Replication Pair Overview
Once a replication network is configured and tested, pairing a replication cluster is the next step. Creating a replication cluster pair is a prerequisite for setting up VMs for replication. The replication network and at least one datastore must be configured before the replication pair can be created.
By pairing cluster 1 with cluster 2, you are specifying that all VMs on cluster 1 that are explicitly set up for replication can replicate to cluster 2 and that all VMs on cluster 2 that are explicitly set up for replication can replicate to cluster 1.
By pairing datastore A on cluster 1 with datastore B on cluster 2, you are specifying that for any VM on cluster 1 that is set up for replication, if it has files in datastore A, those files will be replicated to datastore B on cluster 2. Similarly, for any VM on cluster 2 that is set up for replication, if it has files in datastore B, those files will be replicated to data-store A on cluster 1.
Pairing is strictly one to one. A cluster can be paired with no more than one other cluster. A datastore on a paired cluster can be paired with no more than one datastore on the other cluster.
Procedure for Creating Replication Pair
To create a replication pair, create a datastore on the local network and create a datastore on the remote network. Then follow these steps:
Step 1. From HX Connect, log in to either the local cluster or the remote cluster as a user with administrator privileges.
Step 2. Select the Replication page and then select Pair Cluster, which will bring up the Create New Replication Pair window. Figure 6-10 shows where to pair the new cluster for replication in HX Connect.
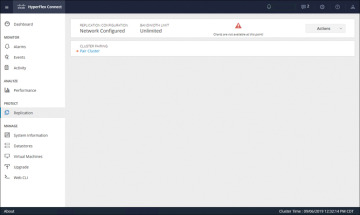
Figure 6-10 Replication Pair Cluster
Step 3. Enter a name for the replication pair on the Name tab, as shown in Figure 6-11, and click Next. The name, which cannot be changed, is set for both the local and remote clusters.
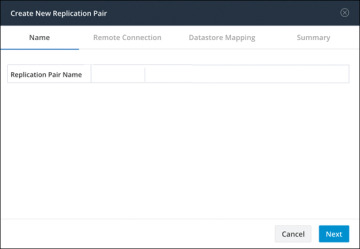
Figure 6-11 Replication Pair Name
Step 4. On the Remote Connection tab (see Figure 6-12), enter the following information:
Management IP or FQDN: The IP address or FQDN for the remote HX storage cluster
Username: The vCenter single sign-on or cluster-specific administrator username of the remote HX storage cluster
Password: The vCenter single sign-on or cluster-specific password of the remote HX storage cluster
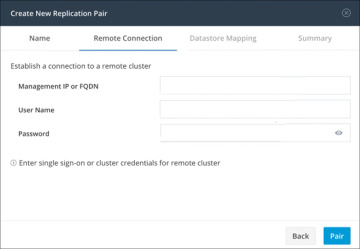
Figure 6-12 Replication Remote Connection
When you’re done with these entries, click Pair to pair with the replication remote cluster.
Step 5. Go to the Datastore Mapping tab, as shown in Figure 6-13, to view the data-store mapping between the local and remote clusters. The Local Datastore column shows the list of the configured datastores on the local HX storage cluster. The Remote Datastore column pairs the datastores between the HX storage clusters. Click Next.
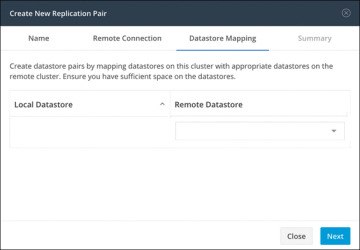
Figure 6-13 Datastore Mapping Between Clusters
Step 6. On the Summary tab, shown in Figure 6-14, review the summary of the data-store mapping. The Datastore field indicates the selected datastore on this local HX storage cluster. The Target Datastore field indicates the datastore on the remote HX storage cluster to which the replication snapshot is copied. Click Map Datastores.
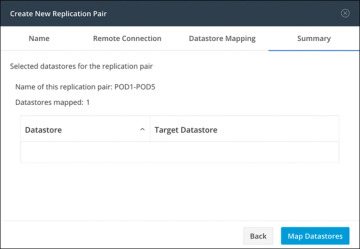
Figure 6-14 Datastore Mapping Summary
Protecting Virtual Machines
After a replication cluster is formed, the next step is to protect the virtual machines in the clusters. The following attributes are required to protect the virtual machines:
Replication interval, which is the frequency of replication
A start time (within the next 24 hours), which specifies the first time replication is attempted for that virtual machine
Whether the replication snapshot should be taken with the virtual machine quiesced or not
Protection attributes can be created and assigned to protection groups. To assign the protection attributes to virtual machines, you can add them to a protection group. For example, suppose there are three classes of protection: gold, silver, and bronze. You can set up a protection group for each class, with replication intervals such as 5 or 15 minutes for gold, 4 hours for silver, and 24 hours for bronze. Most of your VMs could be protected by merely adding them to one of the three already created protection groups.
