Configuring Centralized Web Authentication
Multiple devices need to be configured to enable CWA. The network access device (NAD) requires some special configuration, such as a redirection ACL; in addition, ISE needs authentication and authorization rules set up for CWA. The following sections look at these configurations.
Cisco Switch Configuration
With secure network access using ISE, the switch performs the URL redirection for Web Authentication and also redirects the discovery traffic from the posture agent to the ISE policy service node.
Performing URL redirection at the Layer 2 access (edge) device is a vast improvement over previous NAC solutions, which requires an appliance (such as the inline device) to capture web traffic and perform redirection to a Web Authentication page. URL redirection at the Layer 2 access device simplifies Web Authentication deployment, device onboarding, and the posture agent discovery process.
Configure Certificates on the Switch
In order to redirect HTTPS traffic, there is a prerequisite for the switch to have its own certificate. To configure a certificate, perform the following tasks in global configuration mode on a switch:
Step 1. To set the DNS domain name on the switch, type ip domain-name domain-name at the global configuration prompt. Now that the domain name is configured, and the keys can be generated.
Step 2. To generate keys to be used for HTTPS, type crypto key generate rsa general-keys mod 2048 at the global configuration prompt.
Enable the Switch HTTP/HTTPS Server
The embedded HTTP/HTTPS server in IOS is used to grab HTTP traffic from the user and redirect that user’s browser to the Centralized Web Authentication portal or to a device registration portal or even to the mobile device management onboarding portal. This same function is used for redirecting the posture agent’s traffic to the Policy Services node. Follow these steps to enable the switch HTTP/HTTPS server:
Step 1. Enable the HTTP server by entering the following command in global configuration mode:
C3850(config)# ip http server
Step 2. Enable the HTTP secure server by entering the following command:
C3850(config)# ip http secure-server
Many organizations need to ensure that this redirection process, which is using the switch’s internal HTTP server, is decoupled from the management of the switch itself. To disconnect the HTTP management process from the URL-redirection process, run the following two commands in global configuration mode:
C3850(config)# ip http active-session-modules none
C3850(config)# ip http secure-active-session-modules none
Verify the URL-Redirect ACL
In Chapter 11, you created an access list named ACL-WEBAUTH-REDIRECT, which is used to determine what traffic is redirected to the CWA portal with the permit statement. Any traffic that is denied is not redirected.
Contrary to the way a wireless LAN controller works, the URL-Redirect ACL on a switch is used only to determine what traffic is redirected and what traffic is not redirected. If network traffic is denied from redirection, it is not necessarily denied the ability to traverse the network. The traffic-filtering capability comes from the downloadable ACL (dACL) that is sent to the switch from ISE as part of the authorization result.
The use of dual ACLs is limited to IOS-based wired and wireless devices. (The AirespaceOS wireless controllers behave differently and are covered later in this chapter.) Follow these steps to verify the URL-Redirect ACL:
Step 1. Validate whether the ACL-WEBAUTH-REDIRECT ACL is configured on the NAD by entering the following command:
C3850# show ip access-list ACL-WEBAUTH-REDIRECT Extended IP access list ACL-WEBAUTH-REDIRECT 10 deny udp any any eq domain 20 permit tcp any any eq www 30 permit tcp any any eq 443
If the ACL is not there or needs to be modified, continue to step 2.
Step 2. Add the following ACL to be used for URL redirection with Web Authentication:
C3850(config)# ip access-list ext ACL-WEBAUTH-REDIRECT C3850(config-ext-nacl)# remark explicitly deny DNS from being redirected to address a bug C3850(config-ext-nacl)# deny udp any any eq 53 C3850(config-ext-nacl)# remark redirect all applicable traffic to the ISE Server C3850(config-ext-nacl)# permit tcp any any eq 80 C3850(config-ext-nacl)# permit tcp any any eq 443 C3850(config-ext-nacl)# remark all other traffic will be implicitly denied from the redirection
Cisco WLC Configuration
Cisco switches are responsible for redirecting web browser traffic to the centralized portal(s), and Cisco WLCs must do the same thing.
Validate That MAC Filtering Is Enabled on the WLAN
The MAC Filtering option for an open wireless network configures a WLAN for wireless MAB. This is necessary to ensure that an authentication is sent from the WLC to ISE, so ISE can return the URL redirection in the authorization result.
