SOC Conceptual Architecture
To get the best out of your investment, you should operate the various SOC technologies under a cohesive architecture. The architecture should formalize the operation model of SOC in terms of components and relationships.
We propose a reference conceptual architecture in Figure 2-13. The proposed reference architecture formalizes the following:
- The input to the SOC in terms of categorized sources
- The output of the SOC in terms of alerts and actions
- The SOC’s technologies
- The relationship between the technologies
- The areas where measurements can be collected in terms of type, value, and frequency
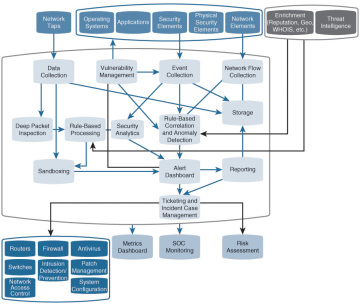
Figure 2-13 SOC’s Conceptual Architecture
We will refer to this architecture and detail its different blocks in various chapters of this book. One other architecture to consider is looking at how SOC responsibilities could be outsourced to a managed service provider. Figure 2-14 represents the Cisco architecture for managed threat defense services targeting customers looking to outsource some or all of their SOC responsibilities.

Figure 2-14 Cisco Managed Threat Defense Architecture