Courage is resistance to fear, mastery of fear—not absence of fear.” —Mark Twain
By the end of this chapter, you should know and be able to explain the following:
- Who needs a firewall, and why firewalls are used to protect network resources
- How a firewall is a technological expression of your organization’s written security policy
- When a DMZ is appropriate and the security benefits you gain by deploying a firewall with a DMZ
Answering these key questions enables you to understand the overall characteristics and importance of network security. By the time you finish this book, you will have a solid appreciation a firewall’s role, its issues, how it works, and why it is so important to the security of your network.
The Internet is an exciting and wonderful place to browse and explore. It has been likened to the Wild West, The Great Frontier, and other grandiose achievements of mankind. In reality, the World Wide Web is merely a collection of routers and servers that make up the largest WAN in recorded history. This collection of networking gear provides mail servers, websites, and other information storage and retrieval systems and is all connected to the Internet and accessible to every person who is also connected. It has even been said that the Internet will contain the collective institutional knowledge of mankind, eventually. Entire books have been written on the Internet’s potential and its impact on our lives—rest assured that this is not one of those books. But it does make you ponder just how much of your life is out there already that you might or might not be aware of.
We are concerned with a network’s security, so we must ask what kinds of safeguards are in place to protect such an unbelievable amount of information. Is there some organization that polices the Internet much in the same way that law enforcement cruises the highways? How about a governmental agency that snoops around and double-checks every possible device connected to the Internet? The answer to these questions is no; there is no unifying organization responsible for protecting the Internet.
The job of securing and protecting the gateways of the Internet’s knowledge is left up to the person or persons responsible for the Internet connection and network hardware/software, such as the router, firewall, switch, server operating systems, application, and so on. This person or persons are tasked with the job to ensure that hackers (the bad guys) do not make a mess of the carefully stored and catalogued information in question. And just how can you protect a website, mail server, FTP server, or other information sources accessible from the Web?
The answer is one word—firewall. The sole purpose of these dedicated hardware devices is to provide security for your network. A firewall is a security device that sits on the edge of your Internet connection and functions as an Internet border security officer. It constantly looks at all the traffic entering and exiting your connection, waiting for traffic it can block or reject in response to an established rule. The firewall is the law and protection in the lawless wild wild web. A firewall is ever vigilant in its mission to protect the network resources connected to it.
The Internet has made so much information available to individual users as, over the years, access to this information has evolved from an advantage to an essential component for both individuals and businesses. However, making your information available on the Internet can expose critical or confidential data to attack from everywhere and anywhere in the world—the Internet is literally a worldwide network. This means that, when you connect to the Internet in Madison, Mississippi, you can be subject to attacks from Europe, Asia, and Russia—literally any device connected to the Internet anywhere on the earth, which is kind of disturbing. Firewalls can help protect both individual computers and corporate networks from hostile attacks from the Internet, but you must understand your firewall to correctly use it.
This 24-hour/365-day-a-year “electronic Robocop” has an important job: to keep the bad guys out and let the good guys get to the resources they need to do their jobs. Sounds simple, right? On paper, it sounds like a walk in the park, but in reality, properly configuring a firewall is far from easy.
In some cases, a badly configured or feature-inadequate firewall can be worse than no firewall at all. This is difficult to believe, isn’t it? Nonetheless, it is true. This chapter dissects a firewall’s duties to understand what makes a firewall operate and how it does its job.
Firewall Frequently Asked Questions
Before looking at the overall operation of a firewall, the following sections examine and answer some of the fundamental questions about them.
Who Needs a Firewall?
This is perhaps the most frequently asked security question. If you plan to connect to the Internet, you need a firewall. It does not matter whether you connect from home or your company connects—you need a firewall, period! The increased penetration of broadband Internet services to the home and their always-on Internet connections make home security even more important.
Why Do I Need a Firewall?
You read about security threats in the papers or hear about them on the evening news almost every day: viruses, worms, denial-of-service (DoS) attacks, hacking, and new vulnerabilities to your computer. For example, Code Red, Slammer, and other threats/vulnerabilities. are changing with the prevalence of malware and botnets.
It is no secret that hackers are out there, and they are out to get you. Often, you do not know who they are, but you do know where they are and where you do not want them to be (in your network). Like pirates of old who roamed the seas, hackers freely roam the open expanses of the Internet. You do not want them to enter your network and roam among the computers that connect to it, and that is where a firewall becomes a requirement.