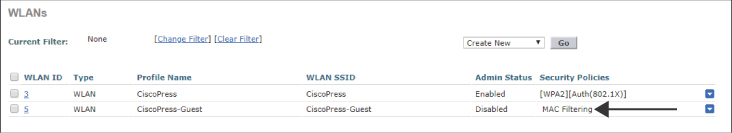
From the WLC’s GUI, navigate to the WLANs tab, examine the list of WLANs, and ensure that MAC Filtering is listed in the Security Policies column, as shown for the CiscoPress-Guest SSID in Figure 12-4.
Validate That ISE NAC Is Enabled on the WLAN
The ISE NAC feature is a very important setting. It is critical to allow for URL redirection, Centralized Web Authentication, posture assessment, native supplicant provisioning, and more.
From the WLC GUI, follow these steps:
Step 1. Navigate to WLANs > and select your open SSID.
Step 2. Click on the Advanced tab.
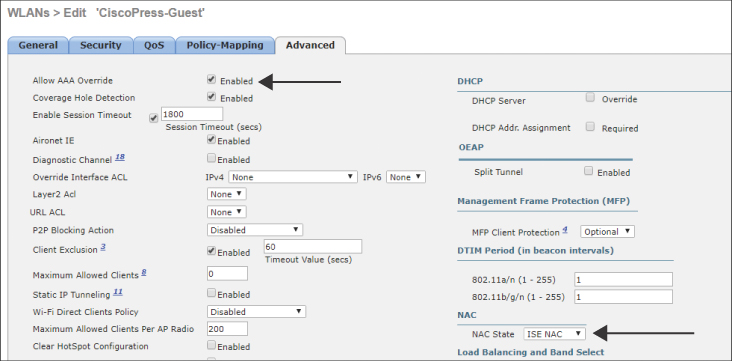
Step 3. Ensure that NAC State is forest to ISE NAC, as shown in Figure 12-5. In the same screen, ensure that Allow AAA Override is set to Enabled.
Validate That the URL-Redirection ACL Is Configured
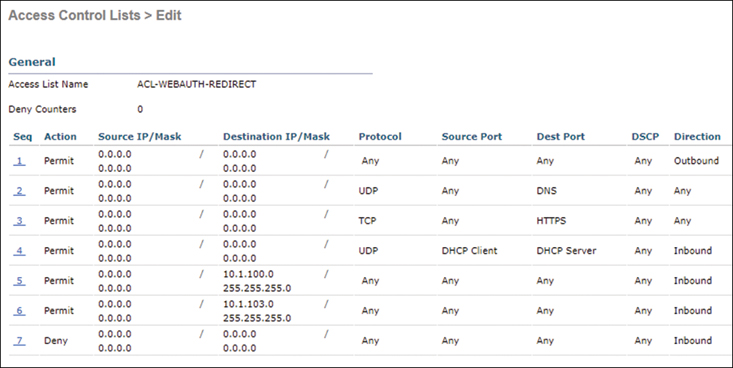
The last critical item you need to ensure exists in the WLC configuration is an ACL to use for URL redirections. In Chapter 11, you created an ACL named ACL-WEBAUTH-REDIRECT, which is used to determine what traffic is redirected to the CWA portal with the deny statement. Any traffic that is permitted is not redirected.
Unlike IOS-based NADs, AirespaceOS-based wireless controllers use a single ACL to determine which traffic to redirect and which traffic to permit through. In other words, both redirection and traffic filtering are handled by a single ACL. Therefore, the logistics of which traffic is redirected are not the same as with IOS-based devices. With Cisco WLCs, a deny statement means that traffic should be redirected. A permit statement allows the traffic through the WLC and bypasses the redirection.
In the WLC GUI, follow these steps:
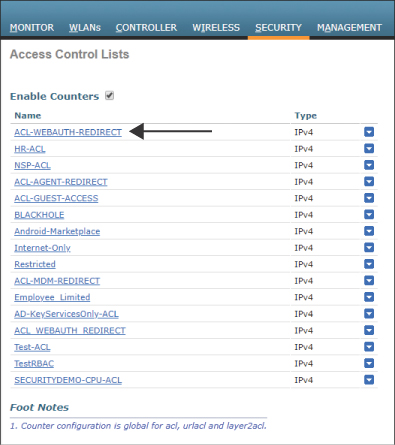
Step 1. Navigate to Security > Access-Control-Lists > Access-Control Lists. Ensure that the ACL-WEBAUTH-REDIRECT ACL is in the list, as shown in Figure 12-6.
Step 2. Click this access list and ensure that the entries for your environment are there, as shown in Figure 12-7.