To protect virtual machines, you can choose from the following methods:
Independently: Select one virtual machine and configure it. Set the replication schedule and the VMware quiesce option for the specific virtual machine. Changes to the replication settings will only affect the independently protected virtual machine. The virtual machine is not included in a protection group.
Existing protection group: Select one or more virtual machines and add them to an existing protection group. The schedule and VMware quiesce option settings are applied to all the virtual machines in the protection group. When the protection group settings are changed, the changes are applied to all the virtual machines in the protection group.
New protection group: Select two or more virtual machines and choose to create a new protection group. Define the protection group name, schedule, and VMware quiesce option settings. These settings are applied to all the virtual machines in the protection group. When the protection group settings are changed, the changes are applied to all the virtual machines in the protection group.
Creating Protection Groups
Protection groups provide protection to the VMs where they are created. If protection groups have protected virtual machines that replicate to the remote cluster, these protection groups are listed in HX Connect. Before staring the configuration, ensure that replication network and replication pair are configured. Then follow these steps:
Step 1. Log in to HX Connect as an administrator.
Step 2. On the Replication page, click Create Group (see Figure 6-15.
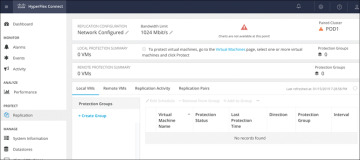
Figure 6-15 Creating a Protection Group
Step 3. Enter the following information in the Create Protection Group dialog (see Figure 6-16):
Protection Group Name: The name for the new protection group for this local cluster
Protect virtual machines in this group every: The frequency at which virtual machines are to be replicated to the paired cluster
Start protecting the virtual machines immediately: Radio button to start replication immediately after adding the first virtual machine to the protection group
Start protecting the virtual machines at: Radio button to set a specific time for the first replication to start
Use VMware Tools to quiesce the virtual machine: Check box to have HX Data Platform quiesce the virtual machines before taking the replication snapshot
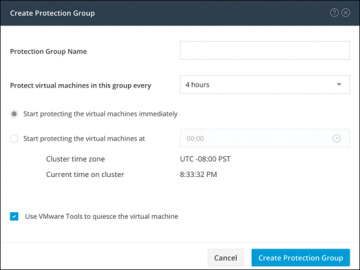
Figure 6-16 Protection Group Settings
Before starting replication, ensure that at least one virtual machine is added to the protection group and the scheduled start time is reached. To specify the protection start time, click in the time field and select an hour and minute.
Step 4. Click Create Protection Group to add the new group to the Protection Groups tab.
When the protection group is created, the next step is to add virtual machines to the created group.
Protecting Virtual Machines
This section describes how to protect multiple virtual machines using an existing protection group. Before starting, make sure that the replication network and replication pair are configured and that a protection group is created prior to adding the virtual machines. Then follow these steps:
Step 1. Log in to HX Connect as an administrator.
Step 2. On the Virtual Machines page, select one or more unprotected virtual machines from the list (see Figure 6-17).
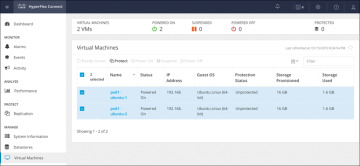
Figure 6-17 Virtual Machine Display Window
Step 3. Click Protect.
Step 4. In the Protect Virtual Machines dialog (see Figure 6-18), verify the selected virtual machine name(s), storage provisioned, and storage used by the VMs
Add to an existing protection group: Click this radio button to select an existing protection group from the pull-down list.
Create a new protection group: Select this radio button to create a new protection group for the local cluster.
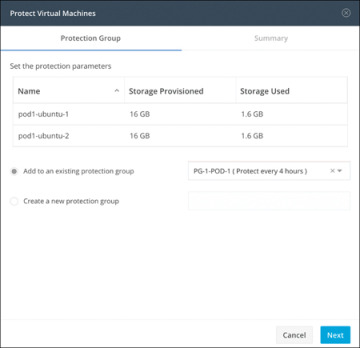
Figure 6-18 Protect Virtual Machines Window: Protection Group Tab
Step 5. Click Next.
Step 6. Confirm the information shown on the Summary tab (see Figure 6-19) and click Add to Protection Group.
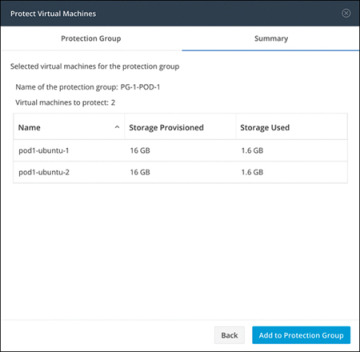
Figure 6-19 Protect Virtual Machines Window: Summary Tab