You know that you must protect your network from these attackers, and one of the most efficient methods of protecting your network is to install a firewall. By default, any good firewall prevents network traffic from passing between the Internet and your internal network. This does not mean that the firewall can stop all traffic—that defeats the purpose of being on the Internet. It does mean that the firewall is configured to allow only web browsing (HTTP/port 80) to access it from the Internet. Along the way, the firewall provides Stateful Packet Inspection (SPI) rules to every incoming packet (as discussed previously in Chapter 2, “Security Policies.”)
The alternative to having a firewall is allowing every connection into your network from anyone, anywhere—there wouldn’t be any sort of packet inspection to determine whether an attack is hidden within one of the incoming packets. Not having a firewall is ill-advised and will make your organization wide open to everyone on the Internet.
Do I Have Anything Worth Protecting?
I often hear people say, “I understand that if I had something worth protecting, I would definitely need a firewall. However, I do not have anything an attacker would want, so why should I worry about a firewall?”
Networks and their resources are important to the way our society conducts business and operates. In practical terms, this means that there is value to your network and having it effectively operate. This increased role of networks means that you definitely have something worth protecting to some degree, as documented in the following list:
Downstream liability: This sounds like a confused Bassmasters fishing show title, but it is perhaps the next big step in the legal evolution of the Internet. Downstream liability involves allegations that an attacker has taken control of a target computer (yours) and used it to attack a third party. Assume that it is your company’s computer that has been compromised by a hacker. Your company’s failure to protect its own systems has resulted in the damaging of a third party; the attacker used your computer as a weapon against the third party. Your company is therefore negligent due to lack of due diligence because it failed to protect against reasonable risks—specifically, no firewall was in place, or it was improperly configured, which is just as bad.
The prudent person’s responsibility for security here is to use reasonable care. You can find a more detailed definition in Prosser, Wade, and Schwartz’s Cases and Materials on Torts: “...requiring the actor to conform to a certain standard of conduct, for the protection of others against unreasonable risks.” Who says Hollywood liberalism doesn’t contribute to society?
- Lost data: You have probably heard the stories of companies that lost all their business data in hurricanes such as Katrina or the September 11 attacks, and many companies did not recover. What if your company experienced the same loss of data because you did not have a firewall and an attacker deleted your data because he could? What would happen to your business? Would it cost money to re-create everything? Would you suffer lost sales? Would you still be employed the next day?
- Compromise confidential data: Every organization has data it considers confidential and, if lost, might cause financial problems, legal difficulties, or extreme embarrassment. These things might be caused by the loss of customer information such as credit card numbers, secret plans for the new weight loss formula, or secret product plans that end up in the hands of a competitor. The list goes on, and when you have been hacked, you must assume the worst. Perhaps this is why most cybercrimes go unreported—it is embarrassing, and admitting to being hacked is a sign of weakness that could affect the reputation and brand of a company.
- Network downtime: Have you ever gone to an ATM machine or a grocery store to get cash and paid with your cash card in the swipe card readers? The networks enabling these devices to operate usually work fine; however, if they were not protected, an attacker might cause them to go down. The loss of revenue from these networks can quickly grow if they are unavailable. Downtime is the bane of any network, and a cost is always associated with these types of events.
Ultimately, everyone has something worth protecting, and failure to do so is ill-advised; it is just a matter of time before something happens. The next question is, “What does a firewall do to protect my network?”
What Does a Firewall Do?
A firewall examines traffic as it enters one of its interfaces and applies rules to the traffic—in essence, permitting or denying the traffic based on these rules. Figure 7-1 shows a firewall filters both inbound and outbound traffic.
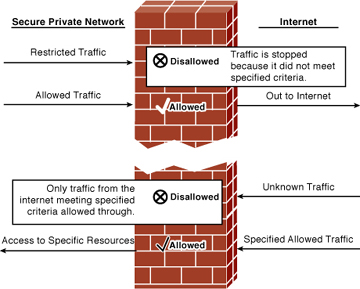
Figure 7-1 Firewall in Operation
Firewalls use access control lists (ACLs) to filter traffic based on source/destination IP addresses, protocol, and the state of a connection. In other words, normally you might not allow FTP/21 into your network (via the firewall), but if a user inside your network begins an FTP session out to the Internet, it is allowed because the session was established from inside the network. By default, firewalls trust all connections to the Internet (outside) from the trusted internal network (inside).
A firewall can also log connection attempts with certain rules that might also issue an alarm if they occur. Finally, firewalls enable you to perform Network Address Translation (NAT) from internal private IP addresses to public IP addresses. The section “Firewall Operational Overview” discusses the roles of a firewall; however, here you can tie the firewalls back to Chapter 2’s security policy discussions by examining how a firewall enforces your security policy.