Configure ISE for Centralized Web Authentication
When you’re sure the key elements of the network devices are configured correctly, it’s time to ensure that ISE is configured correctly, too. A key change must be made in the authentication policy: An identity source sequence that uses all the appropriate identity stores and the appropriate traffic-filtering dACLs need to be configured. In addition, you need to create the appropriate authorization rules for both before and after Web Authentication.
The sections that follow describe the key steps in configuring ISE for Centralized Web Authentication:
Step 1. Configure MAB Continue for the Authentication.
Step 2. Verify the Web Authentication identity source sequence.
Step 3. Configure a dACL for pre-WebAuth authorization.
Step 4. Configure an authorization profile.
Configure MAB Continue for the Authentication
WebAuth is often used for guest access, which means an endpoint is likely to be unknown to ISE when a guest attaches to the network. It is therefore critical to set the identity options to continue when the MAC address is unknown. This has been the default for MAB since ISE Version 2.0, but we examine it anyway to better understand the situation.
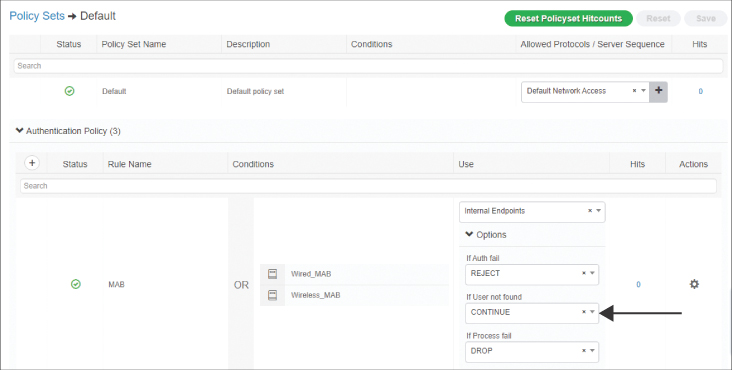
In the ISE GUI, follow these steps (see Figure 12-8):
Step 1. Navigate to Work Centers > Network Access > Policy Sets.
Step 2. Select the Default policy set.
Step 3. Expand the Authentication Policy section.
Step 4. In the MAB rule, click Options underneath Internal Endpoints.
Step 5. Ensure that If User Not Found is set to CONTINUE.
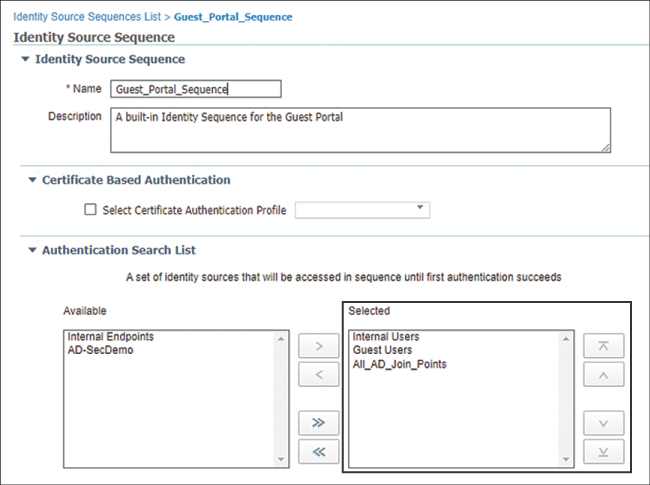
Verify the Web Authentication Identity Source Sequence
There is a preconfigured identity source sequence (ISS) named Guest_Portal_Sequence. The default Web Authentication portal is configured to use this ISS. It is configured by default to check Internal Users, Guest Users, and All_AD_Join_Points—in that order.
There is no configuration change required. This sequence, and all the preconfigured sequences since ISE Version 2.0, are ready to use as is. However, just to be sure it does what you need, in the ISE GUI, navigate to Work Centers > Network Access > Identities > Identity Source Sequence and select the Guest_Portal_Sequence, as shown in Figure 12-9.
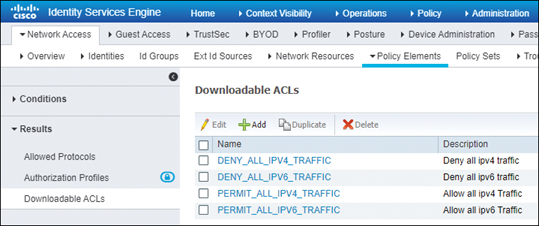
Configure a dACL for Pre-WebAuth Authorization
Before a device can reach the CWA portal, it first has to be permitted onto the network. Full network access is not desirable in most cases. For IOS-based devices, a dACL can and should be used to limit the network access.
