Software-Defined Networking (SDN)
The catalyst for software-defined networking is largely attributed to Stanford University’s Clean Slate Program in 2008. Cisco was a sponsor of this project, which reimagined what a new Internet would look like if we set aside conventional norms of traditional networks and worked from a clean slate. It was difficult to develop next-generation routing or connectivity protocols if the equipment available was purposely programmed to follow the original conventions. Programmable logic arrays (PLAs) were pretty expensive to test theories, so a more software-based approach was proposed.
What Is SDN and Network Programmability?
Definitions of SDN and network programmability varied among network IT vendors, but some points were generally agreed upon. As illustrated in Figure 10-10, SDN is
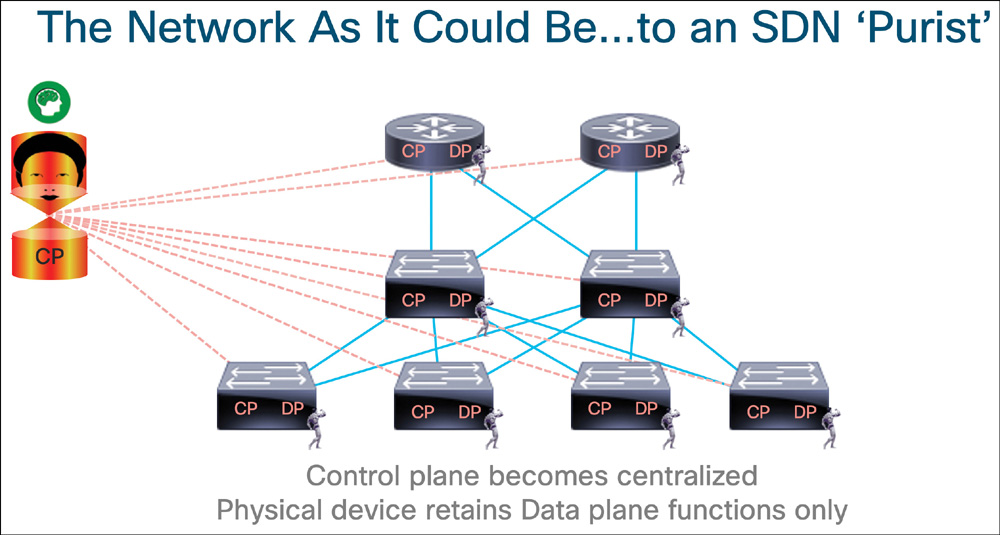
Figure 10.10 The SDN Concept
■ An approach and architecture in networking where control and data planes are decoupled, and intelligence and state are logically centralized
■ An enabling technology where the underlying network infrastructure is abstracted from the applications (network virtualization)
■ A concept that leverages programmatic interfaces to enable external systems to influence network provisioning, control, and operations
Although all of these definitions were exciting and transformative, the last item of leveraging programmatic interfaces appeals mostly to the network programming crowd. The last item also enables us to influence the first two through provisioning and monitoring network assets.
In my talks at CiscoLive, I would share that SDN was
■ An approach to network transformation*
■ Empowering alternative, nontraditional entities to influence network design and operations
■ Impacting the networking industry, challenging the way we think about engineering, implementing, and managing networks
■ Providing new methods to interact with equipment and services via controllers and APIs
■ Normalizing the interface with equipment and services
■ Enabling high-scale, rapid network and service provisioning and management
■ Providing a catalyst for traditional route/switch engineers to branch out
Approach
So, why the asterisk next to an approach to network transformation? Well, it wasn’t the first attempt at network transformation. If we consider separation of the control plane and data plane, we can look no further than earlier technologies, such as SS7, ATM LANE, the wireless LAN controller, and GMPLS. If we were considering network overlays/underlays and encapsulation, the earlier examples were MPLS, VPLS, VPN, GRE Tunnels, and LISP. Finally, if our consideration was management and programmatic interfaces, we had SNMP, NETCONF and EEM. Nonetheless, SDN was a transformative pursuit.
Nontraditional Entities
What about those nontraditional entities influencing the network? As new programmatic interfaces were purposely engineered into the devices and controllers, a new wave of network programmers joined the environment. Although traditional network engineers skilled up to learn programming (and that may be you, reading this book!), some programmers who had little prior networking experience decided to try their hand at programming a network. Or the programmers decided it was in their best interests to configure an underpinning network for their application themselves, rather than parsing the work out to a network provisioning team.
