Because Cisco Identify Services Engine (ISE) is positioned to know exactly who and what is on the network at any given time, as well as assign different levels of access and context assignments with security group tags, it is the perfect security tool to be at the center of a security ecosystem.
There are so many tools that may exist within your “security toolbox”: firewalls, next-generation firewalls (NGFWs), intrusion prevention systems (IPSs), NG-IPSs, security information and event management (SIEM) systems, secure web gateways, threat defense tools, vulnerability assessment scanners, mobile device managers, and more. Most of these tools do not know the identity of the user, only the identity of the endpoint. These other tools can be made even more valuable by integrating into a full security ecosystem with ISE.
Wouldn’t the reporting in the SIEM be more valuable if it showed which user was involved in the security event, instead of only the IP address or MAC address? What about when your intrusion prevention tools or threat defense solutions identify malicious activity on the network? Wouldn’t it be great if they could trigger something that would change the way the endpoint was treated on the network? With a single “trigger,” the endpoint’s level of network access could be changed, the endpoint’s traffic could be inspected deeper as it passes through a Cisco Adaptive Security Appliance (ASA), the Cisco Web Security Appliance (WSA) can apply a different SSL decryption policy, and so much more.
You’ve already read about ISE integrating with mobile device managers (MDMs) and a little bit on how ISE can provide passive identities to ecosystem partners through technologies like pxGrid, but it can also provide the single point of policy control for threat containment and context setting.
The Many Integration Types of the Ecosystem
An integration might be ISE sharing data outbound, or it may be ISE steering traffic toward another solution. The integration method could be with ISE receiving information inbound for use within ISE’s own network access policies, or even ISE brokering data exchange between other members of the security system.
MDM Integration
In Chapter 4, “Extending Network Access with ISE,” you read about BYOD and the integration between ISE and mobile device management solutions. That integration is twofold: ISE provides the redirection to the MDM service for onboarding, but the MDM service is also able to provide “context-in” to ISE. In other words, the MDM service tells ISE about the mobile endpoints, the endpoint’s compliance with the security policies set in the MDM (macro-level compliance), the status of encryption or pin lock, and more (micro-level compliance).
This integration uses a specific bidirectional application programming interface (API) between ISE and the MDM solution (cloud service or appliance). This API is unique and created just for MDM integration.
Rapid Threat Containment
MDM is one of the first and most common integration types for ISE. In true Cisco marketing fashion, this next integration type, Rapid Threat Containment, has gone through several different names and marketing initiatives.
There was a feature added back in ISE 1.1 called Endpoint Protection Services (EPS). EPS provided an API allowing other applications to initiate three actions against an endpoint based on IP address or MAC address:
Quarantine: The quarantine action set the binary flag on the endpoint record to “true,” added the endpoint to a list of quarantined endpoints, and allowed the administrator to create authorization policies that used that assignment to assign a different level of network access.
Unquarantine: Removed the endpoint from the list of quarantined endpoints and cleared the binary flag.
Shutdown: Was supposed to send a Change of Authorization (CoA) terminate to the network and shut down the port on the network switch.
Many of the first integrations with ISE used EPS, including the original integration with Lancope StealthWatch (now Cisco Stealthwatch), where an endpoint was quarantined from the StealthWatch user interface.
Figure 6-1 illustrates a flow with Stealthwatch initiating an EPS quarantine.
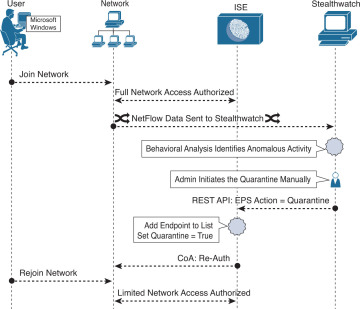
Figure 6-1 Stealthwatch to ISE: EPS Quarantine
The flow illustrated in Figure 6-1 shows an endpoint being admitted to the network with full access. The Stealthwatch admin initiates a quarantine, and Stealthwatch connects to ISE using the EPS REST API, telling ISE to quarantine the endpoint with the specific IP address.
ISE then adds the endpoint to the EPS list and sets the flag on the endpoint object and sends a CoA to the network.
When the new access request comes in, a rule created with the EPSStatus condition will be matched. Figure 6-2 shows that condition.

Figure 6-2 EPSStatus Authorization Condition
The resulting network authorization may provide for limited access, or even set a new Security Group Tag (SGT) that can be acted upon differently at miscellaneous points in the network, such as the Web Security Appliance.
Well, ultimately EPS was just too rigid. It provided for only a single actionable classification (Quarantine). More flexibility was needed to provide many different options, but also to be integrated into this new-fangled context-sharing technology that Cisco was creating named pxGrid. So, it needed to evolve into “EPS 2.0” or something like it.