In the ISE GUI, follow these steps:
Step 1. Navigate to Work Centers > Network Access > Policy Elements > Results > Downloadable ACLs, as shown in Figure 12-10.
Step 2. Click Add.
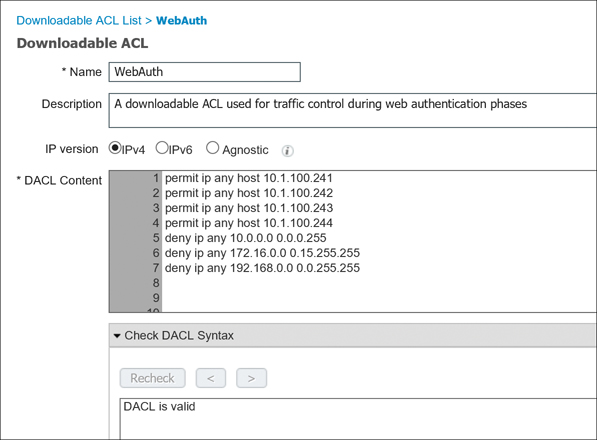
Step 3. Name the new dACL WebAuth.
Step 4. Add a description.
Step 5. Configure the ACL to permit traffic to the ISE policy service nodes but deny access to the remainder of the internal network. Figure 12-11 shows what this might look like.
Step 6. Click Submit.
Configure an Authorization Profile
At this point, you are ready to build the authorization profile to allow the end user onto the network, apply the URL redirection to the default CWA portal with the correct URL-Redirect ACL, and apply the dACL to limit network traffic.
In the ISE GUI, follow these steps:
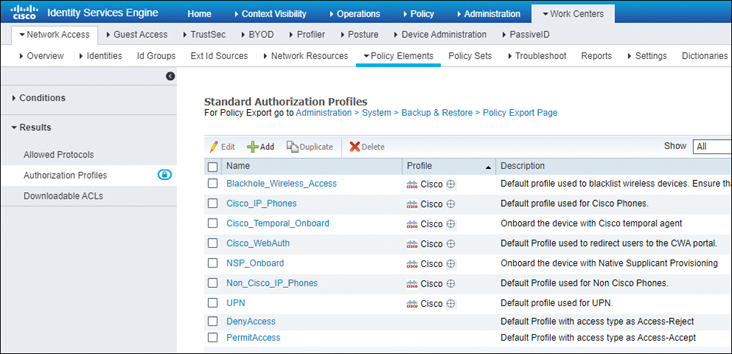
Step 1. Navigate to Work Centers > Network Access > Policy Elements > Results > Authorization Profiles, as shown in Figure 12-12.
Step 2. Click Add.
Step 3. Name the new Authorization Profile CWA.
Step 4. Select the WebAuth dACL.
Step 5. Select the Web Redirection checkbox and choose Centralized Web Auth from the first dropdown. In the ACL text box, type ACL-WEBAUTH-REDIRECT. You are using a default WebAuth portal, so ensure that Sponsored Guest Portal (default) is selected from the Value dropdown.
Figure 12-13 is a composite image that shows all the key parts in one graphic, including the complete authorization profile.
Many organizations implement segmentation with ISE, as it is a security best practice. After all, this is a major use case for ISE and probably a big reason you are reading this book now. With segmentation, users and devices that have an 802.1X supplicant and perform strong authentication should be admitted to the network and kept separate (segmented) from users and devices that have not gone through strong authentication.
If you are going to use VLANs for segmentation, go for it. However, you don’t want to change VLANs on a device that is not using a supplicant unless you absolutely have no other choice.
A supplicant detects VLAN changes and renews its IP address in the new VLAN. Most devices that are not using a supplicant don’t detect that change of VLAN, and they therefore hold on to the wrong IP address, effectively ensuring that the device will be unable to communicate on the network at all.
Some tricks of the trade can be employed here. (Some in the industry like to call it network gymnastics.) Java and ActiveX applets can be used with WebAuth, and you can play tricks with the DHCP scope in the initial VLAN. The DHCP option is one of the better ones, as a lease can be issued for a very short time, such as 5 minutes. The rules of DHCP client behavior dictate that a client will try to renew its IP address at 50% of the lease time (in this case, 2.5 minutes). ISE has a built-in DHCP server for just such use cases.
However, the recommendation from most implementors is to change VLANs only on clients who use supplicants. Therefore, the default VLAN of your switch ports should remain in a common network segment for guest users and the like, while an authorization profile for employees who gain access via 802.1X should include the VLAN change, and an employee who gains access via CWA should land in the default VLAN of the switch.