Regardless of the source of interaction with the network, it is imperative that the new interfaces, telemetry, and instrumentation be secured with the same, if not more, scrutiny as the legacy functions. The security policies can serve to protect the network from unintentional harm by people who don’t have deep experience with the technology and from the intentional harm of bad actors.
Industry Impact
The impact to the network industry with operations and engineering was greatly influenced by control plane and data plane separation and the development of centralized controllers. The network management teams would no longer work as hard to treat each network asset as an atomic unit but could manage a network en masse through the controller. One touchpoint for provisioning and monitoring of all these devices! The ACI APIC controller is acknowledged as one of the first examples of an SDN controller, as seen in Figure 10-11. It was able to automatically detect, register, and configure Cisco Nexus 9000 series switches in a data center fabric.
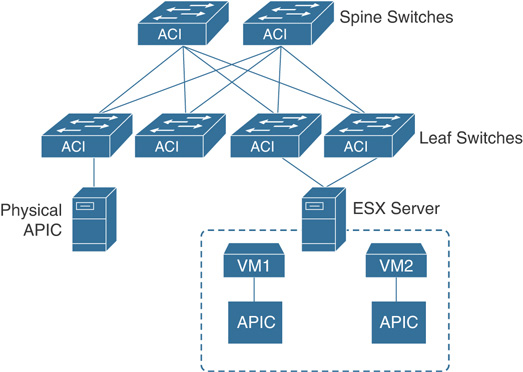
Figure 10.11 Cisco ACI Architecture with APIC Controllers
New Methods
With respect to new methods, protocols, and interfaces to managed assets, APIs became more prolific with the SDN approach. Early supporting devices extended a style of REST-like interface and then more fully adopted the model. First NETCONF and then RESTCONF became the desired norm. Centralized controllers, like the wireless LAN controller, ACI’s APIC controller, Meraki, and others, prove the operational efficiency of aggregating the monitoring and provisioning of fabrics of devices. This model has coaxed the question “What else can we centralize?”
Normalization
SDN’s impact on network normalization is reflected in the increasingly standardized interfaces. While SNMP had some utility, SDN provided a fresh opportunity to build and use newer management technologies that had security at their core, not just a “bolt-on” consideration. Although the first API experiences felt a bit like the Wild Wild West, the Swagger project started to define a common interface description language to REST APIs. Swagger has since morphed into the OpenAPI initiative, and specification greatly simplifies API development and documentation tasks.
Enabling Operations
Network operations, service provisioning, and management were influenced with SDN through the new interfaces, their standardization, and programmatic fundamentals. Instead of relying on manual CLI methods, operators began to rely on their growing knowledge base of REST API methods and sample scripts in growing their operational awareness and ability to respond and influence network functions.
Besides the REST API, other influences include gRPC Network Management Interface (gNMI), OpenConfig, NETCONF, RESTCONF, YANG, time-series databases, AMQP pub-sub architectures, and many others.
Enabling Career Options
Finally, SDN provided traditional network engineers an opportunity to extend their skills with new network programming expertise. The traditional network engineer with years of domain experience could apply that knowledge in an impactful way with these programmatic interfaces. They could deploy more services at scale, with fewer errors and more quickly.
How impactful could SDN be? Let’s consider the early days of IP telephony: it didn’t ramp up as quickly as desired. On one side there were the traditional “tip-ring telco” team members; on the other side was the new “packet-switch” team. IP telephony technology was slow to gain momentum because few individuals crossed the aisle to learn the other side and become change and translation agents for the greater good. When people started to understand and share the nuanced discipline of the other side, then SDN started to make strides.
Network programmability is in that same transition: there are strong network engineers who understand their tradition route/switch technology. Likewise, there are very strong software developers who understand how to build apps and interact with systems; they just don’t have the network domain expertise. As network engineers skill up with the automation and network programming discipline, they bring their experience of networks with them. So, let’s do IT!