So, ISE 1.3 introduced something new named Adaptive Network Control (ANC), which was a huge step forward by simply renaming EPS to ANC. Okay, hopefully the sarcasm was obvious there.
ISE 1.4 actually added new functionality to ANC. While still supporting the old EPS API calls for backward-compatibility purposes, it also added a new API with different labels available, including the ability to create your own label.
ISE refers to these labels as ANC “policies,” but there is no policy to them whatsoever. An ANC policy is a tag or a label that gets assigned to an endpoint object and can be used in the authorization policy to invoke some action, such as changing the authorization level and assigning a new SGT.
Although you can add many different labels, there are only three choices for ANC policies: Quarantine, Shut Down, and Port Bounce—which determines the CoA type used when the label is applied to the endpoint.
To create an ANC policy (a.k.a. label), navigate to Operations > Adaptive Network Control > Policy List and click Add. Figure 6-3 shows the resulting page with the Action drop-down menu open.

Figure 6-3 Adding an ANC Policy
You can create multiple ANC policies, and each policy may contain one or more actions. Each ANC policy can be associated to a different authorization. For example, you can end up with ANC policies such as:
Investigate
Phasers on Stun
Eradicate
Nuke from Orbit
In addition to a much more flexible approach to classification, or as Cisco’s legendary Paul Forbes would call it, “flexible name spaces,” ANC also integrates tightly with pxGrid, allowing pxGrid subscribers to trigger the ANC action within the pxGrid connection, not through the point API of the past.
So now you have Endpoint Protection Services which was renamed to Adaptive Network Control. Then Adaptive Network Control gets new functionality in ISE 1.4. Then Cisco security marketing gets involved and comes up with a new naming convention to refer to the entire integrated security system where any Cisco security product may take action through another Cisco security product.
That name is Rapid Threat Containment. You have solutions like: Rapid Threat Containment with Cisco Stealthwatch and the Identity Services Engine and Rapid Threat Containment with Cisco Firepower Management Center and Identity Services Engine.
While ISE is often the center of a security ecosystem, the Rapid Threat Containment portfolio includes more than just integrations with ISE. There are solutions like Rapid Threat Containment with Firepower Management Center and Cisco Stealthwatch, Firepower and Cisco Tetration, and many more. Actions taken using Cisco Threat Response are also part of the Rapid Threat Containment umbrella (no pun intended).
Crystal clear, right?
Cisco’s platform eXchange Grid (pxGrid)
Now that you are thoroughly confused about the marketing term “Rapid Threat Containment”, let’s clear up one thing. Rapid Threat Containment may leverage pxGrid for the integration between two or more Cisco security products, but pxGrid is not a requirement. Many of those integrations are handled by API’s or other connection types.
What is this pxGrid thing that we keep talking about?
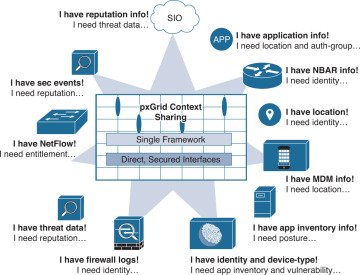
pxGrid is Cisco’s premier publish and subscribe (pub/sub) communication bus that was designed from the ground up to be a scalable, secure data sharing system.
Like most other next-generation AAA solutions, ISE originally started sharing information through the use of APIs. It was quickly recognized that point APIs would not scale to the level of data that needed to be shared and the scale of which it was requested.
Cisco went down the path of a pub/sub bus, similar to the way Cisco Unified Communications Manager (formerly known as Call Manager) and Cisco Jabber work. A controller keeps track of all the topics that exist. A topic is a list of information that is available. A topic might be session data of who and what is on the network, or it might be a list of vulnerable endpoints and the list of those vulnerabilities.
pxGrid participants can subscribe to any topic of interest and be notified when there is data to be retrieved. Those participants are known as subscribers. The true source of the data can be any other pxGrid participant, known as publishers. A publisher registers the topic with the controller, who performs the authorization for each subscriber to retrieve the data from the miscellaneous publishers.
Figure 6-4 shows the standard Cisco drawing that is often used to explain pxGrid. In this illustration, you see many different types of products, each of which has different information to publish and needs information from one of the other products.
pxGrid was initially added to ISE in version 1.3, so it’s been around for a while now and has an ecosystem of partner applications that continue to grow at a very rapid pace.
ISE 2.2 made great strides in enhancing pxGrid. Most of the pxGrid-related enhancements are around ease of use, making it even easier to configure and maintain. ISE 2.2 also added more information into ISE’s pxGrid topics for consumption by the subscribers. A specific example of additional information that was added to pxGrid topics in ISE version 2.2 is the list of groups that each active user is a member of; and that list was shared within the same topic(s) that was used in previous ISE versions, enabling backward compatibility seamlessly.