, Linux computers used in the SOC often contain penetration testing tools. Also known as pentesting, penetration testing is the process of looking for vulnerabilities in a network or computer by attacking it. Packet generators, port scanners, and proof-of-concept exploits are examples of penetration testing tools.
Kali Linux is a Linux distribution created to group many penetration tools. Kali contains a great selection of penetration testing tools. Figure 3-2 shows a screenshot of Kali Linux. Notice all the major categories of penetration testing tools.
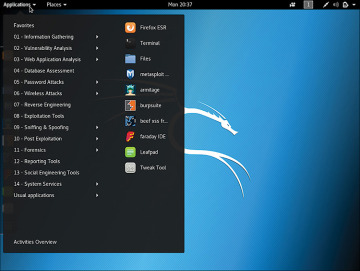
Figure 3-2 Kali Linux Tool Categories
Working in the Linux Shell (3.1.2)
In this topic, you will learn about the Linux shell, including common commands used in the CLI and working with text files.
The Linux Shell (3.1.2.1)
In Linux, the user communicates with the OS by using the CLI or the GUI. Linux often boots into the GUI by default, hiding the CLI from the user. One way to access the CLI from the GUI is through a terminal emulator application. These applications provide user access to the CLI and are often named as some variation of the word “terminal.” In Linux, popular terminal emulators are Terminator, eterm, xterm, konsole, and gnome-terminal.
To experience the Linux CLI in your web browser, go to the following website:
Type the ls command to list the current directory content. Keep the tab open if you would like to try out some of the other commands discussed in this chapter.
Figure 3-3 shows gnome-terminal, a popular Linux terminal emulator.
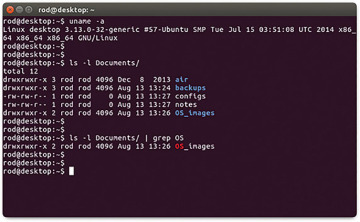
Figure 3-3 Gnome Terminal
Basic Commands (3.1.2.2)
Linux commands are programs created to perform a specific task. Use the man command (short for manual) to obtain documentation about commands. As an example, man ls provides documentation about the ls command from the user manual.
Because commands are programs stored on the disk, when a user types a command, the shell must find it on the disk before it can be executed. The shell will look for user-typed commands in specific directories and attempt to execute them. The list of directories checked by the shell is called the path. The path contains many directories commonly used to store commands. If a command is not in the path, the user must specify its location or the shell will not be able to find it. Users can easily add directories to the path, if necessary.
To invoke a command via the shell, simply type its name. The shell will try to find it in the system path and execute it.
Table 3-1 shows a list of some basic Linux commands and their functions.
Table 3-1 Basic Linux Commands
Command |
Description |
mv |
Used to move or rename files and directories. |
chmod |
Used to modify file permissions. |
chown |
Used to change the ownership of a file. |
dd |
Used to copy data from an input to an output. |
pwd |
Used to display the name of the current directory. |
ps |
Used to list the processes currently running on the system. |
su |
Used to simulate a login as another user or to become a superuser. |
sudo |
Used to run a command as another user. |
grep |
Used to search for specific strings of characters within a file or other commands’ outputs. To search through the output of a previous command, grep must be piped at the end of the previous command. |
ifconfig |
Used to display or configure network card–related information. If issued without parameters, ifconfig will display the configuration of the current network card(s). |
apt-get |
Used to install, configure, and remove packages on Debian and its derivatives. Note: apt-get is a user-friendly command line front end for dpkg, Debian’s package manager. The combo dpkg and apt-get is the default package manager system in all Debian Linux derivatives, including Raspbian. |
iwconfig |
Used to display or configure wireless network card–related information. Similar to ifconfig, iwconfig will display wireless information when issued without parameters. |
shutdown |
Used to shut down the system. shutdown can be instructed to perform a number of shutdown-related tasks, including restart, halt, put to sleep, or kick out all currently connected users. |
passwd |
Used to change the password. If no parameters are provided, passwd changes the password for the current user. |
cat |
Used to list the contents of a file and expects the filename as the parameter. The cat command is usually used on text files. |
man |
Used to display the documentation for a specific command. |
File and Directory Commands (3.1.2.3)
Many command line tools are included in Linux by default. To adjust the command operation, users can pass parameters and switches along with the command. Table 3-2 shows a few of the most common commands related to files and directories.
Table 3-2 Common File and Directory Commands
Command |
Description |
ls |
Displays the files inside a directory |
cd |
Changes the current directory |
mkdir |
Creates a directory under the current directory |
cp |
Copies files from source to destination |
mv |
Moves files to a different directory |
rm |
Removes files |
grep |
Searches for specific strings of characters within a file or other commands’ outputs |
cat |
Lists the contents of a file and expects the filename as the parameter |
Working with Text Files (3.1.2.4)
Linux has many different text editors, with various features and functions. Some text editors include graphical interfaces while others are command line–only tools. Each text editor includes a feature set designed to support a specific type of task. Some text editors focus on the programmer and include features such as syntax highlighting, brackets, parentheses, checks, and other programming-focused features.
