As security threats in the wild continue to advance in capabilities, demand increases for organizations to develop a Security Operations Center (SOC, pronounced sock). Relying on basic security solutions such as firewalls and anti-virus software is not good enough; this minimal approach is equivalent to protecting a bank merely by locking the front door. Cyber security requires layers of defenses, similar to how a bank protects valuables with a security strategy that includes cameras, guards, safes, and other measures beyond locking the front door. Layering cyber security solutions requires somebody to be responsible for enabling and maintaining security, which leads to the demand for a SOC.
Starting the SOC Conversation
The biggest challenge in starting the conversation about the need for a SOC is justifying the cost to people who don't understand the threat landscape or the value of being proactive rather than reactive about security. According to the 2015 Verizon Data Breach Investigation Report, "In 60% of cases, attackers are able to compromise an organization within minutes," and "75% of attacks spread from Victim 0 to Victim 1 within one day (24 hours)." Waiting to react to a breach until after damage has been done will most likely lead to an extremely costly recovery. We have all seen in the news the amount of money lost from data breaches. Showcasing a few data breach examples from a source such as DataLossDB will surely make your point.
One way to help justify the SOC budget is by posing the following questions to the organization's leadership:
- How can you detect a compromise?
- How do you judge the severity of the compromise?
- What is the impact of the compromise to your organization?
- Who is responsible for detecting and reacting to a compromise?
- Who should be informed or involved, and when do you deal with a compromise once it is detected?
- How and when should you communicate a compromise internally or externally? (Note that sometimes engaging the authorities is required by law.)
These questions are designed to make the organization's leadership think about the impact of an incident and judge their existing cyber security capabilities. Many organizations find that they need to develop a better incident-response plan—one that requires a group within the organization to be responsible for it. That group should be the SOC.
Five major steps are involved in developing a SOC:
- Planning the SOC.
- Designing the SOC.
- Building the SOC.
- Operating the SOC.
- Reviewing the SOC.
The following sections review the actions required in each step of SOC development.
Step 1: Planning the SOC
Planning starts by assessing your existing security capabilities for people, processes, and technology. This approach allows you to establish a baseline that can be compared to the objectives for the future SOC. This strategy is required for new SOCs as well as existing SOCs that want to improve their capabilities.
The assessment methodology should follow these steps:
- Identify the SOC business and IT goals.
- Identify the capabilities to be assessed, based on the SOC goals.
- Collect information related to people, processes, and technology capabilities.
- Analyze the collected information and assign maturity levels to the assessed capabilities.
- Present, discuss, and formalize the findings.
Figure 1 showcases this process.
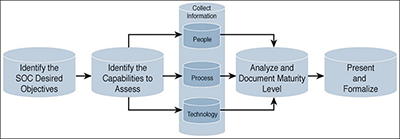
Figure 1 Assessment methodology. (For more information, see Chapter 3, "Assessing Security Operations Capabilities," in Security Operations Center: Building, Operating, and Maintaining Your SOC.)
The idea is to first establish business goals of the organization, so that anything developed will matter to the leadership sponsoring the SOC. The next step is to list capabilities that map back to the business goals that were identified in the first step. Capabilities include existing people, processes, and technologies. Maturity levels are established for each capability, which in turn will align with a business goal so that gaps can be prioritized for developing a plan to build the future SOC. That plan is debated and eventually solidified by all parties responsible for developing the SOC.
The second part of the planning phase is developing your SOC strategy, which is made up of the following items:
- SOC mission statement
- SOC strategic goals
- SOC scope
- SOC model of operation
- SOC services
- SOC capabilities-development roadmap
- SOC key performance indicators (KPI) and metrics
An inadequate or inaccurate SOC capabilities assessment will produce a weak SOC strategy that does not align to the goals of the organization. Do not skip or rush the assessment step, and make sure that you complete all strategy items before moving into the next phase.
The planning phase should determine the model of operation for the future SOC: Physical, virtual, or hybrid? The planning phase will also identify the type of services that the SOC will provide, indicate whether the SOC is responsible for the entire network or a subset of the network, and specify the details of those services.
Steps 2–3: Designing and Building the SOC
Once the planning phase is complete, the next step is designing the SOC. The designing and building steps are almost inextricably linked, and technology selection is a major part of both phases for the future SOC. One important focus is how the SOC will collect data. Typically this task is accomplished using a centralized data-collection tool such as a security information and event management (SIEM) solution. Other security tools such as firewalls, content filters, intrusion detection/prevention systems, and so on will export events to the SIEM, enabling the SOC analysts to evaluate all events to get a bigger picture of the current security status of the organization. Figure 2 shows an example of a mature SOC with layered security, network segmentation, and monitoring technologies.
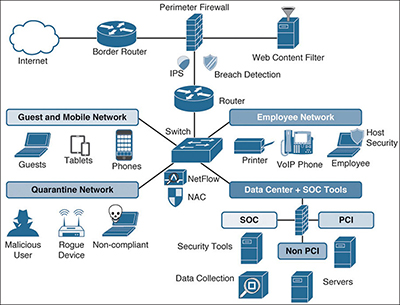
Figure 2 Example of mature SOC architecture. (For more information, see Chapter 9, "The Technology," in Security Operations Center: Building, Operating, and Maintaining Your SOC.)