Use Cases and Problems Solved with SDN
SDN aimed to address several use cases. The research and academic communities were looking for ways to create experimental network algorithms and technologies. The hope was to turn these into new protocols, standards, and products. Because existing products closely adhered to well-defined routing protocol specifications, SDN was to help separate the current norms from new, experimental concepts.
The massively scalable data center community appreciated SDN for the ability to separate the control plane from the data plane and use APIs to provide deep insight into network traffic. Cloud providers drew upon SDN for automated provisioning and programmable network overlays. Service providers aligned to policy-based control and analytics to optimize and monetize service delivery. Enterprise networks latched onto SDN’s capability to virtualize workloads, provide network segmentation, and orchestrate security profiles.
Nearly all segments realized the benefits of automation and programmability with SDN:
■ Centralized configuration, management control, and monitoring of network devices (physical or virtual)
■ The capability to override traditional forwarding algorithms to suit unique business or technical needs
■ The capability of external applications or systems to influence network provisioning and operation
■ Rapid and scalable deployment of network services with lifecycle management
Several protocols and solutions contributed to the rise of SDN. See Table 10-4 for examples.
Table 10-4 Contributing Protocols and Solutions to SDN
Protocol/Solution |
Definition |
Function |
|---|---|---|
OpenFlow |
Layer-2 programmable forwarding protocol and specification for switch manufacturing |
|
I2RS |
Interface to Routing System |
Layer-3 programmable protocol to the routing information base (RIB); allowed manipulation and creation of new routing metrics |
PCEP |
Path Computation Element Protocol |
L3 protocol capable of computing a network path or route based on a network graph and applying computational constraints |
BGP-LS/FS |
BGP Link-State / Flow Spec |
The ability to gather IGP topology of the network and export to a central SDN controller or alternative method to remotely triggered black hole filtering useful for DDoS mitigation |
OpenStack |
Hypervisor technology for virtualization of workloads |
|
OMI |
Open Management Infrastructure |
Open-source Common Information Model with intent to normalize management |
Puppet |
Agent-based configuration management solution embedded in devices (later updated to agentless) |
|
Ansible |
Agentless configuration management solution |
|
NETCONF |
Network Configuration standard |
IETF working group specification normalizing configuration across vendors using XML schemas (later updated with YANG) |
YANG |
Data Modeling Language |
Data modeling language for defining IT technologies and services |
Overview of Network Controllers
One of the main benefits of SDN was the notion of control plane and data plane separation. You can think of the control plane as the brains of the network: it makes forwarding decisions based on interactions with adjacent devices and their forwarding protocols. The data plane is the muscle, acting on the forwarding decisions programmed into it. Routing protocols like OSPF and BGP operate in the control plane. A link aggregation protocol like LACP or the MAC address table would be representative of the data plane.
The first traditional networks combined the functionality of the control plane/data plane into the same device. Each device acted autonomously, creating and executing its own forwarding decisions. With the advent of SDN, the notion of centralizing that brain function into one control unit yet keeping the data plane function at the managed device was the new architectural goal. These centralized controllers aggregated the monitoring and management function. They oftentimes also provided that centralized forwarding path determination and programming function.
The separation of functional planes also resulted in the definition of new overlay and underlay functionality. Network overlays defined that tunnel endpoints terminated on routers and switches. The physical devices executed the protocols to handle resiliency and loops. Some examples are OTV, VXLAN, VPLS, and LISP.
Host overlays defined that tunnel endpoints terminated on virtual nodes. Examples of host overlays are VXLAN, NVGRE, and STT. Finally, integrated overlays allowed for physical or virtual endpoints in tunnel termination. The Cisco ACI fabric with Nexus 9000 series switches are examples of integrated overlays.
The Cisco Solutions
Cisco has many offerings in the SDN space, the most prominent being the Cisco ACI fabric with Nexus 9000 series switches. Software-defined access (SDA) is enabled by Cisco DNA Center on enterprise fabric-enabled devices. Software-defined wide-area networks (SD-WANs) can be seen in the acquired technologies of Viptela, resulting in the vManage solution for central cloud management, authentication, and licensing.
Network Function Virtualization (NFV) enables cloud technology to support network functions, such as the Cisco Integrated Services Virtual Router (ISRv), ASAv, and vWLC. The Cisco Managed Services Accelerator (MSX) provides automated end-to-end SD-WAN services managed from the service provider cloud.