While graphical text editors are convenient and easy to use, command line–based text editors are very important for Linux users. The main benefit of command line–based text editors is that they allow for text file editing from a remote computer.
Consider the following scenario: a user must perform administrative tasks on a Linux computer but is not sitting in front of that computer. Using Secure Shell (SSH), the user starts a remote shell to the remote computer. Under the text-based remote shell, the graphical interface is not available, which makes it impossible to rely on tools such as graphical text editors. In this type of situation, text-based programs are crucial.
Figure 3-4 shows nano (or GNU nano), a popular command-line text editor. The administrator is editing firewall rules. Text editors are often used for system configuration and maintenance in Linux.
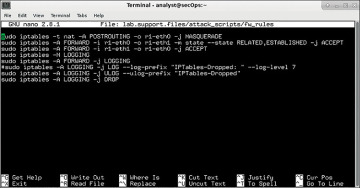
Figure 3-4 The nano Text Editor
Due to the lack of graphical support, nano can only be controlled with the keyboard. For example, CTRL-O saves the current file; CTRL-W opens the search menu. GNU nano uses a two-line shortcut bar at the bottom of the screen, where commands for the current context are listed. Press CTRL-G for the help screen and a complete list of commands.
The Importance of Text Files in Linux (3.1.2.5)
In Linux, everything is treated as a file, including the memory, the disks, the monitor, the files, and the directories. For example, from the operating system standpoint, showing information on the display means to write to the file that represents the display device. It should be no surprise that the computer itself is configured through files. Known as configuration files, they are usually text files used to store adjustments and settings for specific applications or services. Practically everything in Linux relies on configuration files to work. Some services have not one but several configuration files.
Users with proper permission levels can use text editors to change the contents of configuration files. After the changes are made, the file is saved and can be used by the related service or application. Users are able to specify exactly how they want any given application or service to behave. When launched, services and applications check the contents of specific configuration files to adjust their behavior accordingly.
In Figure 3-5, the administrator opened the host configuration file in nano for editing. Only the superuser can change the host file.
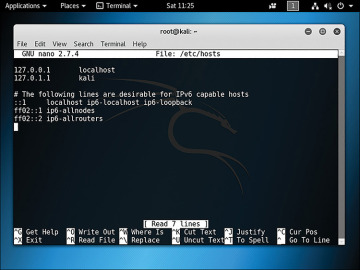
Figure 3-5 Editing a Text File in nano
Linux Servers and Clients (3.1.3)
In this topic, you will learn about Linux client-server communications.
An Introduction to Client-Server Communications (3.1.3.1)
Servers are computers with software installed that enables them to provide services to clients. There are many types of services. Some provide resources such as files, email messages, or web pages to clients upon request. Other services run maintenance tasks such as log management, memory management, disk scanning, and more. Each service requires separate server software. For example, the server in Figure 3-6 requires file server software to provide clients with the ability to retrieve and submit files.
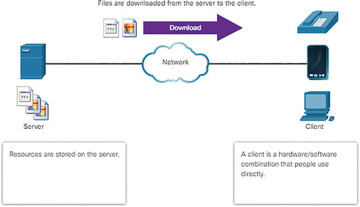
Figure 3-6 Server Sending Files to Client
Client-server communications is discussed in more detail later in the course.
Servers, Services, and Their Ports (3.1.3.2)
For a computer to be the server for multiple services, ports are used. A port is a reserved network resource used by a service. A server is said to be “listening” on a port when it has associated itself to that port.
While the administrator can decide which port to use with any given service, many clients are configured to use a specific port by default. To make it easier for the client, it is common practice to leave the service running in its default port. Table 3-3 shows a few commonly used ports and their services. These are also called “well-known ports.”
Table 3-3 Common Port Numbers and Services
Port Number |
Service |
21 |
File Transfer Protocol (FTP) |
22 |
Secure Shell (SSH) |
23 |
Telnet remote login service |
25 |
Simple Mail Transfer Protocol (SMTP) |
53 |
Domain Name System (DNS) |
80 |
Hypertext Transfer Protocol (HTTP) |
110 |
Post Office Protocol version 3 (POP3) |
123 |
Network Time Protocol (NTP) |
161 |
Internet Message Access Protocol (IMAP) |
161 |
Simple Network Management Protocol (SNMP) |
443 |
HTTP Secure (HTTPS) |
Ports and their uses in network communications are discussed in more detail later in the course.
Clients (3.1.3.3)
Clients are programs or applications designed to communicate with a specific server. Also known as client applications, clients use a well-defined protocol to communicate with the server. Web browsers are web clients used to communicate with web servers via the Hypertext Transfer Protocol (HTTP). The File Transfer Protocol (FTP) client is software used to communicate with an FTP server. Figure 3-7 shows a client uploading files to a server.
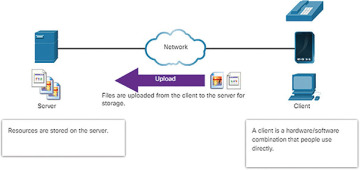
Figure 3-7 Client Uploading File to Server
 LAB 3.1.2.6: WORKING WITH TEXT FILES IN THE CLI
LAB 3.1.2.6: WORKING WITH TEXT FILES IN THE CLI