There are many flavors of security technologies; however, best practice involves making sure that the approach you choose leverages layered capabilities, so that if a defense measure fails to detect an attack, another measure is available to help prevent the attack. Having multiple vendor firewalls aligned back-to-back doesn't provide much additional security, since all firewalls will probably have the same ports open. Having both an intrusion-prevention system (IPS) and anti-virus software is good, but both technologies are signature-based and probably will detect (and miss) similar threats. A better approach would use layered defense/detection capabilities such as the following:
- A content filter that is aware of malicious web sources
- IPS to detect attacks
- Breach-detection technology looking for unknown threats missed by the IPS
- A tool (such as NetFlow) that baselines the network and then monitors it for unusual data trends
Figure 3 shows an example of technologies designed to address different parts of the attack continuum.
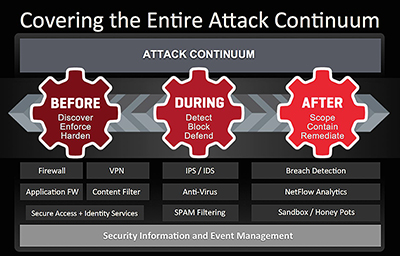
Figure 3 Attack continuum with related security technologies.
Security defenses must expand across all areas of the network. If you don't provide the same level of security for the various parts of your network, the least-protected area will most likely be targeted by malicious parties for attack. Some design areas to include are securing the network edge, mobile devices, user desktops, branch offices, and the datacenter.
To address identifying and securing the weakest link in an organization, the SOC should include vulnerability management capabilities. The extent of these services should be outlined in the SOC services planning; however, typically it includes dealing with the vulnerability management lifecycle, as shown in the SANS vulnerability management model in Figure 4.

Figure 4 SANS vulnerability management model. (For more information, see Chapter 2, "Overview of SOC Technologies," in Security Operations Center: Building, Operating, and Maintaining Your SOC.)
Technology required for the vulnerability management lifecycle can include assessment tools that identify and qualify vulnerabilities (such as Nessus, OpenVAS, or Metasploit), as well as different approaches to calculate how much risk is associated with the threat, in order to determine how to mitigate, transfer, accept, or avoid the vulnerability. It is also important to have an automated inventory-assessment tool so the SOC is aware of all existing assets and their current risk to the organization. Without this information, some assets may not be evaluated by the SOC, possibly exposing the organization to unknown risk.
Once the design is finished, the last area to consider before moving to the operation phase is assessing the people. This can be the most challenging part of this step, since today's job market continues to have more jobs available than qualified people to fill them. This situation also makes retaining talent challenging, because SOC jobs can be very demanding and repetitive, and often require extended hours. Effective process and procedures can assist with maintaining consistent services as job roles change hands; however, too much involvement in process and procedures can negatively impact the SOC operation by pigeonholing top performers.
Step 4: Operating the SOC
Once the SOC is built, it is time to move into the operation phase, also known as the "go live" phase. It is critical that the new SOC overcome some key challenges before the go-live date:
- First, it is important to validate that the SOC still has executive sponsorship. In many cases, a large gap of time passes between the initial signoff from leadership to build a SOC to the point when the SOC is actually ready to operate.
- Processes will be challenging, since some will be new and need to be tested.
- Technology needs to be checked to ensure that everything is functioning properly.
- Training may be needed for team members who are responsible for using and maintaining the solutions.
Moving through each step from building to operating a SOC requires a well-managed transition plan. Successful transition plans tend to share some common success factors:
- Success criteria are explicit and clear. A simple checklist of success criteria should be negotiated with the sponsors as part of the design, and this list should form the basis for managing expectations and execution.
- Resourcing is detailed and well structured. Resources may refer to people, time, or money. It should be very clear how and when each resource is expected throughout the project or program.
- Requirements for skills, technologies, deliverables, and content are clear and achievable. Your team has to be sufficiently skilled by the go-live date to do the work. Required technologies, deliverables, and content have to be in place, according to specific requirements set during the planning and design phases.
- Simple checks can be performed to verify that a goal has been completed successfully. A simple checklist should be developed that clearly outlines how the results of each activity, task, or milestone will be evaluated.
Step 5: Reviewing the SOC
Once the SOC has gone live, the final phase is reviewing how successfully the SOC is operating, as well as identifying areas of improvement. Reviewing your SOC is not very different from reviewing any other critical and costly business function. The following five-step method works well to develop a report that can be used for updating leadership on the current state of the SOC:
- Determine the review's scope. This can include all aspects of the SOC as part of a comprehensive review, but it is often more helpful to limit the scope to focus on particular areas.
- Determine participants. You need to understand who will perform and participate in the review. The specific participants may depend on the scope of the review.
- Establish a clear methodology. You need a clear methodology to guide any review, along with expected outcomes and deliverables based on a predetermined template.
- Determine frequency. Decide how frequently to perform such reviews. Certain types of reviews may or should occur more often. For example, performing frequent post-incident reviews within the first 72 hours of an incident is recommended, so that the people involved don't forget specific events associated with the incident.
- Prioritize results and action items. Any areas for improvement and related action items need to be prioritized, executed, and followed up to ensure that necessary changes are completed.
The SOC should continue to work at improving key performance indicators (KPIs) for capabilities that align with business goals, in order to judge whether services are performing at expected levels. SOC leads should target KPI goals for each capability category created during the design phase related to specific timeframes such as quarterly reviews. Failure to meet goals could indicate a need for more people, processes, or technology.
Final Thoughts
With all these requirements, it is easy to see why SOCs might fail to fulfill their initial promise. No SOC is perfect, but a healthy SOC can evolve for the better. Efforts to maintain, review, and improve your SOC are fundamental to its long-term viability. Remember, running a SOC is a journey, not a destination.