Cisco Umbrella
Cisco Umbrella is a cloud DNS service. The first question that may come to your mind is “What is the relation with wireless?” Well, many administrators try to secure network access by restricting the content that wireless users can access. This can be done with AVC if you want to target specific applications, but websites are more complicated because you would need to do URL filtering. Solutions exist in the shape of web proxies, firewalls, or content engines, but those indeed have little integration with wireless. First of all, Cisco Umbrella is a very fast DNS server that helps guarantee a very low latency of DNS resolutions and accelerates web browsing. On top of that, because it is cloud managed, it is constantly updated with the latest safety against malware and helps you to not resolve malicious domain names. Simply configuring a client to use Umbrella as a DNS server is enough to provide some protection. On top of that, Umbrella offers an administrator dashboard that allows you to restrict what URLs can be resolved in your network. Without personally choosing to block website X or Y, you can decide to ban all adult-content websites or all websites promoting violence, for example. You can also, of course, add specific sites to be allowed or blocked, as well as add personal URLs that you want resolved (as if it were your private DNS server). Rather than relying on antivirus software analyzing the threats downloaded to your clients, Umbrella prevents your clients from accessing the malicious content, an approach that is much more efficient and secure.
How does Umbrella relate to wireless though? The integration allows you to do two things:
Make sure that your clients use Umbrella as a DNS server.
Allow you to mark the DNS traffic coming from your network toward Umbrella to use specific DNS policies on Umbrella. For example, you may want to allow more websites on your secure employee SSID but block a lot more things on your guest SSID (such as illegal software, movies, and VoD websites).
You must first register your controller to the Umbrella cloud by going to the Configuration > Security > Threat Defense > DNS Layer Security/Umbrella page (as shown in Figure 5-50), where you can create a global umbrella parameter-map in your configuration. You can obtain the token from the Umbrella cloud account and enter it on the controller. You can then enable DNS packet encryption (which means the WLC encrypts the packets it sends to Umbrella) and create parameter maps. Those are just names that you are able to apply to a policy profile to identify requests on the Umbrella cloud site.
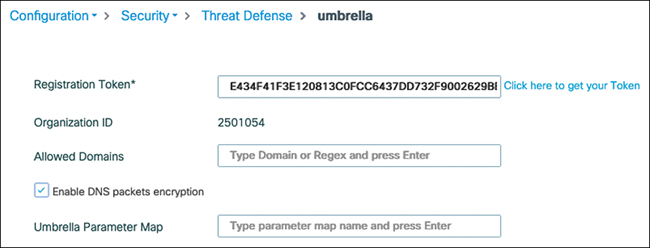
FIGURE 5-50 Umbrella global configuration on the 9800
On the policy profile advanced settings section, you can choose one of the parameter maps you created to segregate DNS policies on the Umbrella cloud. By default, the controller injects the Umbrella DNS IP address into DHCP option 6 (which points to the DNS servers) when the clients receive their IP address so that you don’t even have to configure the Umbrella IPs in your DHCP pools. The other settings depicted in Figure 5-51 allow you to also inject the DHCP option 6 setting in Flex APs when the traffic is locally switched and to force the DNS traffic redirection. This means that even if the client then manually configures a custom DNS server, the WLC intercepts the DNS queries anyway, sends them to OpenDNS, and spoofs the original DNS IP back so that the client doesn’t notice that it’s another DNS server that replied.
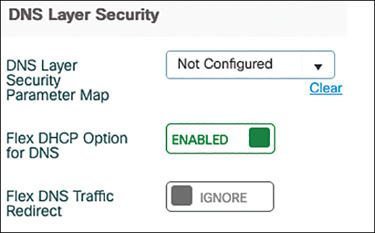
FIGURE 5-51 DNS Layer Security (formerly called Umbrella) section of a policy profile.